The most effective way to ensure that your database is secure from hackers is to think like one. What kind of data would a hacker seek? What steps would they take to acquire that information? There are numerous methods to hack into various types of databases, but most hackers will attempt to crack high-level passwords or execute database attacks. If you're familiar with SQL commands and basic programming languages, you might try hacking into a database yourself.
Steps
Use SQL injection
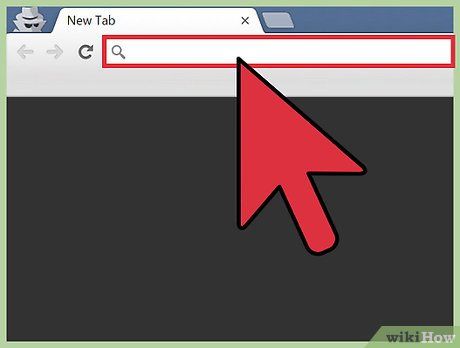
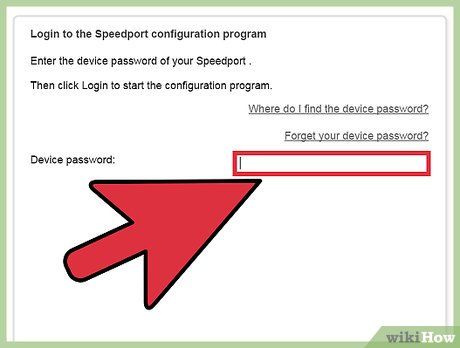
Identify the database's vulnerabilities. To apply this method effectively, you need to be proficient with database commands. Start by opening the database login interface in your web browser and entering a single quotation mark (') in the username field. Then click 'Login'. If an error such as 'SQL Exception: quoted string not properly terminated' or 'invalid character' appears, it indicates that the database is vulnerable to SQL injection attacks.
Find the number of columns. Go back to the database login page (or any other URL ending with 'id=' or 'catid=') and click on the browser's address bar. After the URL, press the spacebar and type 'order by 1', then hit Enter. Increase the number to 2 and press Enter. Continue increasing the number until you encounter an error. The actual number of columns is the number entered right before the error message.
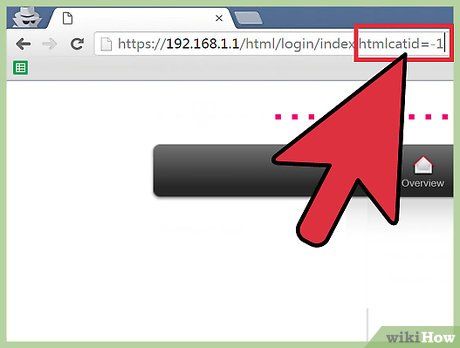
Find columns that accept variables. At the end of the URL in the address bar, change 'catid=1' or 'id=1' to 'catid=-1' or 'id=-1'. Then, press the spacebar and enter 'union select 1,2,3,4,5,6' (if there are 6 columns). You need to enter incrementing numbers for all columns, separating each number with a comma. Press Enter, and the columns that accept variables will be displayed.
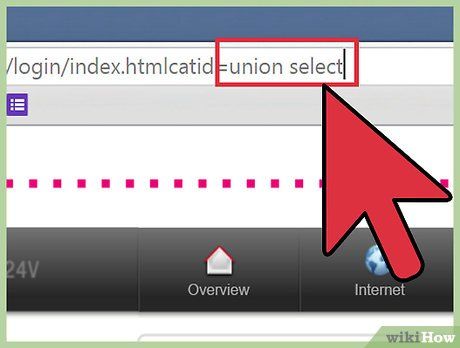
Inject SQL commands into columns. For example, if you want to find the current user and inject content into column 2, remove everything after 'id=1' in the URL and press the spacebar. Then enter 'union select 1,concat(user()),3,4,5,6--' and press Enter. The username of the current database user will be displayed on the screen. Select the SQL command to retrieve the necessary information, such as a list of usernames and passwords to crack.
Crack high-level database passwords
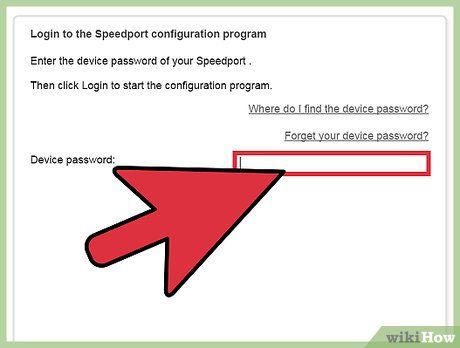
Attempt to log in with high-level user privileges using the default password. Some databases do not have a default high-level (administrator) password, so you can leave the password field blank. Others may have default passwords that can easily be found on database support forums.

Try common passwords. If the administrator has protected the account with a password (which is quite common), you can attempt common username/password combinations. Some hackers publicly share password lists they've cracked using auditing tools. Try a few combinations of usernames and passwords.
- The website https://github.com/danielmiessler/SecLists/tree/master/Passwords is well-known for providing many password lists collected by hackers.
- Manually guessing passwords may take time, but it’s worth trying before resorting to more complicated methods, as it costs you nothing.
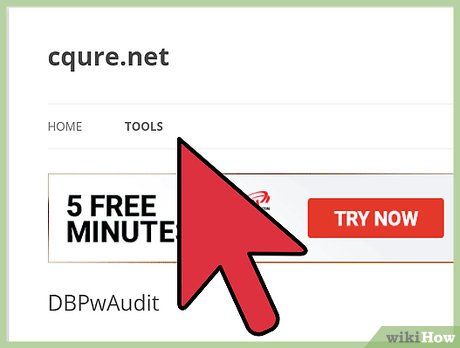
Use password testing tools. There are various tools you can use to try thousands of word and character/number combinations using brute force attacks until the password is cracked.
- DBPwAudit (for Oracle, MySQL, MS-SQL, and DB2) and Access Passview (for MS Access) are popular password testing tools that work with most databases. You can also search Google for newer password testing tools tailored to specific databases. For example, if you're hacking an Oracle database, search for 'password audit tool oracle db'.
- If you have an account on the server hosting the database, you can run a hashing tool like John the Ripper to decrypt the database’s password file. The location of the hash file varies depending on the database.
- Only download tools from trusted websites. Research the tool you're considering using before executing it.
Database attack.
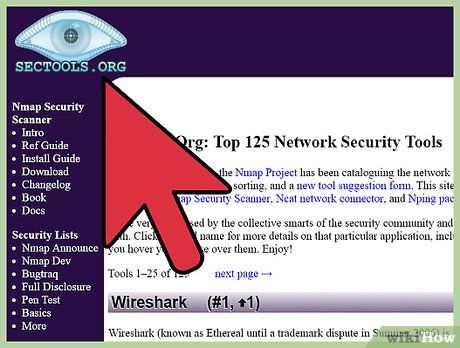
Find an exploit to execute. Sectools.org is a website that aggregates security tools (including exploits) that have been used for over a decade. Their tools are quite reputable and are used by system administrators worldwide to test network security. Browse through their 'Exploitation' category (or another trustworthy site) to find tools or text files that may help you exploit a database’s security vulnerabilities.
- Another site offering exploits is www.exploit-db.com. Visit the site, click on the 'Search' link, and search for the type of database you want to hack (e.g., 'oracle'). Enter the Captcha code provided and search.
- Make sure to thoroughly research every exploit you intend to try, as you'll need to troubleshoot if issues arise.
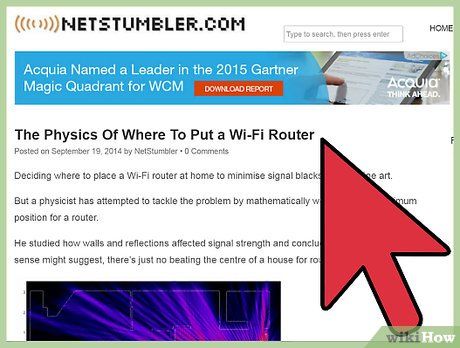
Find vulnerable networks to access (wardriving). Wardriving is the act of driving (or even biking or walking) around an area using network scanning tools (such as NetStumbler/Kismet) to find unsecured networks. Essentially, this action itself is not illegal, but accessing these networks and engaging in illegal activity is.
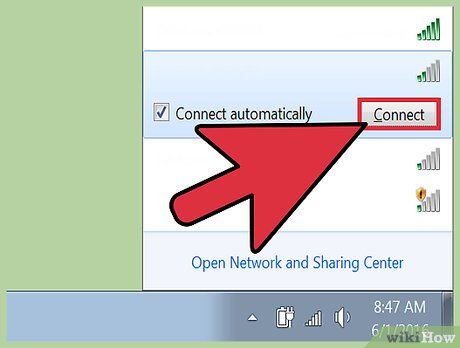
Use an exploit to attack a database from the network you just accessed. If you plan on doing something that you really shouldn’t, using your home network is not a good idea. Instead, find and connect to an unsecured Wi-Fi network, then use the exploit you have researched and selected to attack the database.
Advice
- Sensitive data should be protected behind a firewall.
- Encrypt your Wi-Fi with a password so unauthorized users cannot use your home network to conduct database attacks.
- You can seek advice from hackers. Sometimes the best insights are not found online.
Warnings
- You need to understand the laws and consequences of hacking databases in Vietnam.
- Never gain access to any computer within your private network without proper authorization.
- Accessing someone else’s database without permission is illegal.
