As technology becomes more embedded in our daily routines, an increasing array of items is becoming vulnerable to cyberattacks. This is a growing issue that’s expected to worsen, particularly since many businesses offer minimal protection or neglect cybersecurity entirely. Anything containing a microchip is at risk, including some unexpected devices.
10. Any Device Embedded in Your Body
You might think your heart is yours alone… unless you have a pacemaker. In that case, it can be hacked. Any medical device within your body that’s connected to the Internet is at risk. This is not just a hypothetical concern – it has already occurred.
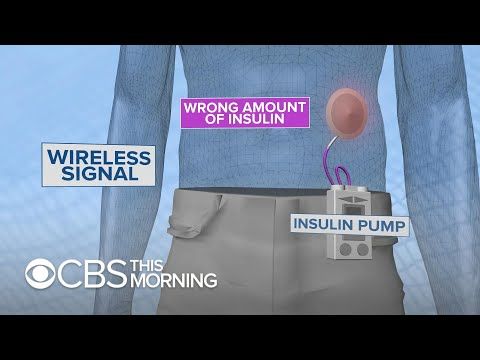
At the 2011 Black Hat Technical Security Conference, security specialist Jerome Radcliffe demonstrated the vulnerability of his own insulin pump by hacking it. He remotely disrupted the wireless signals to his device, replaced the data about his condition with falsified information, and sent it back. While Radcliffe didn’t alter his device to the point of endangering his health, a change in insulin dosage could have easily induced a coma or even led to death.
Radcliffe isn't the only one conducting this type of research. Barnaby Jack, a researcher at McAfee, discovered a method to scan and hack any insulin pumps within a 90-meter (300 ft) radius using their wireless connections.
The same vulnerability exists with heart defibrillators. When first implanted, these devices are tested using a radio signal that toggles the defibrillator on and off. Researchers have found that this signal can be intercepted and rebroadcast to control the device remotely.
9. Toilets

High-end Japanese toilets have been shown to be surprisingly vulnerable to even the most basic hacking attempts. Marketed in the US as a groundbreaking example of "toilet innovation," Satis toilets are operated via a smartphone app called 'My Satis.' However, a glaring flaw lies in the fact that the app uses the same Bluetooth PIN to connect to every toilet.
What could a toilet hacker do to you? The simplest hack would cause the toilet to continuously flush, driving up your water bill. The Satis also features an air purifier, automatic lid, in-bowl spotlight, and built-in sound module to mask the sounds of your activities. If a hacker targets you while you're using the toilet, they could manipulate these features, potentially causing "discomfort and distress" according to Satis, and increasing your electricity costs. However, with the toilet's $4,000 price tag, anyone able to afford it could likely manage the resulting spike in utility bills.
The most unsettling hack on a Satis toilet could be the two-nozzle bidet spray, which substitutes toilet paper with jets of water. While it may be simply inconvenient if it happens unexpectedly, it becomes much more embarrassing to realize that someone has interfered with one of your most private moments.
8. The Emergency Broadcast System
In Montana, the Emergency Alert System once broadcast a warning stating that “the bodies of the dead are rising from their graves and attacking the living.” The message was swiftly retracted, and the TV station issued an apology, attributing the bizarre alert to a hack of their Emergency Alert System.
The prank also took place in various other locations, including Michigan, during a broadcast of the children's show Barney. These were the first hacks of the system, which had previously been telephone-based. However, within a year of transitioning to a web-based system, hackers recognized its potential vulnerabilities and successfully breached it.
While the pranks caused no harm, they exposed the system’s weaknesses, particularly the fact that multiple models of Emergency Alert System decoders could easily be taken over. Although the zombie apocalypse warnings were obviously fake, more serious and potentially harmful messages could be broadcast just as easily. If false alarms became too frequent, the public might eventually disregard them.
Even after the company that developed the systems fixed one vulnerability to prevent hackers, the zombie apocalypse message demonstrated that the systems were still prone to human error. Many users neglected to change the default passwords, which is how these breaches occurred.
7. Almost Everything at Your Hospital

If you’re in a hospital and your equipment is connected to the Internet via an Ethernet cable, that equipment is likely highly susceptible to hacking. By searching for common medical terms on Shodan, a search engine that finds Internet-connected devices, researchers were able to identify machines like MRIs, X-ray scanners, and infusion pumps. Almost anything in the hospital connected to the Internet is at risk, whether due to intentional design or simple configuration errors. But what they found next was even more alarming.
A significant issue was that much of the medical equipment was using the same default passwords across different device models. Some manufacturers even cautioned that changing these default passwords might render the equipment ineligible for support, as the support teams rely on those passwords for servicing. Cybersecurity experts were able to easily compile a cloud of the most common login credentials and passwords.
To assess the extent of compromised devices, the researchers set up 10 computers designed to look like medical systems in order to attract hackers. They successfully received 55 login attempts, 24 exploits, and 299 malware samples.
The hacks could have various consequences. The most terrifying would be hackers remotely adjusting medication dosages, something that has already happened to patients. Medical records could be altered, potentially leading to incorrect treatments. Phishing scams could easily be created. Using internal healthcare provider networks, researchers managed to access details such as host names, descriptions, equipment locations, and the physicians assigned to them.
6. Smart Homes

The smart home industry is still in its early stages, and much of the technology falls short of modern cybersecurity standards. In 2015, a security firm tested 16 home automation devices and found only one that couldn't be easily hacked. Devices like cameras and thermostats lacked even basic security features, which is concerning for several reasons, including the potential for cybercriminals to use your behavior patterns to jeopardize your safety.
Homeowners who use smartphone apps to control their homes remotely are especially vulnerable to break-ins. A reporter from Forbes discovered that a series of keywords could be crawled by search engines, causing some homeowners' systems to show up in search results, leaving them exposed to anyone who wanted to take control.
A hacker could easily open a person’s garage door and gain access to their home. The specific model that allowed this exploit was recalled, but other systems still had a security flaw that made them controllable by anyone on the same Wi-Fi network.
The security flaws extended to nearly every device in the home that connects wirelessly. One hacker gained control of a family's baby monitor and began yelling profanities at their two-year-old daughter. While the girl, who was deaf, was unaffected, other incidents involving hacked baby monitors have been far more harmful.
5. Gas Pumps

Concerned that Internet-connected gas pumps could be exposed to hacking, cybersecurity experts set up fake pumps to attract potential hackers. Their concerns were quickly confirmed. Within just six months, there were 23 different attacks.
Research shows that some gas pumps have already been tampered with by hackers. Although no serious damage has been done so far, the risks are clear. Among the attacks, two were denial-of-service, which could have caused inventory disruptions and shortages. Four involved modifications to the pumps, and twelve were related to changes in pump identification, which could result in the wrong fuel being dispensed into a vehicle’s tank, potentially damaging the engine.
The fake devices (honeypots) were scattered worldwide, highlighting the global nature of the issue. Many automated tank gauges (ATGs), which monitor the volume, temperature, and water content of underground gas tanks, don’t have any password protection.
With ATG documentation accessible online, it’s alarmingly easy to compromise and disrupt service. The researchers found that the US and Jordan were particularly affected by honeypot attacks, and they suspect that groups like the Syrian Electronic Army or Iranian Dark Coder may be behind these incidents.
4. Airport Security

Cybersecurity experts are raising alarms that an airport’s security network could be entirely disabled by hackers. Many airport security devices, such as X-ray machines and itemisers (explosive detectors), have passwords embedded in their software. With the correct username and password, anyone could access the airport network. Hackers could manipulate an X-ray scanner to hide weapons or steal data on how to bypass security. Similarly, itemisers could be hacked.
After the vulnerability was discovered, the Department of Homeland Security issued a warning regarding these passwords. However, experts caution that some airports may have already been compromised. In 2015, a security firm claimed that an Iranian group had breached supposedly secure information from multiple airports. The firm warned that anyone with access to an airport’s emergency plans could potentially find ways to bypass security. Concerns about terrorism and how groups could use this information for attacks remain a serious threat.
Groups like ISIS have already targeted Hobart International Airport’s website, defacing it with a message supporting their cause. Polish airline LOT had to cancel or delay flights after a distributed denial-of-service attack crippled their flight planning computers.
3. Unopened PCs

A new PC is generally safe from hackers, but some Chinese-made computers were sold with preloaded malware. This malware was embedded in counterfeit versions of Windows OS and was used to spy on users and launch denial-of-service attacks.
Microsoft's investigation into the supply chain revealed that these computers were infected with a malware known as “Nitol.” The malware spread through removable drives, leading to the infection of millions of devices. When investigators bought 20 laptops and desktops from various 'PC malls' in China, each one had a counterfeit version of Windows. Three of the machines had inactive malware, while the fourth activated as soon as it was connected to the Internet.
The investigators concluded that the computers were infected after leaving the factory. The Nitol botnet was managed through the domain 3322.org, which hosted over 500 different strains of malware. Microsoft managed to shut down the malware and take control of the domain, now allowing legitimate traffic from its subdomains.
2. Your Car

In 2015, researchers demonstrated a 'zero-day exploit' by hacking a Jeep Cherokee and gaining wireless control of the vehicle while it was on the move. The exploit worked by sending commands through the Jeep’s entertainment system, which affected its dashboard functions.
During the test, the driver—a reporter who volunteered for the experiment—was cruising at 115 kilometers per hour (70 mph) when the researchers began manipulating the car’s systems. They cranked the cooling to maximum, changed radio stations, blasted music at full volume, turned on the windshield wipers, and started spraying wiper fluid, which obstructed the driver's view.
Despite the driver's attempts to stop the chaos, he had no control over the situation. The researchers even displayed their image on the car's digital screen and taunted, 'You’re doomed!' Before cutting the transmission, causing the vehicle to stop and forcing it off the road.
Though the reporter knew what was coming, the experience was still intense for him as it took place on a highway. The researchers noted that the situation could have been far more dangerous. Later in the test, they cut the brakes, sending the car into a ditch. They could have also forced the car to stop abruptly, resulting in a crash. While they haven’t yet mastered control over steering, they are actively working on it.
1. Airplanes have long been a symbol of human advancement, enabling rapid travel across the globe.

Despite improvements in airport security, the real threat might lie in the planes themselves. A researcher demonstrated how weak security could allow someone to gain access to a plane's systems. By purchasing authentic aircraft parts, he was able to simulate the data exchange between jets and air traffic control, ultimately showing that a smartphone app could be enough to seize control of key systems, such as the plane's steering mechanism, and even crash it into a building, bypassing the need for traditional bombs.
Chris Roberts, an IT expert, claims to have exploited the in-flight entertainment system of a passenger jet. By connecting his laptop to the Seat Electronic Box—found beneath each seat—he allegedly issued a 'CLB' command that caused the engines to respond by climbing, thus proving the vulnerability of modern aviation technology.
As newer aircraft systems become more interconnected, the risk of security breaches grows. Until airplane manufacturers address these flaws, the issue is likely to persist or even worsen over time.
