This Mytour article will guide you on enhancing the security of your accounts, mobile devices, firewalls, computers, and network information.
Steps
Secure Your Account
Create a complex password. Passwords used to access your accounts on apps or websites should include multiple numbers, a mix of lowercase and uppercase letters, as well as special characters that are hard to guess.
- Avoid using the same password for more than one website or account. This minimizes potential damage if a hacker obtains one of your passwords.
Utilize a password manager. Password managers store and auto-fill your credentials across various sites, enabling you to generate unique, complex passwords for each platform without the hassle of manual entry. While it’s essential to safeguard your passwords, a password manager enhances your device's security.
- Some highly-rated third-party password managers include "Dashlane 4", "LastPass 4.0 Premium", "Sticky Password Premium", and "LogMeOnce Ultimate".
- Most browsers come with built-in password managers that securely store and encrypt your passwords.

Never share your passwords. While this advice may seem obvious, it’s worth repeating: Except for certain school-related services, you should never, and are never obligated to, provide your password to website administrators for account access.
- This rule also applies to IT professionals, Microsoft, or Apple representatives.
- Similarly, avoid sharing your tablet or phone PINs or passwords with others. Even friends might accidentally disclose them.
- If you must share your password for any reason, change it immediately after the person completes their task.

Change passwords regularly. Beyond keeping passwords confidential, update them across accounts and devices at least every six months.
- Ensure no password is reused (e.g., your Facebook password should differ from your bank account).
- When updating, create entirely new passwords rather than making minor alterations.
Enable two-factor authentication (2FA). 2FA requires you to enter a code sent via text or another service after entering your username and password. This makes it harder for hackers to access your information, even if they have your password.
- Most major websites, including popular social networks, offer 2FA. Check your account settings to enable this feature.
- You can set up 2FA for your Google account.
- Popular apps for receiving authentication codes include Google Authenticator and Microsoft Authenticator.
Read privacy policies carefully. Any company handling your information must have a privacy policy detailing how they use and share your data.
- Many people habitually agree to privacy policies without reading them. If reading thoroughly feels tedious, at least skim to understand how your data will be used.
- If you disagree with any terms or feel uncomfortable, reconsider sharing your information with that company.
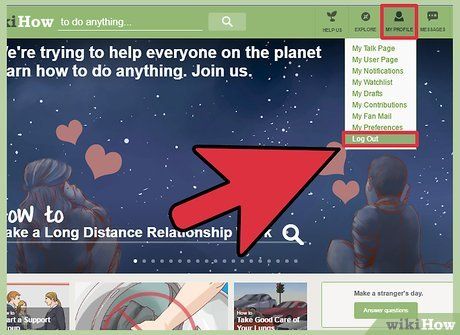
Log out of accounts after use. Simply closing the browser window isn’t enough. Ensure you click (or tap) your account name and select Log Out (or Sign Out) to manually sign out and remove login information from the site.
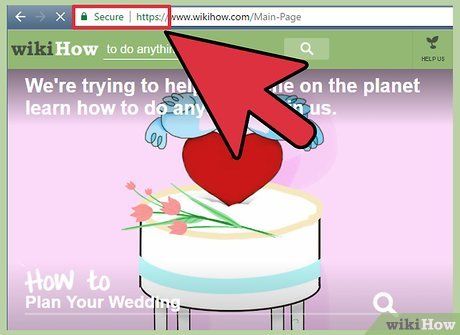
Ensure you enter passwords on official websites. Phishing scams are prevalent, where malicious sites mimic social media or banking login pages—one of the simplest ways to hack your account. A way to spot fake sites is by checking the URL: If it looks similar but not identical to the trusted site (e.g., "Faecbook" instead of "Facebook"), it’s a fake.
- For example, only enter your Twitter login details on Twitter’s official site. Avoid doing so on other sites requesting login credentials to share posts or similar actions.
- An exception is when universities use existing services (like Gmail) through their homepage.
Secure Your Phone
Change your phone password regularly. The first step in protecting against unauthorized access or data theft is setting a hard-to-guess password and updating it frequently.
- Ensure each change introduces a completely new password—avoid minor tweaks like altering a single number.
- Most phones allow you to set "complex" or "advanced" passwords that include letters and special characters alongside numbers.
Use Touch ID whenever possible. While you may still need a screen lock password, enable Touch ID on supported devices for payments and other services.
- As always, minimizing password entry on any platform is a good practice.
Browse using secure web applications. While third-party browsers like Tor or Dolphin may seem appealing, syncing your Google Chrome or Safari accounts across your phone and computer eliminates the need to re-enter saved passwords and protects your device from unsafe websites.
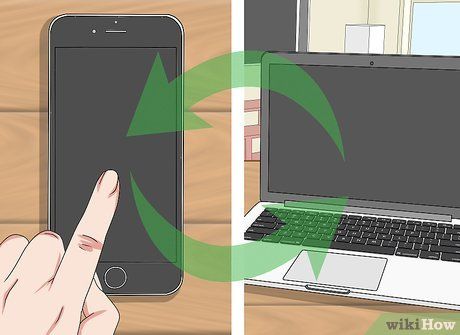
Update devices and software promptly. As soon as updates are available—whether for an app like Facebook or your entire operating system—install them immediately if possible.
- Many updates include patches that fix vulnerabilities and address security issues. Delaying updates can leave your device exposed to exploitation and attacks.
- Enable automatic updates if available to avoid unnecessary complications.

Charge your phone using trusted USB ports. This includes ports on your computer and in your car (if applicable). Public USB ports, like those in coffee shops, can expose your data to risks.
- For this reason, carry a power adapter and USB cable when traveling.
Secure Your Computer
Secure Your Network

Use secure wireless networks. Generally, secure networks require a password before connecting. In some places (like airports or coffee shops), you may need to purchase something to access the password.
- If a wireless network is insecure, your computer will warn you before connecting. Some operating systems even display an exclamation mark next to the network name.
- If you need internet access but lack a secure network, change your passwords immediately upon connecting to a secure network.
- If you have a home wireless network, ensure it’s secure and encrypted. Remember, wireless routers are often insecure by default—you must configure them yourself.
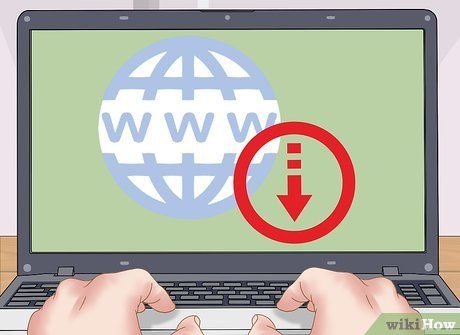
Only download programs from trusted sites. Be cautious when visiting websites over insecure connections. If you don’t see a lock icon to the left of the URL and "HTTPS" before the "www" in the address, avoid the site (and downloading anything) if possible.
Learn to identify fake websites. Beyond avoiding sites without "HTTPS" and a lock icon, carefully inspect the URL before entering passwords. Some sites aim to steal login credentials through phishing. Look for extra (or missing) characters, hyphens between words, or unusual symbols.
- For example, a fake Facebook site might use faceboook.com.
- Websites with hyphens between words (between "www" and ".com") are often untrustworthy.
Avoid using file-sharing services. File-sharing often violates intellectual property laws, and such sites may collaborate with hackers. You might think you’re downloading a hit song or a new movie, but the file could be a virus or malware in disguise.
- Many files are cleverly designed to hide viruses or malware, evading detection by antivirus software. The virus won’t harm your system unless you attempt to open the file.
Only shop on secure websites. Never enter account or credit card information on sites without "https://" before the "www" in the URL. The "s" ensures the site is secure. Sites without it do not encrypt or protect your data.
Advice
- There are numerous free and paid firewalls and antivirus software available online for you to choose from.
- Ensure your password is different from your username or email.
Warning
- Unfortunately, the only way to guarantee absolute safety and never get hacked is to completely avoid technology.
