You might be well-known for your computer skills, or perhaps you just want others to see you that way. Hacking a computer requires knowledge of computer systems, cybersecurity, and coding. So, if people observe what you do and assume you're hacking, they will be easily impressed. You don't have to break the law to appear like a hacker; simple terminal commands or creating a .bat file that launches a Matrix-like browser filled with random characters can leave a strong impression.
Steps
Use Command Prompt
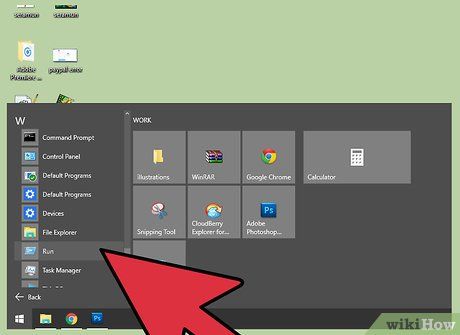
Open the "Run" feature on your computer. You can click the Start menu and search for "Run", or simply use the search bar on your computer to find and open it.
- Windows users can quickly open Run using this keyboard shortcut: ⊞ Win+R
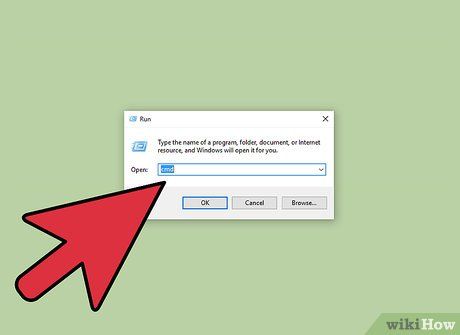
Open the Command Prompt window. Type "Cmd" into the search bar in the Run window. Command Prompt (or Command Line) will appear, a program that allows users to interact with their computer through text-based input.
- Apple users can open the Terminal – the Mac version of Command Prompt – by using Spotlight or searching for "terminal" on their computer.
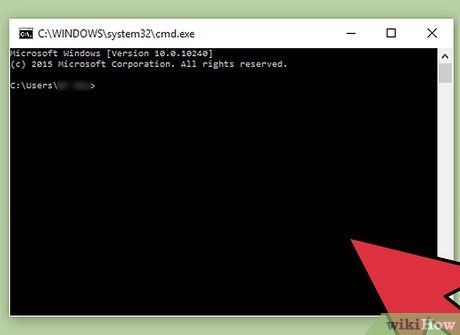
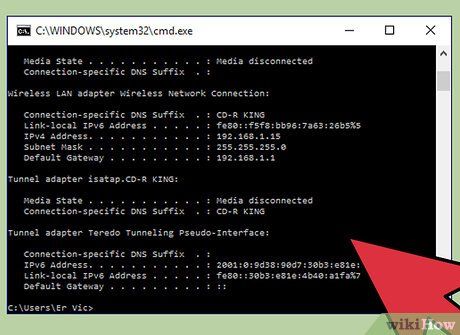
Use Command Prompt or Terminal to simulate hacking. There are many commands you can use in Windows Command Prompt and Apple Terminal to execute tasks or retrieve information. The commands below look impressive but are harmless to software and entirely legal.
- Windows users can try entering the following commands, remembering to quickly press ↵ Enter after each one to make the process seem more complex:
- color a
- This command changes the text color in the Command Prompt window to green with a black background. You can replace the color code after "color" with numbers 0-9 or letters A-F to change the text color.
- dir
- ipconfig
- tree
- ping google.com
- The Ping command checks whether a device can communicate over a network. It’s simple, but not everyone knows it. You can substitute any website for Google in the example above.
- For Apple computers, you can use the following safe commands to fill the screen with rows of characters as if you were performing a professional hack. Enter these commands in the Terminal window to achieve the desired effect:
- top
- ps -fea
- ls -ltra
Switch between commands and windows. You can open multiple Command Prompt or Terminal windows and use different commands to make it look like you’re running several extremely complicated and unrelated processes at once.
Create a .bat file on Windows
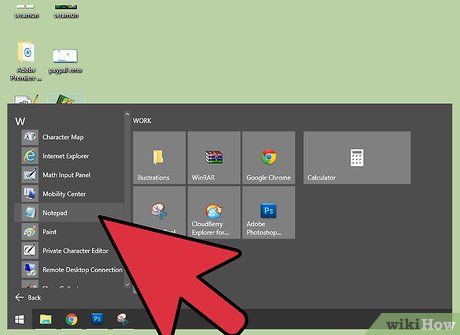
Open Notepad. To create a .bat file, you need to write plain text using a text editor and save it so the computer can read it as an executable command. Notepad or any other basic text editor can be used to write a .bat file.
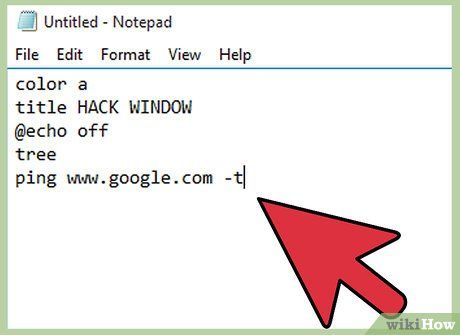
Create the .bat file process in Notepad. The following text will open a window with green font and a title of "Hack Window". To change the title, simply replace the "title" content in the Notepad file. The "@echo off" command will hide the command prompt, and "tree" will display the directory structure, making the hack process appear more realistic. The final line of the text will ping the Google server, which isn’t illegal but adds complexity to make it seem more impressive to non-experts. Enter the following into a blank Notepad document:
- color a
title HACK WINDOW
@echo off
tree
ping www.google.com -t
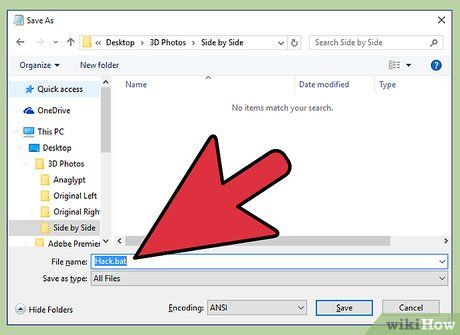
Save the document as a .bat file. When saving the file, choose "Save as". In the dialog box that appears, name the file with a .bat extension. The text document will be saved as a batch file that executes the series of commands required by the operating system.
- This method may not work on Windows Vista.
- The dialog box will warn that saving the file with a .bat extension will remove all formatting. Click "Yes" to complete the creation of the .bat file.

Run the .bat file. Double-click the .bat file located in the folder where you saved it. A window will pop up and run a series of complex processes that hackers (also known as cybercriminals) typically perform, making it look incredibly realistic.
Use an online website

Open a web browser. Some websites can mimic complex computer features. These websites are created for special effects in films/videos or for users like you to explore.
Check out hackertyper.net. This website generates text similar to what hackers typically produce, at a speed sure to leave viewers amazed. One potential issue when using this site to fool your friends is that the hacker-esque code is generated too quickly, which might ruin the effect.

Interface with the hacker emulator on geektyper.com. This site uses the most realistic hacker emulators. Upon accessing the homepage, you can choose a theme instead of typing text to simulate hacking. Users can even click on folders to initiate fake complex processes.
- Switch between combinations of hacker-style text and simulated processes that can be activated by clicking on folders displayed in the browser window after selecting a theme.

Open these different websites in separate windows. Each site generates a unique style of hacker text/code, providing a different atmosphere. You can quickly switch between open windows using the Alt+Tab ↹ combo to cycle through options. Enter some key combinations in each window before pressing Alt+Tab ↹ again to switch to a new fake hack browser window to intensify the effect. If the tabs are within the same window, you can use Ctrl+Tab ↹.
- Try arranging the open windows differently or leave some windows open in the background to make it seem more authentic.
On Linux (Debian)
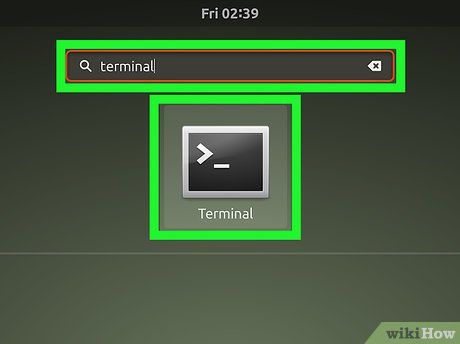
Open a new window in the terminal.
Gõ: "sudo apt install hollywood" rồi nhấn ↵ Enter
- Bạn cũng có thể dùng các trình quản lý gói GUI như Synaptic
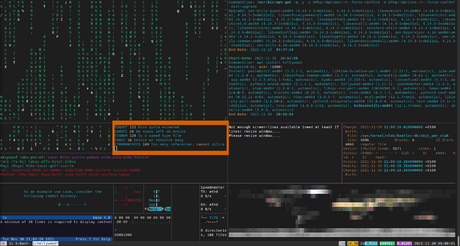
Gõ "hollywood" và nhấn ↵ Enter lần nữa
Lời khuyên
- Nếu biết viết kịch bản cho tập tin batch, bạn có thể nâng quá trình này lên tầm cao mới.
- Bạn có thể áp dụng bài viết này để gây ấn tượng với bạn bè.
Cảnh báo
- Those familiar with computer systems and coding will quickly recognize whether you're genuinely hacking or just pretending. Make sure to choose your audience wisely.
- Some older individuals might believe you're actually hacking, so be careful not to get into any trouble.
- Be cautious when using Command Prompt. You could accidentally input a command that executes and damages critical files on your computer, resulting in data loss or worse.
