A hacked mobile phone is a situation where the device is illegally infiltrated/tracked to control accounts and steal critical personal information. This threatens the security of user data every time they log into social media sites, banking apps, or make calls and send texts. Recognizing early warning signs and applying appropriate measures is the key to successfully thwarting such intrusions. Let's delve deeper into this topic with Mytour!
1. Causes of phone hacking
Below are some of the most common reasons your phone becomes a target for hackers:
1.1. Active Agents
+ You've downloaded apps of unknown origin, rampant across the internet.
+ Users click on pop-up ads (small dialog boxes that automatically appear when users visit a certain website) to receive rewards or make purchases.
+ Accessing unlicensed, illicit websites.
+ Previously paired your phone with USB devices of unknown origin, or connected devices to public Wifi.
1.2. Passive Agents
+ Users inadvertently click on links containing viruses or malware.
+ Unregistered SIM cards are easily exploited by hackers to steal information.

There are numerous reasons why a phone might be compromised, such as insecure SIM cards, users accessing unfamiliar links/apps, and connecting to public Wifi/3G networks...
2. How to Detect if Your Phone is Hacked?
Early detection of phone intrusions helps you prevent data theft and loss. Here are the most common signs to look out for:
2.1. High Battery Temperature
Typically, when a phone is hacked, hackers initiate the execution of several background apps to transfer all data to their secret storage system. This sudden activity causes the phone to heat up, even if you weren't using any heavy apps or charging the device before.
2.2. Phone Drains Battery Faster Than Normal
Continuous background app execution also leads to accelerated battery drain, resulting in faster-than-normal usage time reduction. To check the maximum battery capacity and compare it with previous periods, follow these steps:
+ For genuine iPhone devices: Go to Settings > Battery > Battery Health & Charging > Check information under Maximum Capacity.
+ For Android phones: Open Settings > Tap on Battery & Performance > Check information under Battery Usage (Battery Saver).

Phone tracking leads to a significant decrease in battery capacity.
2.3. Hearing Strange Noises Coming from Your Smartphone
Occasionally, you may hear strange noises coming from your device (such as echoes, crackling, buzzing noises, etc.), which could be a warning sign that your phone has been hacked. This occurs because hackers have installed spyware that interferes with the transmitted sound.
2.4. Unexpected Pop-ups or Changes on Your Phone Screen
Not sure how to tell if your phone is hacked? Keep an eye out for some unusual signs on your phone such as: Unexpected pop-ups or unfamiliar apps appearing; changes in the layout of apps on the home screen; unfamiliar appointments or reminders in your Calendar, etc. If so, these are indications that your phone has been compromised.
2.5. Appearance of Unidentified Applications
The presence of unidentified applications running in the background is a sign that your phone has been hacked. They often do not appear as recognizable icons on the home screen like regular apps, but rather as a link attached to another app, making them difficult for users to recognize.
You can check if your mobile device is running unfamiliar apps by:
+ iPhone: Users can directly scroll through the home screen or the app library to find unfamiliar apps.
+ Android: Open Settings > Select App Management.
2.6. Detecting Strange Messages, Calls in the Log
How to tell if your phone has been hacked? If one day your phone starts making calls or sending messages without clear identity, there's a high chance it has been accessed unlawfully.
If your phone keeps receiving strange calls/messages, that's a simple sign that someone is intruding into your device.
3. What to Do If You Detect Your Phone Is Hacked?
When detecting unauthorized access to your phone, take the following steps to protect your device:
3.1. Immediately Initiate Spyware Scanning Software
Here's a quick and safe suggestion for spyware, virus, and suspicious app detection: Certo (available for iOS and Android). Simply launch Certo, and it will automatically scan your phone, identifying any software/apps/links installed by hackers for easy removal.
3.2. Execute Removal Procedures for Threat Elimination
After Certo provides the information, promptly delete them from your device. Additionally, perform a factory reset to eliminate all potential threats capable of stealing information.
Here's how to proceed:
+ For iPhone: Go to Settings > General > Reset > Erase All Content and Settings > Confirm the command to Reset is done.
+ For Android: Navigate to Settings > System > Tap on Reset > Select Factory data reset > Choose Reset phone and confirm Reset phone.
3.3. Change the password for all accounts on the phone
Enabling the password saving feature can create opportunities for others to easily log in and obtain all account information, passwords. Therefore, to maximize device security, you should change to a new password for every account, especially for commonly used ones like bank accounts, social media accounts...
3.4. Reset the lock screen and PIN code
Next, don't forget to change the lock screen password, app password, and phone PIN. This prevents hackers from using stolen information to access the phone again.

Users need to change passwords, PIN codes immediately to keep phone data safe
3.5. Seek advice, guidance from reputable teams
In addition to implementing the above methods, you should also take your phone to a reputable repair center with a team of professional technicians to receive guidance on effectively enhancing phone security.
4. Protecting your phone from being hacked
Proactively securing your phone is the simplest measure to prevent it from being hacked. Mytour suggests some simple yet effective device protection methods below:
4.1. Avoid downloading unfamiliar, unverified apps
It's crucial to remember not to download and install unfamiliar apps from the internet. They may contain malicious software, viruses, malware... that could allow hackers to steal data without your knowledge.
4.2. Avoid unlocking your phone's bootloader
Many users unlock their phones (or Jailbreak) to experience some apps not available in the app store. This action inadvertently creates opportunities for intruders to access device data more easily. Therefore, limit unlocking your phone unless absolutely necessary.

Unlocking the phone creates opportunities for intruders to quickly infiltrate phone data.
4.3. Keep your phone with you at all times
The process of installing spyware on a phone can happen within a few minutes, even seconds. Therefore, you should not leave your phone unattended to ensure its safety from the risk of being tracked.
4.4. Set up complex PINs and passwords
The simplest way to prevent phone hacking is to choose high-security passwords and PINs. Instead of opting for familiar patterns like 0000, 1234, prioritize using passwords with a mix of numbers (such as 0, 1, 2, 3...), characters (such as #, $, @...), and avoid personal information (like birthdates, ID numbers...).
4.5. Avoid storing passwords on your phone
Users should limit the habit of saving login passwords on their phones. In case of a phone breach, hackers can easily access all account information. Except for unavoidable circumstances, you should write down passwords on paper for storage.
4.6. Regularly clear browsing history
In today's human life, the Internet is an indispensable part. Therefore, to ensure the safety of your data, proactively permanently delete your entire web browsing history every day. This action limits intruders from tracking usage habits, thereby inventing some disguised pop-ups, strange links, or fake forms suitable for you to steal information.
Deleting web browsing history daily prevents hackers from tracking device activity.
4.7. Activate device tracking service for lost devices
You should activate the device tracking feature for your phone in case you lose it somewhere and worry about data theft. The process is simple:
- For iPhone: Under Settings, select your iCloud name > Choose Find > Enable Find iPhone.
- For Android phones: Open the Settings app > Tap on Security and Location (or just Location) > Then select Mode > Choose GPS/Wi-Fi/Mobile network according to your preference.
4.8. Regularly update all applications
Users need to update to the latest version for all applications and the device operating system. This helps fix annoying bugs from the old version and eliminates background apps running concurrently with another app.
4.9. Enable Two-Factor Authentication (2FA)
2FA (short for 2-Factor Authentication) is a two-factor account security measure. It involves using login information (username and password) and a code sent to the user's phone/email. When this feature is enabled, any access from an unfamiliar browser is preemptively alerted, thus enhancing user account security.
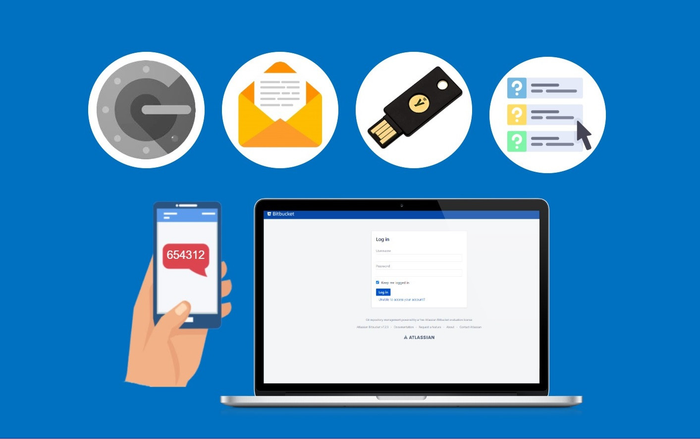
Activating Two-Factor Authentication enhances account protection effectively.
4.10. Avoid using public Wifi without VPN
VPN (Virtual Private Network) is a virtual network that helps users connect to the internet from broadcasting devices privately. It eliminates the access traces of the device and prevents hackers from infiltrating.
Hope the insights above have helped you understand how to recognize if your phone is hacked, and have effective ways to handle and prevent it. Although flagship phones today like iPhone 14 Pro Max 128GB in purple or Samsung Galaxy S23 / S23 Plus / S23 Ultra,... are equipped with highly advanced security technologies, being proactive in prevention is still considered paramount. Don't forget to follow other useful technology experience articles from Mytour to accumulate more interesting knowledge, folks!
