Hackers have existed far longer than most people realize. The practice didn’t begin with the Internet—individuals have been breaking codes and infiltrating systems as soon as it became possible.
Long before computers emerged, hackers were already making their mark by infiltrating telephone systems, manipulating punch-card machines, and even tampering with telegraph networks. Some hackers sought profit, others acted out of altruism, while a few simply enjoyed the time-honored tradition of pranking.
10. Nevil Maskelyne Disrupted a Wireless Telegraph Demo: 1903
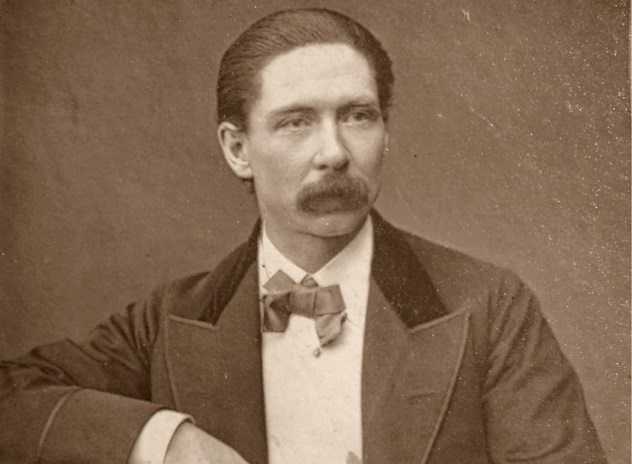
The moment it became physically feasible to hack into something, someone did it. That someone was Nevil Maskelyne, the first hacker in history, and he was active far earlier than you might think. In 1903, he hacked into a live telegraph demonstration.
Maskelyne didn’t even wait for wireless telegraphs to hit the market; he infiltrated one of the first demonstrations. The inventor, Guglielmo Marconi, was showcasing the system to prove its security and confidentiality to the public, claiming that any message transmitted via his wireless telegraphs would remain entirely private.
But as the demonstration began, the telegraph started sending out an unusual message. First, it repeatedly beeped out the word 'Rats.' Then it began to transmit a limerick: 'There was a young fellow of Italy,' it mocked Marconi, 'who diddled the public quite prettily.'
Marconi was left humiliated in front of the audience. However, it didn’t take long for him to discover the identity of the culprit. Maskelyne took pride in his actions, publishing papers boasting about his achievement. He claimed it was for the greater good, to warn the public that if they were going to send messages wirelessly, they needed to understand that privacy wasn’t guaranteed.
9. Rene Carmille Hacked the Nazis’ Database of French Jews: 1940

Rene Carmille is often recognized as the 'first ethical hacker' in history, and it's clear why he earned that distinction. As a member of the French Resistance during the Nazi occupation, his hacking efforts helped save thousands of Jewish lives.
Carmille was an expert in punch-card computing and owned the very machines the Vichy regime in France used for data processing. When the Nazis took control, he discovered they were using these punch-card systems to track and target Jews. Offering to let the Nazis use his machines, Carmille wasn't driven by hatred—he had a plan. He secretly altered the machines so that no matter what data the Nazis entered, no one was ever labeled as Jewish.
For nearly two years, Carmille successfully convinced the Nazis that his machines simply weren't functioning properly. However, when they finally discovered what he had done, they retaliated. In 1944, they broke into his home and sent him to the brutal Dachau concentration camp.
Carmille's actions ultimately led to his death, but the cost was small in comparison to the lives he saved. By the time the Nazis apprehended him, he had already protected thousands of people.
8. David Condon: The First Phone Phreak – 1955

In the 1960s and 1970s, a subculture of individuals known as 'phone phreaks' emerged, hacking into telephone networks. These phreaks discovered that by playing specific sounds into a phone, they could tap into any part of the network. While many of them simply used this knowledge to make free calls, the potential was far greater than they initially realized. In fact, by the 1990s, one phone phreak even convinced a judge that he could hack into nuclear codes.
The first person to crack this code was David Condon. In 1955, Condon used his Davy Crockett Cat and Canary Bird Call Flute to whistle into a phone, marking the first-ever experiment with a theory about how phone systems functioned.
The sound of his whistle was a secret code that the telephone system recognized. The system, assuming he was an employee, connected him to a long-distance operator who, believing she was speaking with a colleague, would then connect him to any phone number he requested—free of charge.
Though Condon only used his discovery to save a few cents on long-distance calls, he unknowingly sparked the birth of an entire movement. The phone phreaks would eventually lay the foundation for the first computer hackers, and it all started with one man and a toy flute.
7. Joybubbles: The First Person to Hack by Whistling – 1957
Though Condon is credited as the first phone phreak, he wasn’t the one who sparked the movement. That honor goes to Joe Engressia, better known as 'Joybubbles.'
Joybubbles was a blind prodigy with perfect pitch, capable of replicating any note he heard, capturing even the smallest tonal variations. At the age of seven, he realized he could use this gift to break into the phone company’s system. His pitch was so accurate that he didn’t need any gadgets—he simply pursed his lips and whistled. The phone system, thinking it was a programmed signal, would connect him wherever he desired.
He made a modest income by charging friends a dollar to hack into their phones and allow them to make free long-distance calls. In 1971, his fame grew when Esquire published an article about him and the phone phreaking scene.
The article brought both attention and trouble. Joybubbles was arrested for fraud related to his hacking the same year. However, he claimed the arrest was intentional. Joybubbles believed that being arrested would give him the opportunity to convince a telecom company to hire him for security work, allowing him to finally earn more than $1 per phone call for his skills.
6. Allan Scherr: The First Person to Hack a Computer Password – 1962

The first computer to be secured with a password was also the first to be compromised. Thanks to Allan Scherr, it happened far more than once.
In 1962, MIT introduced the first computer passwords. The university had a few computers that students had to share, and they wanted to provide some privacy. To accomplish this, students were required to log in with a password—and to prevent them from monopolizing the machines, each account had a daily four-hour limit.
Allan Scherr, a student, quickly grew frustrated with the time restrictions. He created a punch card that tricked the system into printing all the passwords, and he used them to log in as other users whenever his time expired.
Scherr also shared the passwords with his friends, and before long, the first computer troll was born. They used the passwords to hack into their professor's account and leave mocking messages behind.
5. MIT Phone Phreaks: The First People Called 'Hackers' – 1963
The term 'hacker' was first used by an MIT professor named Carlton Tucker, but he didn’t intend it as a compliment.
In 1963, a group of phone phreaks targeted MIT, breaking into the school's phone network. They used it to flood the system with calls to Harvard, blocking others from making any calls. Then they made random long-distance calls, charging them to a radar facility, mostly to cause disruption.
Tucker became furious and coined a term that would go on to shape history. Although 'hack' was already used at MIT to describe working on electronics, he used it to describe the phone phreaks, calling them 'hackers' for the first time.
However, Tucker wasn’t pleased with the new label. He issued a warning to all hackers at MIT, stating: 'If any of these people are caught, they are liable to be put in jail.'
4. RABBITS: Likely the First Computer Virus – 1969

The earliest known computer virus might have been a program named RABBITS. Its creator remains unknown, and so does its purpose, but it was responsible for taking down the University of Washington Computer Center.
The program was small and unassuming, but it reproduced itself – much like rabbits, as its name implied. In 1969, someone installed it on a computer at the university, and it began duplicating. Each new copy created more, eventually overwhelming the computer and causing it to crash.
Five years later, someone inspired by this story created their own rabbit virus, named Wabbit. They deployed it on ARPANET, an early version of the Internet, in an attempt to disrupt another user. This marked the first-ever computer virus used in a denial of service attack.
3. John Walker Created the First Trojan Horse Virus – 1975

John Walker became the first person to deceive others into installing a virus on their computers, two years before personal computers were even available for home use.
While Walker may have created a computer virus, he maintains that he had good intentions. He developed a popular game called ANIMAL, which attempted to guess the animal the player was thinking about. It became such a hit that all his friends wanted a copy.
The challenge in 1975 was that the only way to share the game was by creating a magnetic tape and mailing it to friends. With limited time, Walker decided to take a more efficient approach – infecting as many computers as possible with his game.
He modified the game so that while people played it, it secretly duplicated itself across all directories it could access. This meant it would spread to other users' directories and to any tape inserted into the machine. If that tape was then used on another computer, Walker’s game would infect that machine too. So when someone asked Walker for a copy of ANIMAL, he could just tell them to check their computer – they likely had a copy without realizing it.
Walker insists he did this out of kindness. At least, that’s part of the story – the other part was to show the world, in his own words, 'what could have happened if I were not a nice guy.' So perhaps his actions were a mix of goodwill and a desire to teach others to fear him.
Steve Jobs and Steve Wozniak, before making billions with computers and iPods, started their careers with something very different: hacking into phone systems.
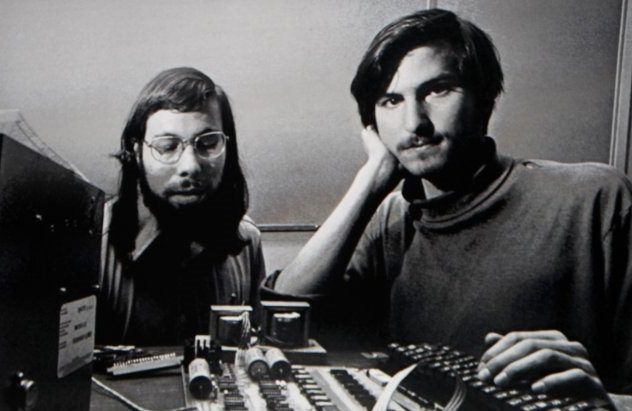
Before their immense success in the tech world, Jobs and Wozniak’s first taste of the hacker life came from a different venture – infiltrating phone systems.
Wozniak became fascinated by an article in Esquire about Joybubbles and the world of phone phreaking. He was so intrigued that he sought out one of the people mentioned in the article, John 'Captain Crunch' Draper, inviting him to his home.
After learning the tricks of phone hacking from Captain Crunch, Wozniak crafted a device known as the blue box to make it easier to break into phone systems. He put it to use immediately, and at one point, he even called the Pope pretending to be Henry Kissinger as part of his pranks.
When Steve Jobs heard about the idea, he realized there was a business opportunity in it. The two began mass-producing Wozniak’s blue boxes and selling them to their classmates, with Wozniak handling the tech side and Jobs overseeing the sales. And that's how Apple was born: the founders of one of the largest companies in the world making money by scamming phone companies.
1. Ray Tomlinson And Bob Thomas Introduced The First Virus To The Internet: 1971
Ray Tomlinson, the inventor of email, was also the first to send a virus over it.
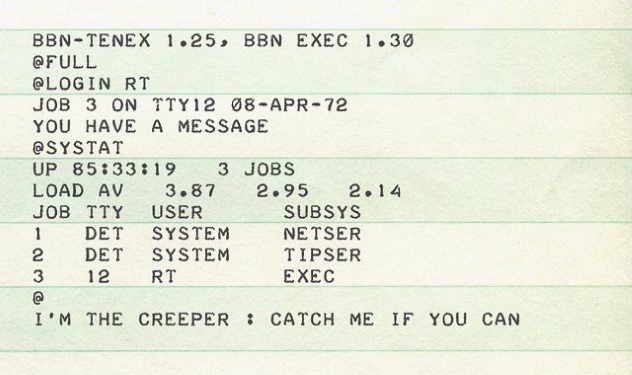
This virus, named Creeper, was the first-ever computer worm. The program replicated itself across ARPANET, leaving behind a message on terminals: 'I’m the creeper: Catch me if you can.'
Although the virus was initially created by Bob Thomas, a colleague of Tomlinson, it was designed to be harmless. The file would simply jump from one computer to another, erasing itself once it had moved on.
However, Tomlinson decided to tweak the virus, ensuring it wouldn’t disappear and instead would slow down a computer until it eventually crashed. Almost immediately after the Internet was born, he uploaded the first virus that could potentially take it down.
So, it turns out that when your inbox is flooded with spam and viruses, your email is actually working exactly as its creator envisioned.
