A keylogger is malicious software or hardware installed on a computer to monitor users' keystrokes. While keyboard tracking is legal in some rare cases, hackers often use keyloggers to collect sensitive data and passwords. This type of tool can slow down your computer's performance. Mytour provides a guide on how to find and remove keyloggers.
Steps
Prepare the Computer
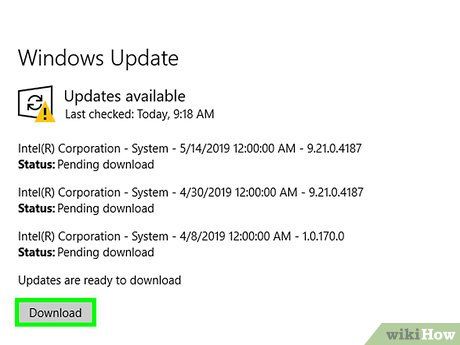
Update your operating system and applications. Outdated software may have security vulnerabilities that make your computer more susceptible to attacks.
- Ensure all users of the computer understand the importance of avoiding suspicious links and pop-up ads, and stay clear of offers that seem too good to be true.
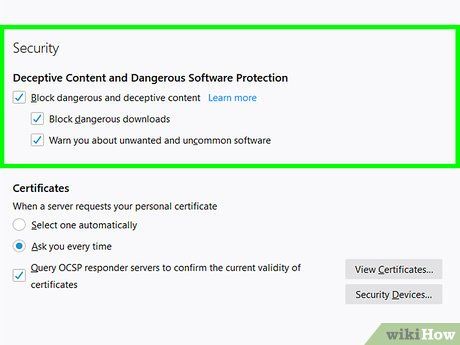
Set up browser security settings. The configuration process varies across different browsers. First, open the Settings menu on your browser and locate the Privacy or Security section. Then, disable unwanted extensions, block harmful websites, and clear your browsing history. Lastly, remove cookies that track personal information.

Install trusted protection software for your computer. Install required anti-malware programs and ensure your antivirus software is always active. Free options include Malwarebytes (anti-malware) and Avast or Panda (antivirus). It's essential to keep your protection software up to date.
Look for keyloggers
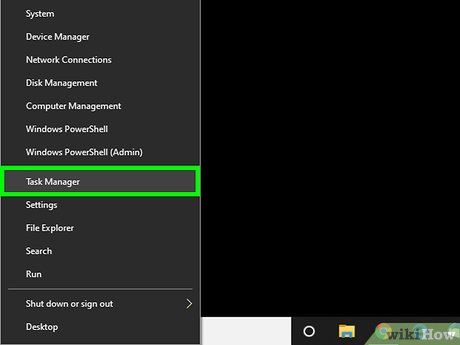
Open Task Manager. Follow these steps to access Task Manager:
- Right-click on the taskbar at the bottom of your screen.
- Select Task Manager from the pop-up menu.
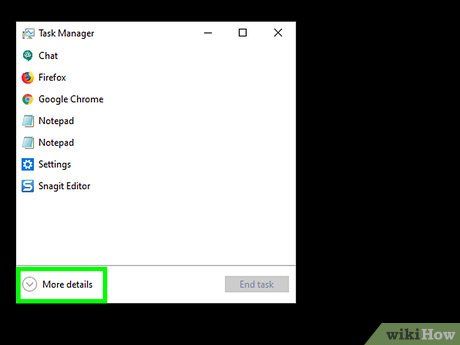
Click on More Details (Other Details). This option is located in the lower-left corner of Task Manager. A list of all active processes on your computer will appear, including open applications and background tasks.
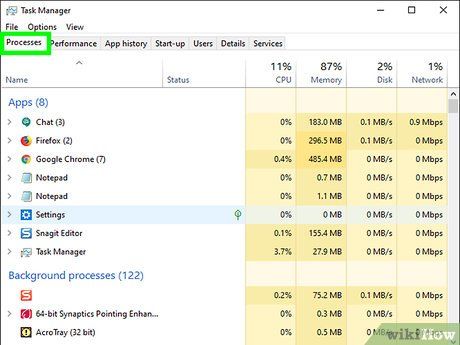
Examine suspicious processes. You may notice some unusual background processes running. Check any unfamiliar applications.
- If you're unsure about a process, right-click on it and select Search online. This will perform a Google search for the application or process.
- If you identify a process that needs to be stopped, click on it and select End task at the bottom-right corner.
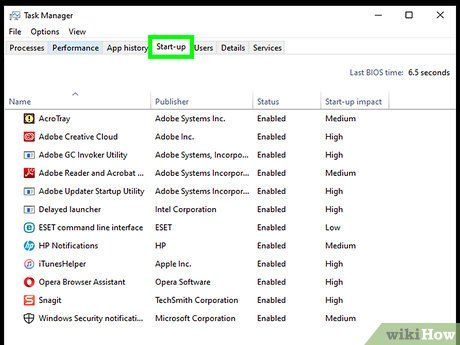
Click on the Startup tab at the top of Task Manager. A list of programs that start with your computer will appear.
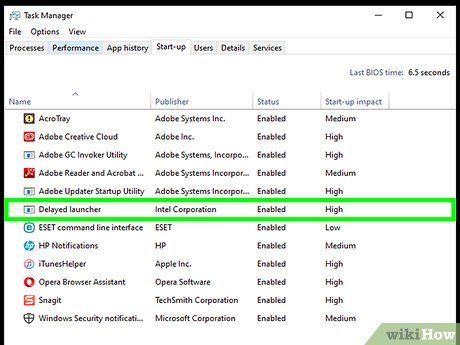
Check all suspicious programs. Go through the startup program list to see if anything seems unusual.
- If you're unsure about any program, right-click on it and select Search Online. This will search for the program on Google.
- Once you've identified a program that should be disabled, click on it and select Disable in the lower-right corner.
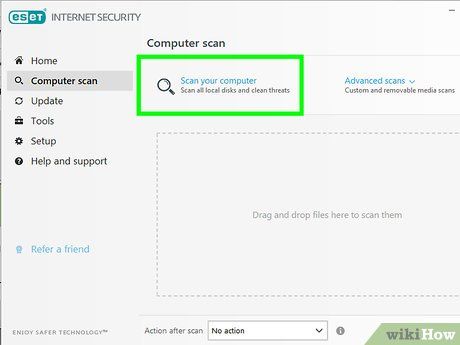
Scan for viruses and malware. Many keyloggers can bypass msconfig and Task Manager, even disguising themselves as legitimate programs. Use security software to scan for viruses and malware on your computer.
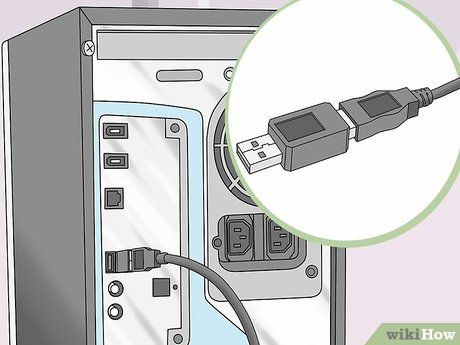
Inspect your desktop computer. If you're using a desktop, there's a chance a hardware keylogger is connected to your machine. Check where the keyboard cable plugs into the tower. If any device is placed between the keyboard cable and the tower, it could be a hardware keylogger.
- Note that this could also be a legitimate device or adapter. If you find an unfamiliar device connected to your computer, investigate who plugged it in and why.
Remove keylogger
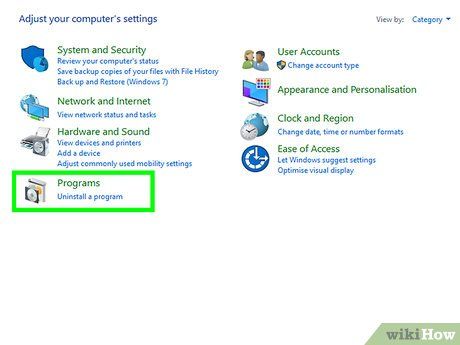
Check if the keylogger is visible. If the keylogger you found appears in the Control Panel's program list, it's likely a legitimate keylogging program with an uninstaller. You should uninstall the program and use anti-malware software to remove any remnants left behind.
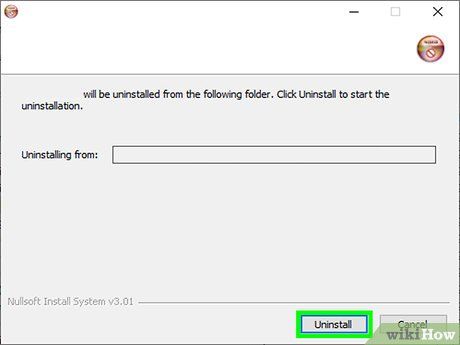
Try using an uninstaller program. For some keyloggers, such as Logixoft's Revealer Keylogger, the installation program can be used to uninstall the keylogger. Download the setup program and use it to uninstall the keylogger. You can also uninstall programs through the Settings menu. Finally, use reputable malware scanners to delete any leftover files.
- If you're unable to uninstall the program, try booting your computer in Safe Mode and uninstalling the keylogger in Safe Mode.
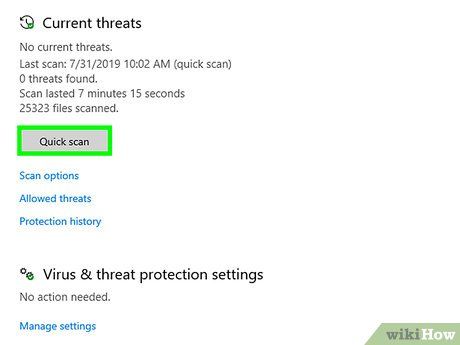
Run Windows Defender Offline. After installing the latest antivirus updates, run a rootkit detector like Windows Defender Offline. To start the program, you'll need to access the settings or create offline media.

Search for advice on a specific keylogger by its name. Search on Google for the name of the particular keylogging program. Some keylogging programs (such as Refog) may actively prevent uninstallation. You should visit forums like Quản Trị Mạng to find methods to remove the keylogger without damaging your computer.
- Hijack This is a suitable tool for removing programs deeply embedded in the Windows Registry. However, you must exercise caution when using Hijack This. The program may accidentally delete files that Windows needs to operate. Make sure to research on Google before removing any registry items.
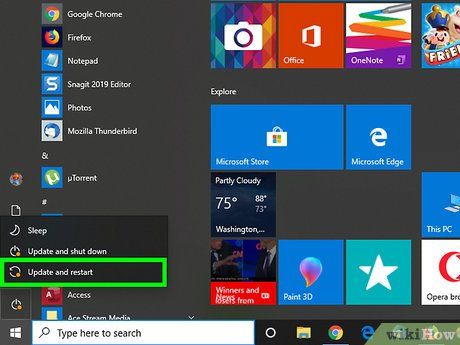
Consider reinstalling your computer's operating system. Many keyloggers are deeply embedded within the Windows operating system and can be very challenging to remove. In certain cases, the easiest solution is to back up your data and reinstall Windows.
- Reinstalling Windows will erase all data on your computer. Be sure to back up everything before reinstalling the operating system. You can back up your data using an external hard drive or cloud services like Google Drive, Dropbox, One Drive.
- Reinstall Windows if you detect a keylogger on a computer you plan to use for banking transactions or handling confidential business matters, as keyloggers may not have been fully removed yet.
Advice
- If you use your computer for banking transactions, your password may have been compromised. Immediately change your password on a secure device. Then, contact your bank if you notice any suspicious activity involving your account.
- Recommended free programs for installation include Avast and Comodo.
Warning
- Some keyloggers do not appear on anti-malware programs or firewalls.
