Living in an area flooded with Wi-Fi signals can raise concerns about the vulnerability of your printer and files to unauthorized access. While completely disconnecting from the Internet is the ultimate solution, this guide offers alternative methods to safeguard your devices, including installing a Firewall and blocking file-sharing programs.
Follow These Steps
Disabling File and Printer Sharing
Prevent sharing your printer with other users on the network. Your printer might be accessible to others without your knowledge. Disable printer sharing through your system settings to enhance security.
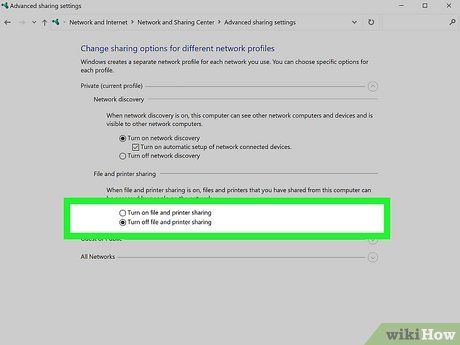
- Windows: Navigate to the Control Panel, select Network and Internet, then Network and Sharing Center. Access Change advanced sharing settings and opt to Turn off file and printer sharing.
- macOS: Click on the Apple menu, then System Preferences… > Sharing. Deselect the 'Printer' option to cease printer sharing.
Review your network's file sharing settings. If file sharing is enabled on your PC or Mac, other devices on the same network may access your files. To disable file sharing:
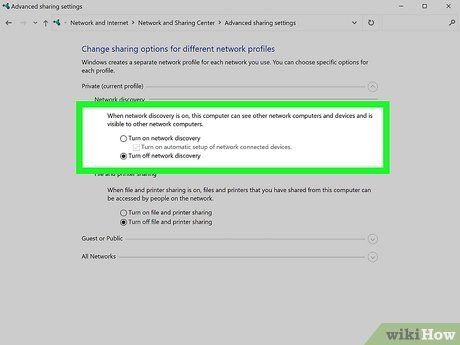
- Windows: Turning off printer sharing in the Network and Sharing Center also disables file sharing in Windows 10 and 11. Additionally, make your PC undiscoverable in Control Panel > Network and Internet > Network and Sharing Center by selecting Turn off network discovery.
- macOS: Navigate to the System Preferences… menu via the Apple logo, then choose Sharing. Uncheck 'File Sharing' to stop sharing all files, or manage access for specific users in 'Users & Groups'.
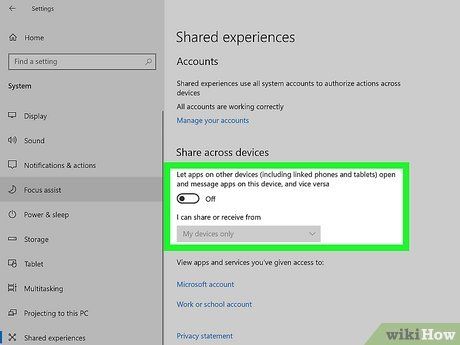
Disable Nearby Sharing in Windows. Windows 10 and 11 offer a feature called Nearby Sharing, enabling file sharing with nearby users. To disable this feature:
- Windows 10: Go to Settings > System > Shared experiences and set it to Off.
- Windows 11: Navigate to Settings > System > Nearby Sharing and switch it to Off.
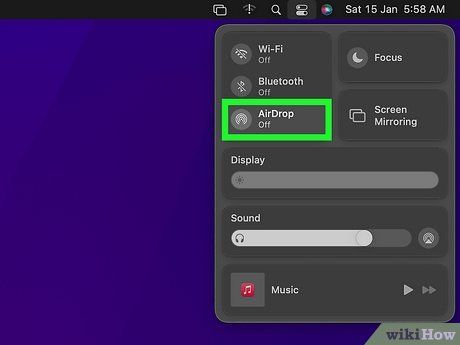
Deactivate AirDrop on your Mac. AirDrop allows wireless file transfers to your Mac from nearby devices. To turn off AirDrop:
- Click the Control Center icon (two sliders) at the top-right corner of your screen.
- If the AirDrop icon is blue, click it to disable AirDrop.
Performing a Malware Scan
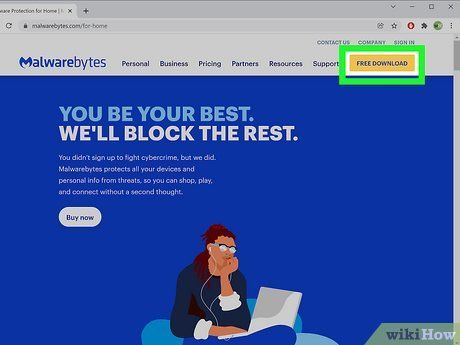
Select an anti-malware tool. With numerous options available, opt for a program that suits your needs. While many are free, paid versions offer enhanced security features. All anti-malware tools can conduct scans to identify potential threats. Advanced programs may allow custom scans.
- Ensure your chosen tool scans registry objects, where hacker activities first appear. Memory, startup, filesystem, and heuristic areas should also be scanned.
Install the program. Ensure compatibility with your computer and system model. Review prerequisites before downloading. If unrecognized, it likely doesn't match the prerequisites.
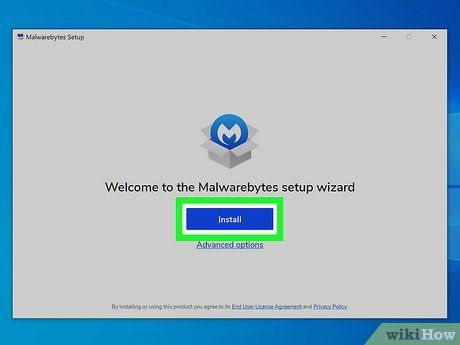
- Locate the program via disk or downloads. Double-click to launch.
- Choose language and accept terms.
- Select installation directory. Default locations are typically chosen.
- Proceed with installation, opting for a desktop icon if desired. Confirm to complete installation.
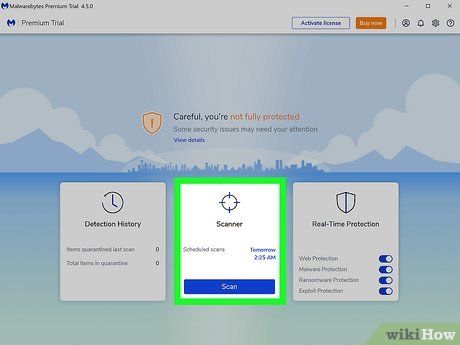
Conduct a threat scan. Open your anti-malware program and click “Scan” on the home screen. Opt for the Threat Scan for comprehensive malware detection.

Initiate the scan. Select the desired scan type and click 'Scan Now.' Monitor progress as the scan may take some time.
- Pause the scan anytime by clicking the button on the progress screen.
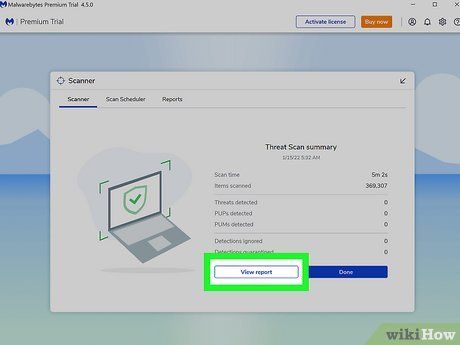
Review scan results. A clean scan indicates no detected threats. If threats are found, assess their severity and decide on removal.
- Most anti-malware tools categorize threats by severity. Remove malware and potentially harmful items to safeguard your computer.
- Select desired items for removal and click “Remove Selected.”
- Once removed, the scan confirms quarantine.
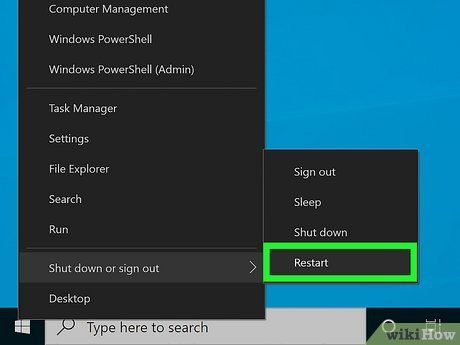
Restart your computer. To finalize threat removal, restart your computer. Delaying will prompt regular reminders.
Utilizing a Firewall
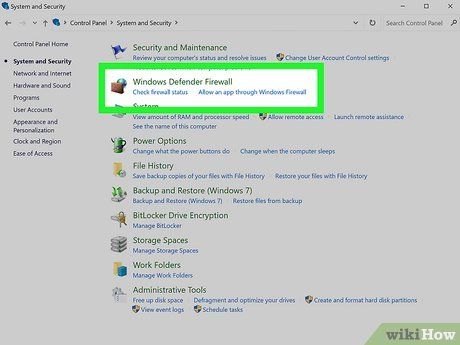
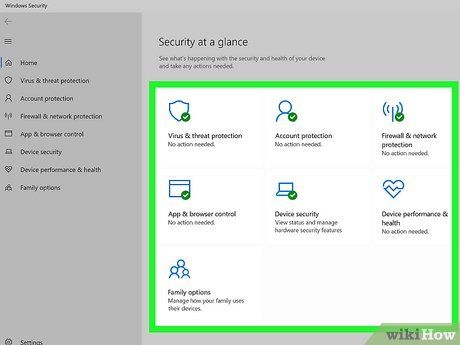
Activate Windows firewall. A firewall serves as a network security tool, overseeing incoming and outgoing network traffic to thwart hackers, viruses, and worms attempting to breach your system via the Internet. Since 2001, Windows has integrated firewall protection into its program to safeguard against external threats.

Install a third-party firewall. Complement your built-in firewall with a third-party option to fortify protection against local programs misusing your network connection. Various no-cost firewalls are available for multiple PCs, such as Kerio Personal Firewall 2, Outpost Firewall Free, Sygate Personal Firewall 5.1, and Zone Labs’ ZoneAlarm 3.7.
- These can be easily found online by searching their names, with the free download option accessible from each program's homepage.
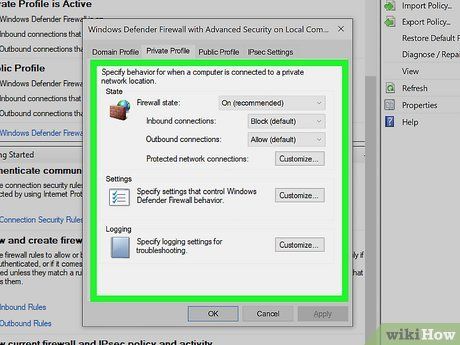
Prevent network browsing. Modify your firewall's default setting to prevent other PCs on the same network from browsing while ensuring they cannot access your files and printers. Right-click the firewall’s system tray icon and:
- Select options, then Network Neighborhood.
- Choose your connection interface from the dropdown list.
- Uncheck the box next to “Allow others to share my files and printer(s),” then click OK.
- With these settings, your computer is secured from both local and external threats.
Restricting Java
Turn off Java. Initially designed to streamline program execution across Java-compatible platforms, Java has become a favored target for hackers. Unless essential, it's advisable to disable Java to mitigate security risks.
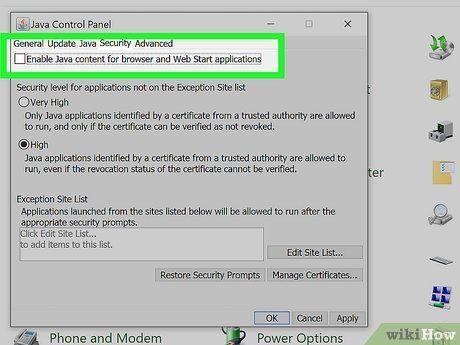
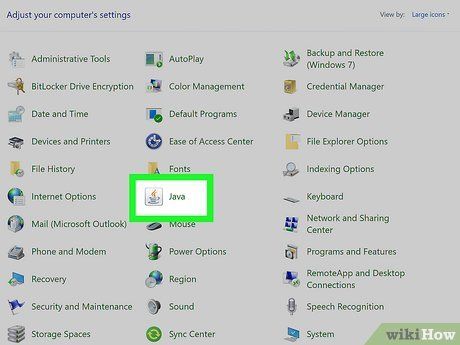
Access your control panel. Locate and launch the Java application (depicted as a steaming coffee mug). Within the app, navigate to the “Security” tab:
- Locate the checkbox labeled “Enable Java content in the browser.”
- Uncheck the box and click OK to confirm the Java deactivation.
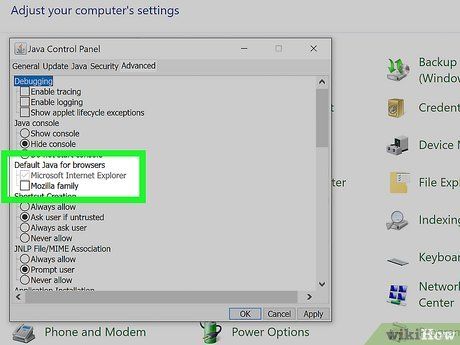
Restrict Java to a single browser. If Java is indispensable for work or specific applications, confine its usage to one browser. Within the Java app, access the “Advanced” tab and locate “Default Java for browsers.”
- Expand the list to view your browsers and select the ones where Java should run by checking the corresponding boxes.
Adjusting Router Configuration
Enhance security protocols. Fortify your computer's defense against Wi-Fi-based intrusions by modifying router security settings. Regularly update your router to shield against known vulnerabilities.
- Ensure your router firmware is up-to-date to safeguard against potential exploits.

Locate the “Wireless Security” section. Access your wireless settings and navigate to the tab labeled “Wireless Security.” Avoid selecting the tab labeled “Security,” as it pertains to other configurations. If you haven't set a password yet, establish one here:
- Ensure your password is robust, incorporating non-dictionary terms, special characters, and numerical digits.
- Keep a record of this password in a secure yet memorable location.
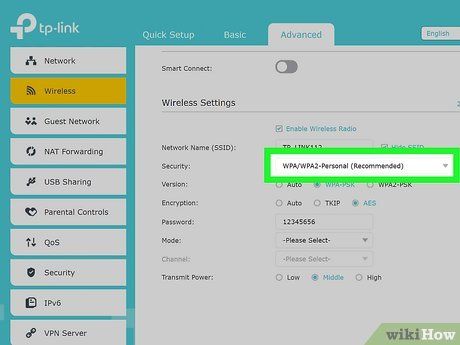
Adjust your security protocol. Look for the dropdown menu adjacent to “Security Mode.” Opt for WPA2 Personal from the menu. Compared to the standard WEP protocol, WPA2 Personal offers enhanced security against intrusion attempts.
Helpful Suggestions
Important Notices
- While confining Java to a single browser mitigates risks, your computer remains vulnerable to potential threats.
- Ensure your network's safety—avoid connecting to unfamiliar WiFi networks, and utilize a robust password for your home WiFi network.
