Learn how hackers can secretly access your computer, steal your identity, or pilfer your financial information without your knowledge — until it's already too late. Understanding how hackers operate is the key to defending yourself. By familiarizing yourself with these basic tactics, you can reduce your risk of becoming a target while navigating the digital world, all without needing to grasp complex technical jargon.
10. Drive-By Downloads
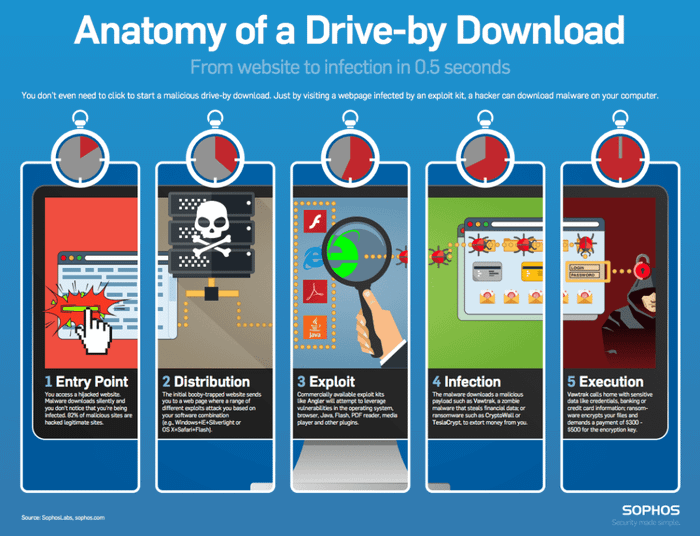
This term sounds frightening, and it is, as it can occur while visiting a website you normally trust. If a site you visit has been compromised, it may look normal, but in reality, it could be silently scanning your device for weaknesses and installing malicious software through any available method. Once this happens, the hacker could steal your data, track your activity, spy on you through your webcam, and more.
If your device isn't up to date or properly patched, a drive-by download attack can easily install harmful software, giving a hacker full control over your system. Keep your devices updated and use up-to-date antivirus and anti-malware software to protect yourself.
9. Cross-Site Scripting (XSS)

Hackers can exploit vulnerabilities in a website's JavaScript code to access the cookies saved in your browser, potentially stealing your personal details or login credentials for that website — and others. In more severe cases, they could even swipe the contents of your clipboard, additional website cookies, and your usernames/passwords.
Much like drive-by downloads, this type of attack can occur when visiting seemingly safe websites. Unfortunately, the website owner is often unaware that any of this is happening in the background.
8. Public WiFi

Be cautious about using WiFi in places like coffee shops or airports, as a malicious hacker could be posing as a legitimate WiFi access point, hoping you'll connect and attempt to log into your bank account. They may also be monitoring all traffic on the otherwise secure WiFi network, searching for vulnerabilities in your system, and more. Always use a VPN, enable a firewall on your device, and ensure everything is up to date when using free WiFi.
7. Phishing

Be cautious about what you click or open in your inbox! Hackers are skilled at creating fake emails with harmful attachments or links to dangerous websites designed to breach your computer. These deceptive emails may even appear to be from trusted organizations, like your bank.
Remember, most banks and reputable websites will never ask you to click a link to log in (unless it's a password reset email). If you do click on such a link, verify that you're on the correct site before entering your credentials.
As for email attachments, only open them if you were expecting them, and make sure they come from someone you trust.
6. Reused Passwords

The more often you reuse the same password across multiple accounts, the higher the likelihood that your accounts will be breached. To help manage the overwhelming task of having a unique password for each site, consider using a password manager, with various options available from free services to premium subscriptions.
5. Malware

Malware can come from numerous sources, and it's not just about pop-ups or pestering you with antivirus software prompts. It has the ability to turn your computer into a ‘zombie,’ which a hacker can activate whenever they choose. In many instances, hackers control large ‘botnets’ made up of thousands of these zombie computers to target individuals, companies, governments, or websites. Before you know it, your device is part of a cyberattack.
Avoid downloading software from unreliable sources and ensure your antivirus is always up to date (a common piece of advice, but crucial!).
4. Unsafe Thumb Drives/Media

Unless you know exactly what’s on a USB drive because you bought it yourself, never connect an unfamiliar one to your computer. This rule also applies to SD cards, CDs, and DVDs. Malicious software can automatically run and infect your device without you even realizing it.
Did you find a USB drive in your workplace parking lot and feel tempted to see what's on it? Don’t do it. Always ensure your computer has up-to-date antivirus software, including for Mac users, to help protect against such risks.
3. Hotel Computers/Kiosks

Avoid logging into any accounts, including banking or email, on public computers in hotel business centers. These machines could easily compromise your accounts.
You can never be sure what threats are hiding on shared public computers since you have no idea who used them before you, and the hotel staff probably doesn’t either.
2. Your Outdated Computer
Still using Windows XP? It's time to disconnect and step away from your computer. It's now highly vulnerable and no longer receives updates from Microsoft. Failing to keep your operating system and software up to date makes it far easier for hackers to breach your system, often through one of the other methods mentioned here.
As irritating as it may be to install updates and restart your computer, it is absolutely essential to stay secure online.
1. Compromised Ad Networks

Hackers often infiltrate trusted websites by targeting the ad networks they use to display advertisements. This method has affected many reputable sites, including major news organizations, and can lead to major security breaches for visitors if malicious ads are being shown.
Although it’s a point of debate, using an ad-blocker in your web browser is one of the most effective ways to protect yourself. While ad-blockers may prevent websites from earning revenue through legitimate ads, they also guard you from the risk of being hacked when those ads are compromised by malicious actors.
