The Default Spell Check Feature on Google Chrome and Microsoft Edge Falls Short

For More Effective Spell Checking, Consider Google's Chrome's Enhanced Spellcheck and Microsoft Editor
Information Theft via Spell CheckThere Have Been Many Doubts Raised About the Operation Mechanism of Google and Microsoft's Spell Check Tools
The information collected by the spell check tool extends beyond regular text messages to include personal details such as names, addresses, emails, birth dates, contact information, and, more dangerously, passwords and payment details.

To demonstrate the tool's nature as an 'information thief,' Josh Summitt, co-founder and director of the security company otto-js, monitored the behavior of these spell check tools through the company's script.
Through otto-js's tool, Summit discovered that clicking the 'Show password' button on certain login pages sent password data through the company's data management system and cloud infrastructure.
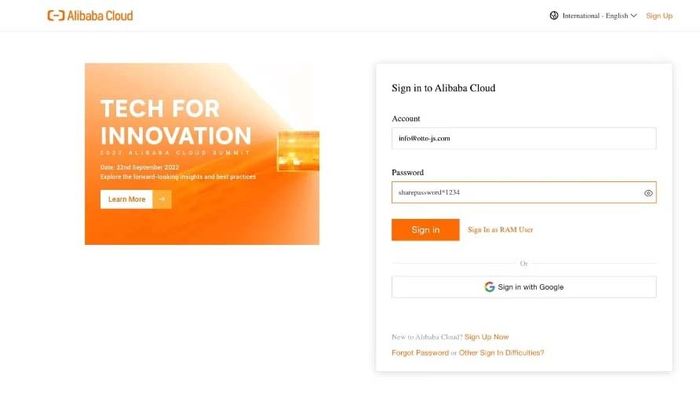
Below is an Alibaba Cloud login account in the Google Chrome browser. The password was visible, and the tool found that the password data was transmitted as text to googleapis.com.
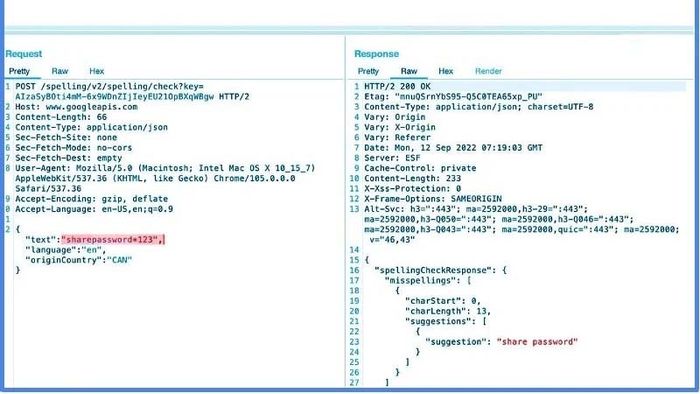
Furthermore, Bleeping Computer verified the data taken by Google's spell check tool on other major foreign websites through Google Chrome such as:
- CNN, Facebook - account and password information taken, with passwords only 'viewed' when the 'Show' button was clicked.
- Bank of America (Major US Bank), Verizon: Only username information taken.
Depending on different websites, the spell check tool decides which information to collect. However, it's challenging to know with absolute certainty which websites are affected.
Website owners can alleviate concerns with just one basic HTML commandAlthough web data exchange is secured by HTTPS protocol, users' personal data isn't protected in this case as it involves a third party, Google. Websites with URLs starting with https have SSL certificates, ensuring encryption between their server and the browser.
However, with spell check tools, SSL protocol only encrypts data between the website (e.g., CNN) and the browser (e.g., Google Chrome), leaving data sent to Google's or Microsoft's spell check servers unencrypted, making user information easily exploitable.
From the user's perspective, we can enhance information security by disabling deep spell check on Google Chrome or uninstalling the Microsoft Editor extension. As for website owners, they can prevent spell checkers from reading passwords by adding the 'spellcheck='false'' attribute to HTML input fields for usernames, passwords, etc., to protect user information.
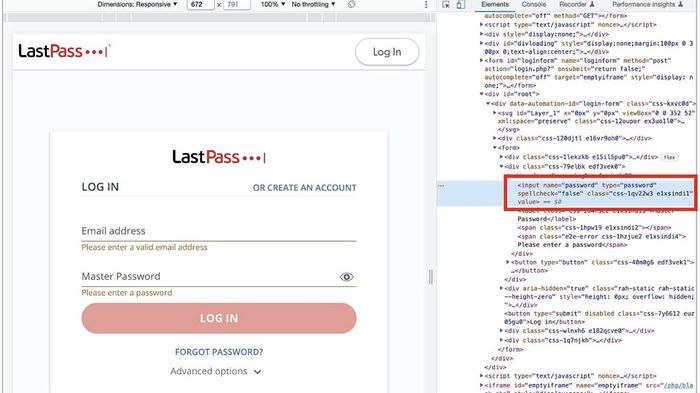
If you're a user with basic HTML knowledge, you can also use the Inspector tool in Chrome or Edge to find and add the mentioned code to password input fields to temporarily disable spell check. However, this method is somewhat cumbersome as it requires manual input, whereas disabling spell check is quicker.
Interim ConclusionPerhaps internet users like us all know that achieving 100% information security is impossible. Especially with major software providers like Microsoft, Google, Amazon,... They might have access to passwords and personal information through means other than spell checks. But as users, we should protect our information to the best of our ability, actively preventing leaks before any regrettable incidents occur.
- Explore more articles in the Discover section
