Ever pondered upon the intricacies of how a program shields itself from replication? With the appropriate tools, you can dissect the internal mechanisms of a program and delve into the realm of reverse-engineering. A solid command over assembly programming and hexadecimal coding is imperative to embark on this journey, along with a disassembler application. Once you're acquainted with the code, you can tweak the DLLs, rendering the associated programs exempt from registration or purchase.
Steps
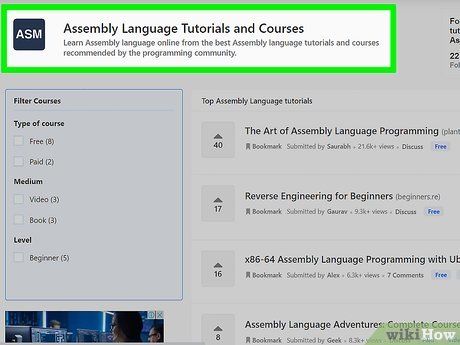
Master Assembly Programming and Hex Code Manipulation. A proficient understanding of assembly is essential for cracking most software. Assembly, being a low-level programming language, is intricately linked with machine language, with each assembly language being computer-specific. The majority of assembly language is communicated through binary and hexadecimal representations.
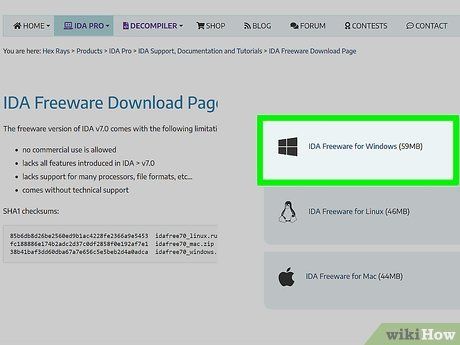
Deploy a Disassembler. To analyze and modify DLLs, you'll require an array of tools, including a disassembler. Consider utilizing IDA Pro, renowned for its capabilities in disassembling and debugging. While a free version is available from https://www.hex-rays.com/products/ida/support/download_freeware, it offers limited functionality compared to the Pro version. Alternatively, explore dotPeek, a DLL-compatible decompiler that translates .NET assembly code into C#. Another viable option is OllyDBG, enabling you to access DLL files free of charge.
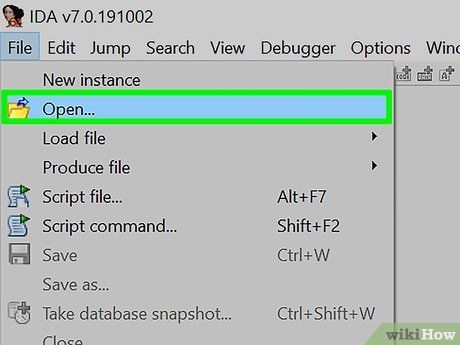
Access the application you aim to crack using your disassembler. The procedure varies slightly depending on the disassembler you employ. This step reveals the DLL files loaded by the program. Utilize the debugger to inspect the functions invoked from the DLL.
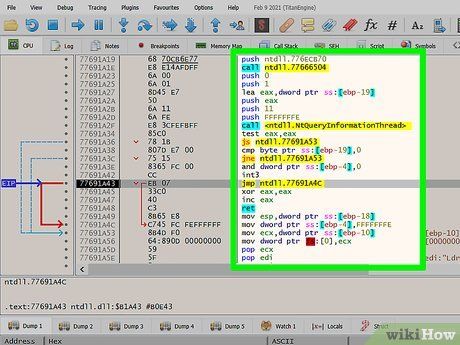
Locate the timer function. Many applications employ a timer for anti-copy measures, barring access once the timer expires. The objective is to identify this timer code and then circumvent it.
- If the targeted program adopts an alternative protection method, focus your search accordingly.
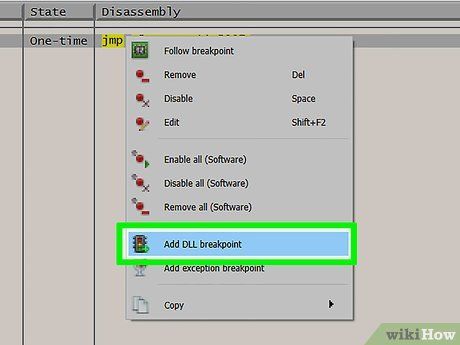
Set a breakpoint on the timer. Upon pinpointing the timer function, configure your disassembler to pause execution upon encountering it. This enables scrutiny of the code execution at the moment the timer function is invoked.
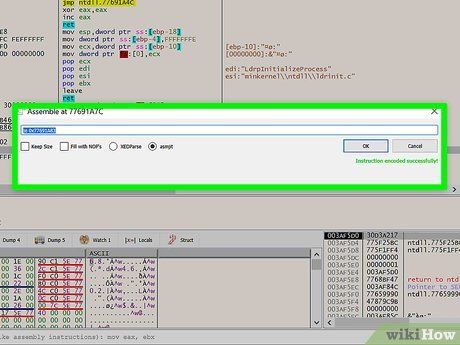
Modify the timer code. Having located the timer function's code, you can alter it to prevent the timer from triggering the program lockout. For instance, you could modify the code to prevent the timer from reaching the lockout threshold or bypass the timer entirely by redirecting program flow.
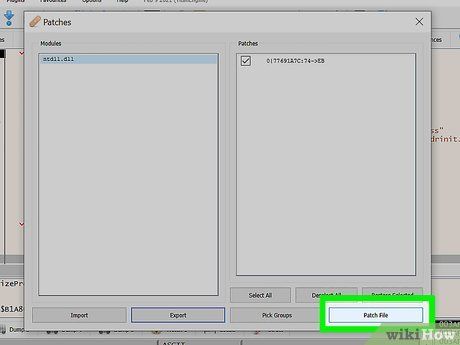
Recompile your cracked application. Following disassembly and modification, compile the revised version of the program to ensure changes propagate to the DLL files and other dependencies.
Insights
Alerts
- Engaging in software piracy is against the law, so proceed at your own risk.
- Most software cracking activities are illegal.
