There are two types of hackers (individuals who gain unauthorized access to information systems) – those who aim to disrupt systems to create a better world and those who seek to cause trouble and harm others. The latter are the ones you need to be wary of (the former simply require an open and broad-minded perspective). If you suspect that your computer or electronic devices may have been compromised, don’t ignore this intuitive concern and act swiftly. Hackers can infiltrate devices in unexpected ways, but it’s important to understand that you can often detect such intrusions by observing your screen. Below are some potential signs that your information system may be under unauthorized access, along with quick action suggestions for such scenarios.
Steps
Identifying Suspicious Signs of Unauthorized Access
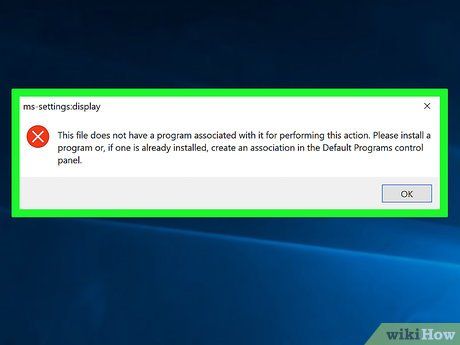
- Certain programs and files that usually open or function properly no longer do so.
- Files you never deleted seem to have disappeared, moved to the recycle bin, or been deleted.
- You can’t access programs with your usual passwords. You notice that passwords on your computer have been changed.
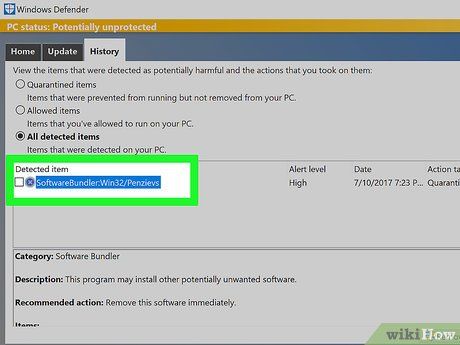
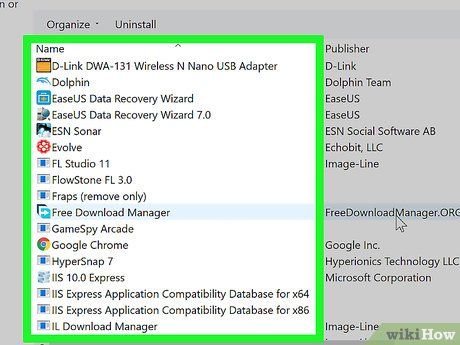
- One or more programs appear on your computer that you didn’t install.
- Your computer frequently connects to the internet when you’re not using it.
- File contents have been altered, and you didn’t make those changes.
- Your printer may behave oddly. It might refuse to print no matter what you do, or it might print pages not included in your print command.

- One or more websites deny your access due to incorrect passwords. Try accessing multiple sites you usually visit: if password-protected access continues to be denied, it could indicate unauthorized access. Could it be that you responded to a phishing email (a fake email asking you to update your password/security details)?
- Internet searches are being redirected.
- Additional browser screens may appear. They might pop up and disappear while you’re doing nothing. They could be darker or the same color, but you’ll notice them regardless.
- If you’ve purchased a domain, you might not be able to access it despite payment.
- Fake virus messages. Regardless of whether your device has antivirus software: if not, these messages will automatically alert you; if it does, and assuming you know what your program’s messages look like, be wary of fake ones. Don’t click on them: they’re scams trying to get you to reveal credit card information in a panic to remove a virus. Be aware that hackers now control your computer (see What to Do below).
- Additional toolbars appear on your browser. They might carry "helpful" messages. However, there should only be one toolbar, and it’s suspicious if more appear.
- Random and frequent pop-ups appear on your computer. You’ll need to remove the program causing this.
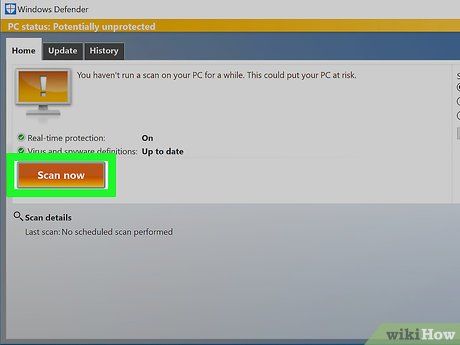
- Antivirus or anti-malware software isn’t working and seems disconnected. Your Task Manager or Registry Editor might also stop functioning.
- People in your contact list receive fake emails from you.
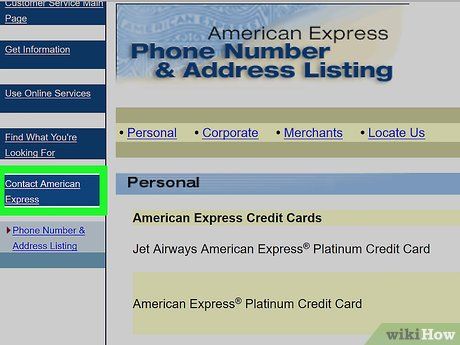
- Money is missing from your bank account, or you receive bills for online transactions you never made.

- Check your personal information. Google yourself. Does Google return personal details you never disclosed? They might not appear immediately, but being vigilant about this risk is crucial in case your personal information is leaked.
What to Do
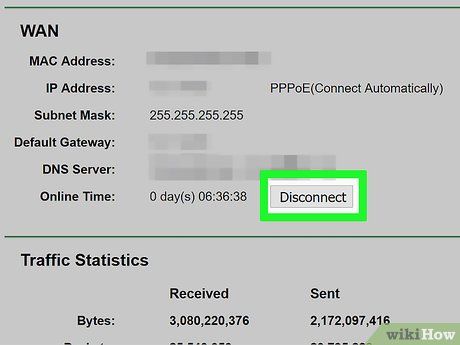
- Unplug the router from the socket to ensure no connections remain!
- Print this page or save it as a PDF before disconnecting to continue following these instructions without needing the internet. Or, read it on another device not compromised by unauthorized access.
Advice
- Turn off your network when going out.
- The best approach is to take preventive measures beforehand.
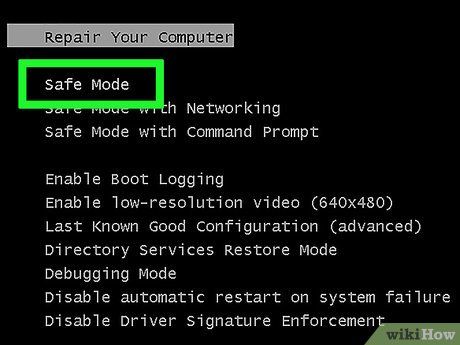
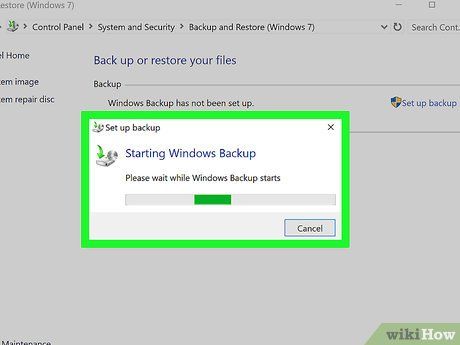
- To retain the operating system you had before the unauthorized access, use backup software.
- Back up important files (such as family photos, documents) to an encrypted USB drive and store it in a safe. Alternatively, you can save them on OneDrive or Dropbox.
- Always create backup files.
- You can completely disable location settings. Combined with a strong VPN (such as F-Secure Freedome), this will almost entirely eliminate the possibility of an uninvited guest determining your location. Also, avoid filling in your location details on Facebook (such as the "hometown" section).
Warnings
- Worse, hackers can turn your computer into a "zombie," using it to attack other computers/networks and carry out illegal activities.
- If programs and files won’t run or open, and the screen displays an electronic image or a light show, the computer may need a new operating system or, if the hacker hasn’t destroyed the backups, you’ll need to restore the computer to its previous settings.
- If left unchecked, the computer could become completely useless, and you’ll likely need to reinstall the operating system or buy a new one.
