The right to privacy is universally recognized as a fundamental human right, falling under the category of first-generation human rights. However, in the age of technology, this right is increasingly compromised. Today, privacy remains a contentious issue globally, with differing definitions across borders. While technology brings numerous advantages, it has not made the protection of privacy any easier. In fact, technological advancements have only added to the confusion surrounding the true meaning of privacy as a fundamental right.
Ongoing security challenges continue to erode privacy protections. The need for constant oversight and monitoring is ever-present in today's world. Despite the many advantages technology offers, privacy often takes a backseat. In this article, we explore ten significant ways in which technology has compromised privacy.
10. The Hidden Dangers of Biometric Scanners

Thanks to technological advancements, we now rely on our eyes, fingerprints, and facial features for identification. Biometric scanners are fast, convenient, and highly secure. Beyond unlocking your phone, checking in at your workplace, and accessing secure areas, these scanners are used in creative ways. For example, some hotels and fast food chains use biometric scanners to recognize customers, tracking who placed an order first and what was ordered.
This might appear as just another routine action for unsuspecting customers and another useful technological innovation. However, when a system can track you based on your past activities, it becomes clear that it can store both short-term and long-term data. But what happens to that stored data? While there are policies and regulations that prevent companies from misusing customer data, trust is not always guaranteed. Despite their benefits, biometric scanners remain one of the most significant threats to privacy for unwitting users.
9. Voice Interception

Have you ever heard of Lawful Interception (LI)? It sounds as suspicious as it is. LI grants law enforcement the authority to monitor users of communication networks, provided they have the necessary permission. Essentially, a government agent can approach a Mobile Network Carrier (MNC) and demand access to communication channels and supporting data. This allows the agent to listen in on conversations of those under investigation, all without their knowledge. While this technology can be instrumental in solving crimes, it is also highly susceptible to exploitation if it falls into the wrong hands, which it often does.
Imagine sitting at home, sharing intimate thoughts with the love of your life—things that are meant to be heard only by each other—only to realize that a third party is secretly eavesdropping. Or perhaps you're sharing sensitive information with a colleague or business partner, only to discover that someone else is tapping into your conversation. Many people have lost property and money due to voice interception apps. While mobile phones are excellent for communication, users should be aware that using them can put their privacy at risk.
8. The Internet Never Forgets, and It's Never Full
Celebrities in the entertainment industry have often found themselves the victims of online data leaks and document exposures. However, this is mostly due to their public status and the influential roles they play in society. Many individuals have had personal photos, videos, or audio they would have preferred to keep private, leak onto the internet, stripping them of control. The internet continues to be rocked by incidents of vengeful ex-partners exposing intimate content of their former lovers.
Before the rapid growth of technology, intimate partners, political leaders, and influential figures didn't have to worry about the internet. Back then, disagreements would be settled privately, without publicizing personal issues. While technology has undeniably improved communication and other aspects of life, it has also exposed people to the risk of having their private documents, photos, audio, or videos leaked online. The most troubling part is how easy it is to share content online in ways that leave little trace. Once something is uploaded, it is nearly impossible to completely erase.
7. Online Cookies

Have you ever been browsing online and suddenly noticed an influx of emails or ads suggesting products or newsletters based on what you've been looking at? For example, after searching for the latest TV models, you start seeing ads for the best TV deals. While this might seem harmless, how did the advertisers know your interests? The simple answer: cookies!
When you visit a website and are asked to “accept or reject cookies,” the site owner is essentially asking for permission to monitor your online behavior. But the real question is: what else do cookies track? In fact, some websites won't allow you to proceed without accepting cookies—it’s as if you’re trading your privacy for access.
6. Video Conferencing, Webinars, and Chat Apps Don’t Offer Much Help Either

Zoom has become one of the most widely used teleconferencing platforms, especially after remote work became the norm. While it has proven invaluable in helping colleagues stay connected and ensuring that companies stay on track with their goals, there’s a trade-off. That trade-off, unfortunately, is your privacy.
Since the rise of teleconferencing apps, many embarrassing situations have unfolded. For example, a professional could be having an important meeting with colleagues, only to have a family member in the background unknowingly dancing half-naked, unaware that the camera is still on. It's no one’s fault; one person is trying to work, while the other is just living their life at home.
5. GPS Tracking
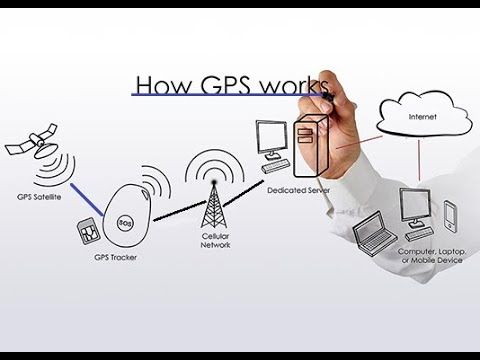
GPS, which stands for Global Positioning System, is an essential tool that people around the world rely on for navigation. Powered by satellites, it’s now a part of everyday life, with anyone carrying a smart device using it. The advantages of GPS are endless, but privacy is often compromised. For example, it’s common to see prompts on your phone asking for permission to access your location. You might wonder why these apps need that information.
Typically, authorities use GPS technology to pinpoint the locations of individuals of interest and monitor their movements. In a similar vein, malicious actors can exploit GPS to track victims through their smart devices. This can even extend to tracking their vehicles with basic GPS trackers. Simply put, GPS and privacy are not compatible.
4. Internet Service Providers’ Unchecked Power
Internet Service Providers (ISPs) are companies that supply internet connections for a fee. Customers then use these services for browsing, work, or entertainment—yet they do so under the watchful surveillance of their ISPs. It’s not uncommon to visit a website only to find it inaccessible, despite your connection working elsewhere. This is often the result of your ISP blocking access to that particular site.
ISPs have the ability to track your IP address and monitor the websites you visit. Who’s to say they can’t access your private data if they choose to? Unfortunately, to fully utilize technology, it’s nearly unavoidable that we must sacrifice some level of privacy.
3. Social Media Surveillance

Now, let's address the biggest offender: social media. With over 4.2 billion people across the globe engaging on various social media platforms, all of them require users to sacrifice a portion of their privacy. At the very least, you'll need an email address or mobile number, but there's no telling how far these platforms might go in invading your privacy.
2. Audio Recordings

Audio recording devices have become some of the most significant violators of privacy in the history of technology. Many people have unknowingly had private conversations that they thought were safe, only to later discover that their words had ended up in the wrong hands. Originally designed to assist journalists and businesses, these devices were soon exploited by malicious individuals to extort and intimidate their victims.
Modern technology now enables communication apps like WhatsApp to record and transmit voice messages. However, these recordings have often been misused, ending up in the wrong hands, leading to embarrassment and serious consequences for the individuals involved. Voice recordings differ from face-to-face conversations in significant ways.
1. Remote Desktop Applications

Remote desktop tools like TeamViewer and AnyDesk gained widespread popularity, particularly after the pandemic changed the world. These tools allow users to access their computers from a distance, provided there’s a stable internet connection. This makes it possible for colleagues to work remotely or for individuals to access important files and documents even when they don't have their own devices available.
As with any technology, using these applications requires compromising some level of privacy. For example, when you connect your computer to a colleague's for work, the other person gains the ability to access and modify almost all of your computer’s features (even those unrelated to work). Even if they pretend not to have seen something private on your system, chances are they have.
