1. Install Antivirus Software
During usage, viruses can spread through various pathways on your computer: Through the Internet, USB drives, hard drives, CDs... And when your computer is infected with viruses, it can cause conditions such as: Sluggish, jerky, lagging performance. Data loss, file corruption. System disruption. Theft of personal information such as personal information, bank accounts, important data, passwords... Therefore, you should regularly scan and remove viruses from your computer to protect it from virus attacks, minimizing the risk of maximum virus infection.
This is something you should do as soon as you decide to buy a computer running the Windows operating system. Unfortunately, if your computer becomes infected with viruses, it will run slower than usual and may even put you at risk of losing all existing data on the computer. It's really dangerous if your computer's memory contains important folders and is completely erased. For Windows 8, Windows 10 versions, Microsoft has integrated antivirus software called Windows Defender by default. However, for absolute safety, install additional antivirus software that is highly optimized today such as Norton or McAfee...

2. Password Management
Managing numerous social media accounts and documents with various passwords? It's a hassle trying to remember all those long and complex characters. To address this, you can utilize a password management browser to control and organize them logically. Additionally, when setting passwords, opt for long and robust characters for security. Ensuring safety and security while using computers at work is not only beneficial for you but also for the entire business.
Ensure that you're receiving automatic updates from Windows Update and installing all updates required by your company. Keeping Windows, Microsoft Office, web browsers, and other software always updated will help protect your computer and your company. However, avoid installing any software from outside your workplace that your company has not approved or administered. Unauthorized programs can create security vulnerabilities.


3. Regularly Update to the Latest Upgrades
Windows Update occurs regularly for a reason. It's genuinely helpful because it promptly fixes errors in each version and provides additional security for your computer. Surely, you still remember WannaCry, right? If you don't update Windows, the WannaCry malware will exploit vulnerabilities in your device to infiltrate and steal data. However, if you regularly update, such incidents become challenging as Microsoft promptly releases patches to enhance your computer's security. Therefore, regularly updating Windows is for your benefit and safeguards your computer from harmful software.
Updating Windows also brings new features and fixes lingering bugs from previous versions. Not updating means missing out on new features Microsoft provides, and vulnerabilities remain unpatched. If you don't update Windows, you won't be able to access the Microsoft Store; instead, you'll have to manually search for and install apps, which is time-consuming. Most importantly, new Windows operating systems are not yet complete, so they require constant bug fixes and updates. Therefore, if you don't update regularly, your Windows operating system won't be complete and optimized.


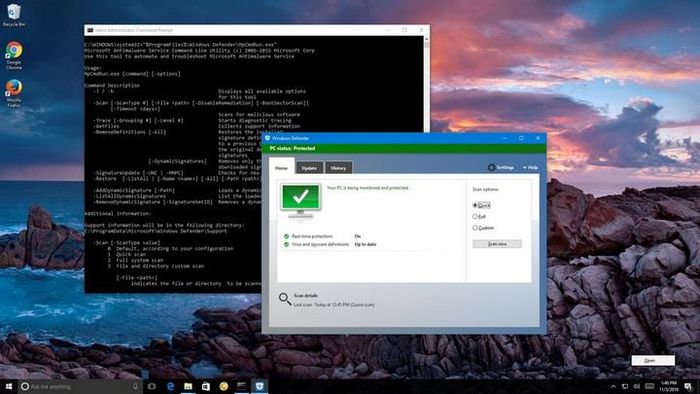
4. Initiate Malware Scanning Program
Malware presents a haunting concern for many Windows users. Malicious attacks using malware have become increasingly sophisticated and modern, running silently on your machine, often unnoticed even with daily use. When infected with malware, your computer may run slower, and you could potentially experience personal information leakage, theft of valuable internet and computer data. Ransomware stands as one of the most prevalent types of malware today. Cybercriminals install this malicious software into systems, encrypt personal data, block device access, and demand ransom payments to unlock it.
Ransomware often spreads through phishing emails or from users accessing infected websites. Attacks with this type of malware are becoming more common, with ransom amounts skyrocketing, sometimes reaching millions of USD. Microsoft has integrated Ransomware protection into the Virus and Threat Protection program to assist users in safeguarding their computers and data against ransomware malware attacks. Note that you won't be able to select Ransomware protection if you're using third-party antivirus software. When attempting this step, the system will display a warning that you're using multiple antivirus programs and recommend uninstalling others if you wish to enable this feature.

5. Install Firewall
Firewall, a network security system, monitors and controls incoming and outgoing network traffic. It establishes a barrier between a trusted internal network and an untrusted external network, such as the Internet. There are two basic types of firewalls: Protective firewalls safeguard personal computers or local networks, preventing intrusion or attacks from the outside. Restrictive firewalls, typically established by Internet service providers, block access to certain websites or servers, often used for Internet filtering or known as local protective firewalls.
The primary task of a firewall is to control data traffic between two areas of different trustworthiness, typically including: The Internet (an untrusted zone) and the internal network (a highly trusted zone). The ultimate purpose of a firewall is to provide controlled connections between different trust zones by applying a security policy and a connection model based on the principle of least privilege. If you're unsure whether your computer has activated the firewall, you can proceed as follows: Open Control Panel -> Windows Firewall. A selection window will appear, where you can click Turn Windows Firewall on to activate it or Turn Windows Firewall off to deactivate it.


6. Create two management accounts
You can create a local user account (offline account) for anyone who regularly uses your PC. However, the best option in most cases is for everyone using your PC to have a Microsoft account. With a Microsoft account, you can access Microsoft apps, files, and services across your devices. If needed, a local user account can have administrator privileges; however, it's best to create a local user account whenever possible.
Most computers today allow you to create multiple accounts for easy management and control. In addition to the admin account typically set up by the Windows installer, you can create an additional account for yourself to better manage the computer and prevent cases of forgetting the admin password. You can create a personal account by opening Control Panel -> User Account, then providing the required information to create a new account.


7. Encrypt Data
BitLocker encryption is available on devices running Windows 10 or 11 Pro, Enterprise, or Education editions that are supported. On supported devices running Windows 10 or newer, BitLocker will automatically be turned on the first time you sign in to your personal Microsoft account (such as @outlook.com or @hotmail.com) or your organization's or school's account. BitLocker isn't automatically turned on with a local account, but you can manually turn it on in the BitLocker Management tool.
This is an optimal way to secure your data. When selecting data encryption, no one except you and those granted access rights can read it. For office personnel with high document security needs, it's best to encrypt them before being compromised by malicious actors. Before executing the encryption command, most of these programs require you to set a highly secure password, so set at least 10-12 characters to prevent hackers from compromising it.


8. Email Management
In recent times, several email accounts have been heavily targeted by spam emails. This is undesirable and makes your mailbox difficult to manage and categorize due to the overwhelming volume of incoming emails. What you should do is take the time to filter through the emails and handle them logically. To send and receive emails, you'll need to access the Internet. Ensure that your device is connected to the Internet. Many email providers allow you to access your email through a website. Log in to your email account via the website and confirm that you can send and receive emails there.
If you can't, there may be an issue with your email server. Contact your email provider for assistance. If you have another email application or a different computer or mobile device, try sending and receiving emails from that application or device. If you still can't, there may be an issue with your email server. Contact your email provider for assistance. If your email provider doesn't have a website and you can't set up your email on another application or device, contact your email provider to see if your email server can be accessed.


9. System Storage Optimization
Storage space helps safeguard your data against drive failures and expands storage capacity over time as you add drives to your PC. You can use Storage Spaces to group two or more drives together into a storage pool, and then use capacity from that pool to create virtual drives called storage spaces. These storage spaces typically store two copies of your data, so if one of your drives fails, you still have a complete copy of your data. If that capacity slows down your machine, simply add more drives to the storage pool.
Excessive memory usage can also cause Windows operating systems to run like a snail. This is when you need to check your computer and clean up unnecessary files or documents, especially in the C drive. Ccleaner is one of the most helpful suggestions to clean up and optimize your computer's speed today. Especially, there is now a trial version of this application available for those who want to experiment.


10. Update to the Latest Browser Version
New features in recent Windows updates will help you customize your PC, enhance security, and be more creative with Windows. With these updates, you'll also find it easier to get things done on your PC and across your other devices, including syncing with Android phones (7.0 and above). While Microsoft thoughtfully installs Internet Explorer as the default web browser, most users still prefer other programs like Coc Coc, Chrome, Opera... because of their interface design and features they offer. However, it's essential to note that when downloading these browsers, update to the latest versions and access reputable links for downloads.
You'll find a set of enhancements limited to productivity and management areas. Enjoy standard WPA3 H2E support to enhance Wi-Fi security. Get GPU compute support in Windows Subsystem for Linux (WSL) deployments and Azure IoT Edge for Linux on Windows (EFLOW) for machine learning and other deep computing workflows. To quickly check information on headlines, weather, latest sports, and more, open News and Interests on the taskbar. Update quickly, then get back to what you were doing.


