Torrenting is one of the simplest methods to obtain any file you need. However, the nature of torrenting makes it highly vulnerable to viruses or being detected for downloading illegal content. By taking certain precautions, you can reduce the risk of virus infections and avoid being caught downloading unauthorized material.
Steps
Preventing Viruses

Install antivirus software. A reliable antivirus program will protect your computer from harmful torrents. Windows comes with Windows Defender pre-installed, which can block most types of viruses. You can activate Windows Defender from the Control Panel as long as no other antivirus software is installed. If preferred, you can install third-party antivirus programs like BitDefender or Kaspersky. Regardless of your choice, only one antivirus program should be installed on your system.
- Refer to guides on installing antivirus software for more details.
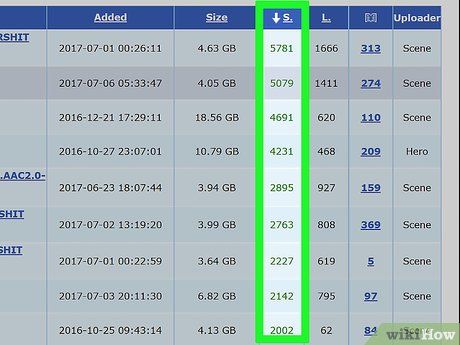
Look for torrents with many seeders. A high number of seeders indicates that the torrent is likely virus-free, as others have already checked and shared it without issues. While not a guarantee, this can help narrow down your options. Torrents with more seeders also download faster.

Check comments before downloading. Although not foolproof, comments can help you determine if a torrent contains viruses. If no comments mention viruses, the torrent is likely safe. If there are multiple warnings about viruses, avoid downloading it.
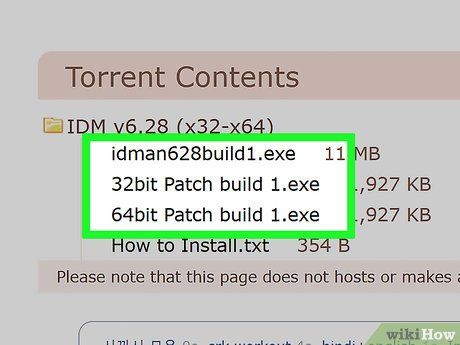
Avoid files prone to viruses. Avoid downloading program files, especially executable files (EXE, BAT), as they are most likely to contain viruses. Cracked software is among the riskiest files to download via torrent.

Join private torrent communities. If invited to a private torrent community, you are less likely to encounter virus-infected torrents. These torrents are created and shared by trusted members, making them more reliable. Gaining access can be challenging, as you typically need an invitation from someone within the community. The best approach is to engage in online communities and build connections with members who have access.
Avoid Detection

Understand how torrent connections work. When downloading a torrent file, your IP address becomes visible to others sharing the torrent. This is necessary for the torrent program to connect with other users, but it also makes you susceptible to detection by torrent monitoring organizations, including your internet service provider (ISP) and copyright enforcement agencies. You can take certain steps to reduce risks and prevent your ISP from throttling your connection speed.
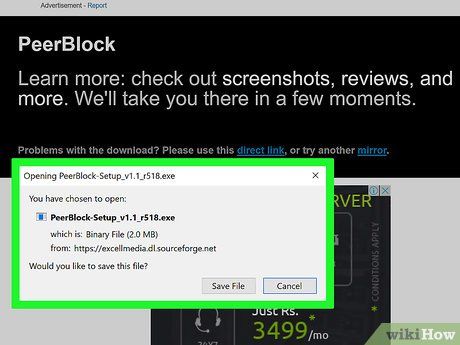
Install PeerBlock. PeerBlock is a program that blocks known torrent tracker IP addresses. It prevents your computer from connecting to these IPs, particularly stopping them from participating in your torrent traffic. While not a perfect solution, as your ISP can still detect torrent activity, it is a quick and simple way to reduce the risk of receiving warnings from organizations like the RIAA or MPAA.
- You can download PeerBlock for free from peerblock.com. Follow the instructions to install and launch PeerBlock. The program runs in the background, blocking connections to notorious IPs. Use the "P2P" list from Bluetack for basic torrent protection during initial setup.
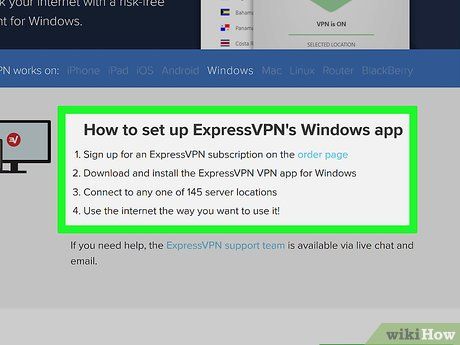
Consider using a VPN service. To maintain anonymity while torrenting, you can subscribe to a VPN (Virtual Private Network). For a few dollars per month, you gain complete privacy while browsing. Your ISP won’t know you’re transferring torrent data, preventing bandwidth throttling. Tracking organizations won’t see your real IP, eliminating the risk of receiving warning notices.
- VPN services have some limitations. First, they are not free, so you must weigh the cost against the benefits. Internet speeds may decrease as traffic is routed through the VPN server before reaching your device. Connecting to a VPN in another country can significantly reduce speed. Lastly, some VPNs may log data and share it with authorities, though you can find no-log services.

Choose and subscribe to a VPN service. There are numerous VPN services with varying prices, structures, and privacy policies. Carefully read the terms of service, and avoid VPNs that log detailed records. Additionally, not all VPNs allow torrenting. Below are some popular VPN services, but you can find many others through a Google search. Avoid free VPNs and proxies, as they are not secure. Many paid VPNs operate outside the U.S. due to lenient data retention laws.
- PrivateInternetAccess
- TorGuard
- IPVanish
- IVPN
Find VPN connection details. When you subscribe to a VPN service, you’ll receive connection information. This includes the VPN server address, username, and password. You may need to log in to the VPN’s website to retrieve these details.
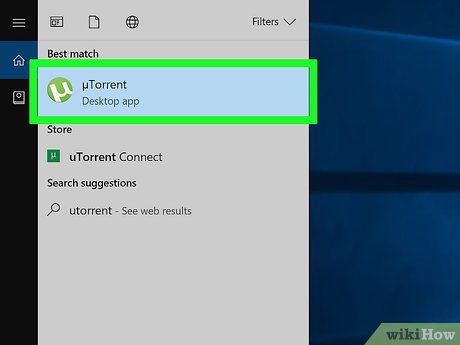
Open the torrent program. After subscribing to a VPN service, you need to configure your torrent program to connect through the VPN.
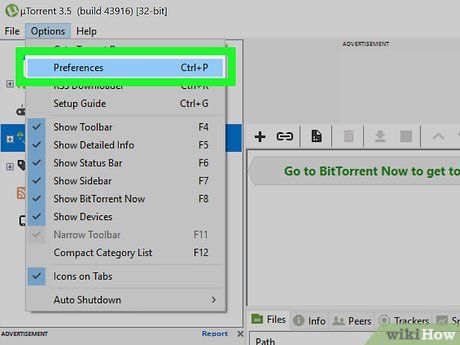
Open the Options or Preferences menu. You can find this option in the Tools or Options menu at the top of the torrent program.
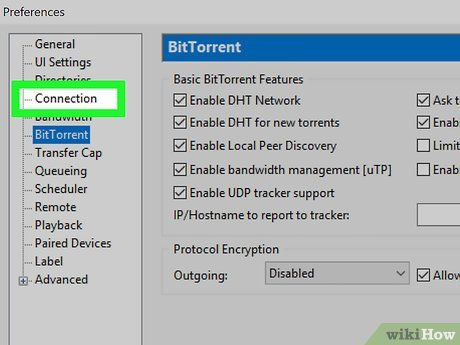
Click on the "Connection" tab. This tab allows you to adjust connection settings, including adding VPN connection details.
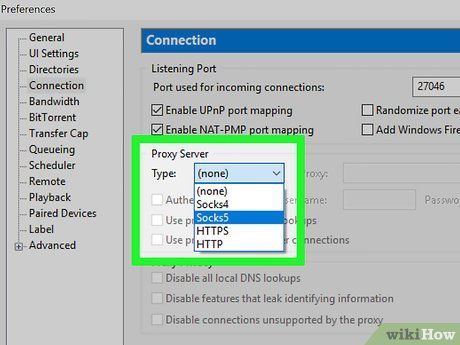
Select the VPN type from the "Type" menu under "Proxy Server." Most VPNs use SOCKS5. Double-check your VPN connection details if you're unsure.
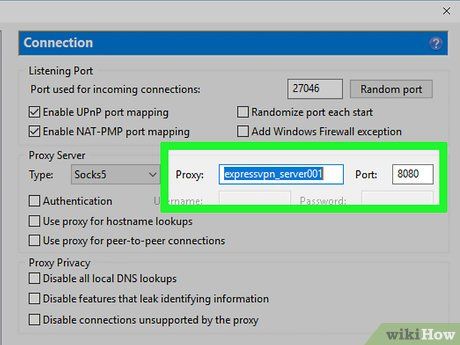
Enter the VPN address and port. You can find the connection details by logging into your VPN's website. Many VPN services offer multiple servers to connect to, which can improve internet speed.
- Don’t forget to check the box for "Use proxy for peer connections."
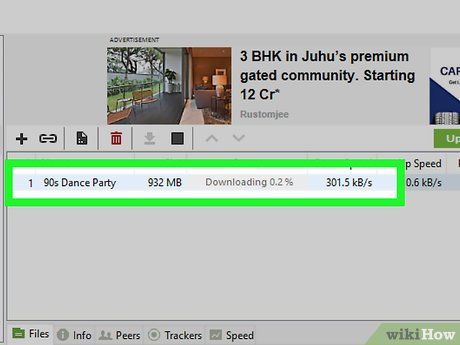
Start downloading the torrent. Once your VPN is configured, you can proceed to download torrents anonymously. While no VPN guarantees 100% anonymity, it significantly reduces your risks.
Warnings
- Downloading copyrighted files without permission from the copyright holder is illegal (unless protected under fair use).
