Discovering intimate conversations, photos, and messages leaked online is not just an invasion of privacy but also disrupts personal life. Despite numerous politicians and celebrities falling victim to mobile phone hacking, there are now ways to protect your device. This article provides information to help you and your loved ones avoid scandals related to phone breaches or becoming victims of privacy violations by hackers.
Steps
Protecting Yourself

Adopt a proactive protection mindset. This doesn’t mean being paranoid but accepting the reality that someone might want to hack your personal information for malicious purposes. For example, an ex-partner, someone who dislikes your actions, or former friends. You can’t predict how quickly relationships might sour, so it’s best to always secure your personal information properly.
- Use passwords. You might feel safe because you never gossip, but that’s no guarantee. If someone wants to hack your account, a password is what stops them. People hack mobile phones not just for personal information but also to access more detailed and private data, often about family, friends, or acquaintances. This is information you need to protect carefully, alongside bank account details and transaction messages.
- Don’t share your password. If you trust someone enough to ask for help, like a spouse, change the password afterward.
- Don’t let outsiders know your password. Set passwords when in public places.
- Avoid programming passwords into your mobile phone.
- Don’t store private data on your phone for long periods. If hackers breach your email account, all data could be lost (often permanently). Even if you reset your password and log back in, you won’t be able to access previous information.
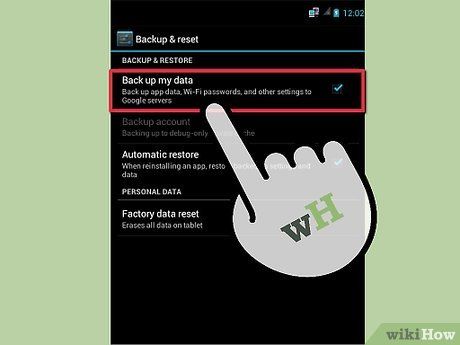
Back up important emails, files, or photos from your mobile phone to another device. Regularly back up your personal computer or tablet.

Think critically, don’t assume. Could a personal conflict lead to your information being stolen? Imagine the worst-case scenario of your phone being hacked and plan accordingly. Develop a habit of not storing sensitive information on your phone, deleting important details after reading, or backing them up elsewhere. If your phone doesn’t contain critical data, losing or having it stolen won’t be a major concern. Be thoughtful and avoid using your smartphone carelessly.
Set Stronger Passwords
Set a password to protect your voicemail. Ensure that careless individuals can’t delete personal voicemails by setting a protective password.
- Follow on-screen instructions to set a password for direct or remote voicemail access. Many systems allow voicemail access from other devices, making it easier to attack if no password is set.
- Many phones have default voicemail passwords (often easy to guess). If you use this feature, change the password immediately.
- Too difficult? Lost your phone data? Contact your service provider for assistance.

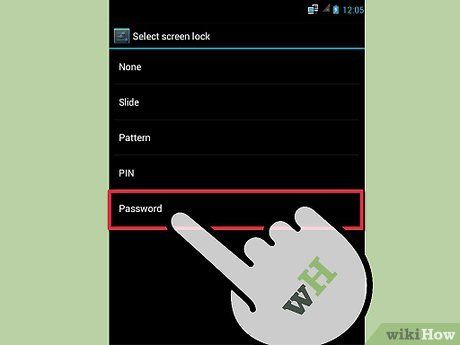
Choose hard-to-guess passwords. Simple passwords are easy to remember, but if they relate to birthdays, phone numbers, or consecutive sequences, the risk is high.
- Avoid using passwords related to birthdays, anniversaries, or consecutive numbers. Hackers often try obvious choices like birthdates of you, your family, or pets. Many people use obvious passwords like “1,2,3,4,5,” thinking hackers will overlook them, but this is a mistake.
- Don’t use names of pets or middle names in passwords. Names and recognizable words are quickly cracked if someone knows you well. Information you share online (Facebook, LinkedIn, Twitter, forum posts, etc.) shouldn’t be part of your password.
- Create complex passwords with uppercase letters, numbers, and symbols. The more complex the sequence, the higher the security. Use uppercase letters in the middle of the sequence and add symbols for extra complexity. Refer to online guides for creating secure passwords.

Do not use the same password for all phone accounts. While using multiple passwords can be confusing, the most effective way to protect your mobile phone (and your information in general) is to set unique passwords for each account accessed on your phone.
Regularly update your passwords. Don’t forget to change your passwords frequently to maintain security. Daily updates aren’t necessary, but occasional changes are recommended.
- Schedule password updates. Whether weekly, monthly, or quarterly, stick to a consistent routine. You can jot down new passwords in a notebook each time you update them.
- When updating passwords, store them in a secure location away from your phone, bag, wallet, or anything related to your phone. Avoid keeping password lists in notebooks long-term, as losing them could expose all your information. Write passwords on separate sheets, label them as “school” or “home repairs,” and store them discreetly in case of theft.
Other Security Methods

If Bluetooth is enabled, turn off 'Discoverable' mode. This prevents nearby devices from detecting your Bluetooth. This is the default setting on most new phone models.
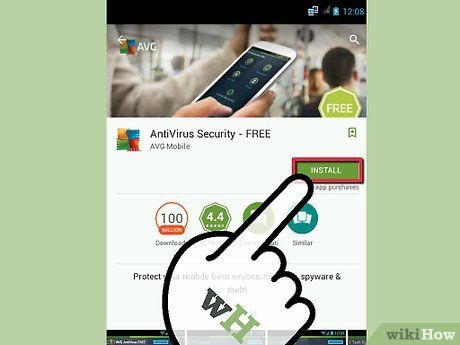
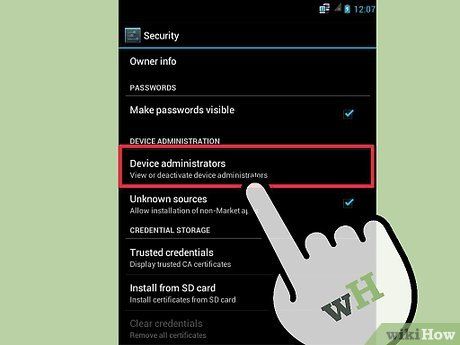
Install phone security software if your device allows it. Depending on your phone model, you may be able to download it for free or at a cost. For example, many phones lock access after prolonged use. Check if your phone has this feature. If your phone is stolen, this lock will prevent thieves from accessing your personal data.
- Contrary to popular belief, there are no “viruses” on phones. However, malicious apps designed to steal your information do exist. Security software scans your phone and alerts you if it detects harmful apps. This is especially useful for Android or jailbroken iPhones. Be cautious when downloading; only use trusted sellers or websites and heed any warning prompts.
- Look for apps that allow remote control of your phone in case of theft. Some apps give you full control over your phone if it’s stolen, helping you locate it or wipe all personal data stored on it.
- Remember to protect security app settings with a unique password if the feature is available.
Tips
- Always keep your phone with you (or know its location).
- Avoid clicking on links in emails from untrusted sources, as this could expose your personal information.
- Smartphones are like computers; be cautious about what you view, the websites you visit, and any data or images stored on the device.
- Turn off Wi-Fi when not in use.
Warnings
- If you’re considering hacking someone’s phone (accessing their voicemail system without permission), think again, as this could lead to serious consequences. Additionally, in many countries, this behavior is considered illegal.
