There are few things more unsettling than the thought of someone remotely accessing your personal computer. If you believe that a hacker might be controlling your device, the first step is to disconnect it from the internet. Once offline, you can search for and remove any entry points that the hacker may have used to access your system. After securing your system, you can follow additional steps to prevent further intrusions.
Steps
Check for signs of unauthorized access
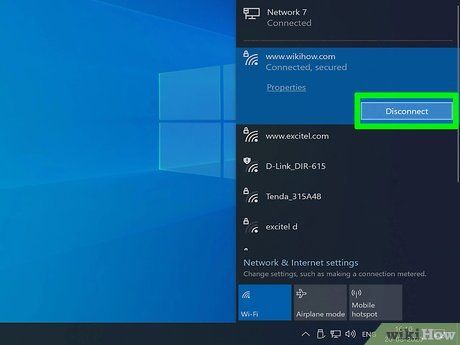
Disconnect your computer from the network. If you suspect that someone is remotely accessing your computer, immediately disconnect from the internet. This means unplugging the Ethernet cable and turning off Wi-Fi.
- Common signs of unauthorized access include the mouse moving on its own, applications opening unexpectedly, or files being deleted automatically. However, don’t worry too much about pop-up ads; many apps with automatic update features can generate these during updates.
- Slow internet speeds or strange programs running may not necessarily indicate a hack.
Check the list of recently accessed files and applications. Both Windows and Mac allow you to view a list of recently opened files and applications. If you notice anything unusual in these lists, it could indicate that someone has accessed your computer without your consent. To check the information, follow these steps:
- Windows: To see recently opened files, press Windows + E to open File Explorer. Look for "Recent files" at the bottom of the sidebar to spot any unusual activity. You can also check recently opened apps from the Start menu.
- Mac: Click the Apple menu at the top-left of the screen and select Recent Items. You can view Applications for recently used apps, Documents for opened files, and Servers for any external connections.
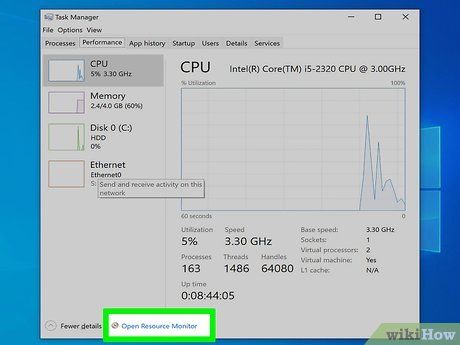
Open Task Manager (Windows) or Activity Monitor (Mac). These utilities provide insight into what’s happening on your computer.
- Windows – Press Ctrl + Shift + Esc.
- Mac – Open the Applications folder in Finder, double-click the Utilities folder, and then double-click Activity Monitor.
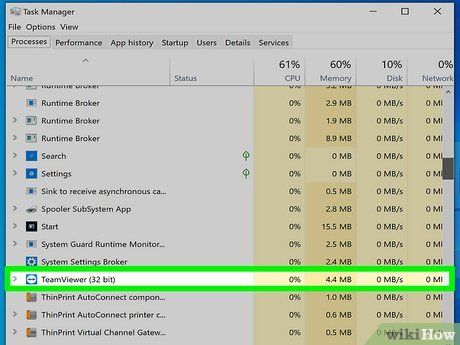
Look for remote access programs in the list of active programs. Now that you’ve opened Task Manager or Activity Monitor, check the list of running programs for any suspicious or unfamiliar ones. Here are some common remote access tools that might have been installed on your system without your permission:
- VNC, RealVNC, TightVNC, UltraVNC, LogMeIn, GoToMyPC, and TeamViewer.
- If you come across any unknown or suspicious programs, you can look them up online to learn more.
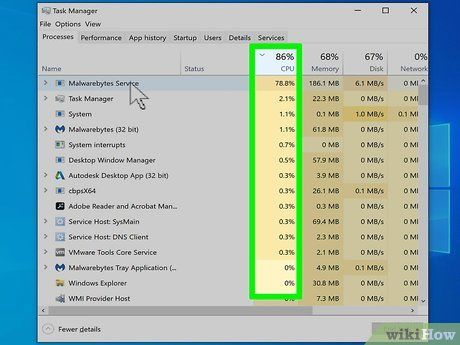
Pay attention to unusual CPU activity. You’ll find this information in Task Manager or Activity Monitor. While high CPU usage isn’t always an indication of a security breach, if you’re not actively using your computer and the CPU is still running high, it may suggest unauthorized background processes. However, CPU activity can also increase when programs are updating or torrents are downloading, which you might have forgotten about.
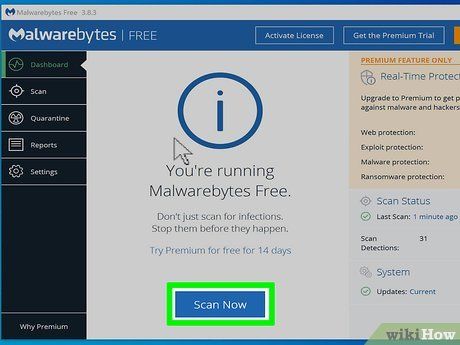
Run a virus and malware scan. If you're using Windows 10, you can use the built-in scanning tool by navigating to Settings > Update & Security > Windows Security to detect fake applications. If you're using a Mac, consult guides on scanning tools designed specifically for macOS.
- Malware is often the easiest way for hackers to gain access to your personal computer.
- If you don’t have an antivirus program, you can download one from another computer and transfer it via USB. Once transferred, install the antivirus and run a full scan.
- Malwarebytes Anti-Malware is a free third-party tool available for both Windows and Mac. You can download it for free from https://www.malwarebytes.com.
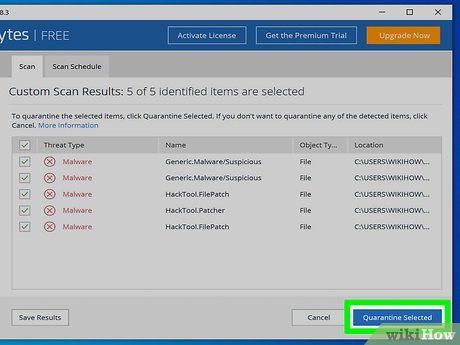
Isolate any files that are detected. If your antivirus or anti-malware program finds any files during the scan, isolating them will prevent them from impacting the system's operations.
Download and run the Malwarebytes Anti-Rootkit Beta program. You can download the program for free at https://www.malwarebytes.com/antirootkit. This tool helps you identify and remove "rootkits"—malicious software that hides within your system files. The program will scan your computer, which may take some time.
Monitor your computer after removing malware. If your antivirus and/or anti-malware program finds harmful software, you've successfully removed the threat, but you should still keep a close watch on your computer to ensure the malicious software has been fully eliminated.
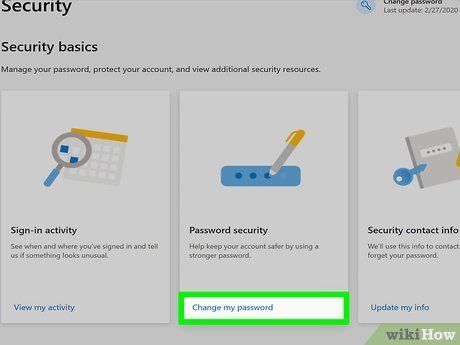
Change all of your passwords. If your computer was compromised, it's possible that all your passwords were captured by a keylogger. Once you're certain the threat has been eradicated, change the passwords for all your accounts. Avoid using the same password across multiple services.
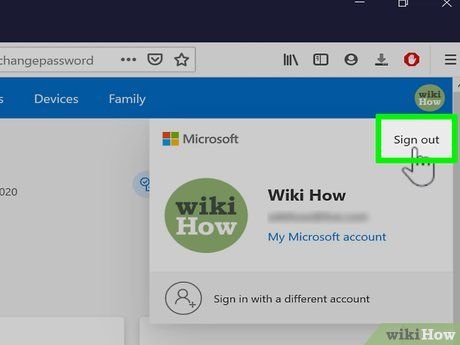
Log out of all accounts. After updating your passwords, go through each account and log out completely. Be sure to log out from all devices. This ensures that the new passwords will take effect, preventing anyone from using the old ones.
Completely erase the system if you can't remove the intrusion. If your computer is still compromised or you suspect there are remaining threats, the only guaranteed way to fix it is by wiping the system and reinstalling the operating system. Before doing so, however, make sure to back up important data as everything will be erased and reset.
- When backing up data from an infected computer, ensure you scan each file before saving it. Restoring old files may reintroduce the infection.
- Follow the guide on how to format your computer (Windows or Mac) and reinstall the operating system.
Prevent future intrusions
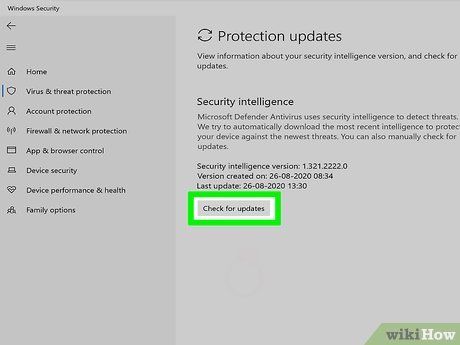
Always keep your antivirus and anti-malware programs updated. An up-to-date antivirus program will detect most potential threats. Windows includes the built-in Windows Defender antivirus, which can automatically update and run in the background. Additionally, there are several free antivirus options like BitDefender, avast!, and AVG. Installing just one antivirus program is sufficient.
- Check out the guide on enabling Windows Defender on a Windows computer.
- If you prefer not to use Defender, you can follow instructions to install a different antivirus program. Windows Defender will automatically disable itself when another antivirus is installed.
Ensure your firewall is properly configured. If you're not running a web server or other programs that require remote access to your computer, there's no need to open additional ports. Most programs that require ports use UPnP to automatically open and close them when necessary. Leaving ports open indefinitely increases the risk of intrusion.
- See how to configure port forwarding on your router and make sure no ports are open unless required for a server you're using.
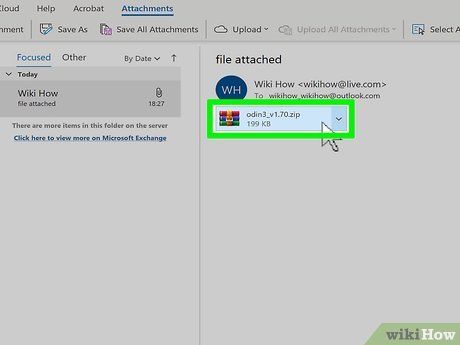
Be cautious with email attachments. Email attachments are one of the most common ways to infect your system with viruses and malware. Only open attachments sent by trusted sources, and be sure that they intentionally sent the file to you. If someone in your contact list has an infected computer, they may unknowingly send a malicious attachment.
Ensure that your passwords are secure and hard to guess. Each service or program you protect with a password should have a unique and difficult-to-guess password. This ensures that if one service is compromised, hackers won't be able to use that password to access other accounts. Refer to the guide on using password managers to make this process easier for you.

Avoid using public Wi-Fi networks. Public Wi-Fi networks are risky since you can't control the network system. You don't know if someone else using the same Wi-Fi is monitoring the traffic from your computer. Through public Wi-Fi, others can access your open web browser and other information. You can reduce this risk by using a VPN whenever connecting to Wi-Fi to encrypt your connection.
- Check the guide on how to set up a VPN connection for more information.
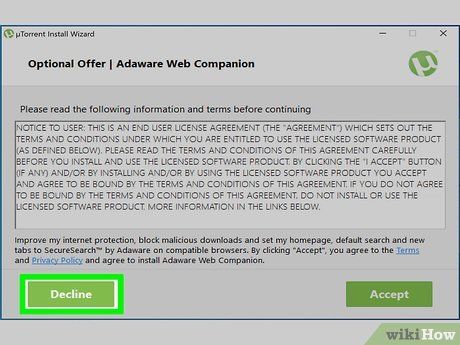
Always be cautious with programs downloaded online. Many "free" programs on the internet come bundled with unwanted software. Pay attention during the installation process to decline any unnecessary extras. Avoid downloading illegal software, as this is a common way to infect your operating system.
Tips
- Note that your computer may restart to install updates. Many newer computers are set to automatically update the system, often in the evening when you're not using it. If your computer restarts while you're not using it, it's likely because the computer in Sleep mode was "woken up" to apply updates.
- Although remote access to your computer is possible, the likelihood is low. You can take steps to prevent unauthorized access.
