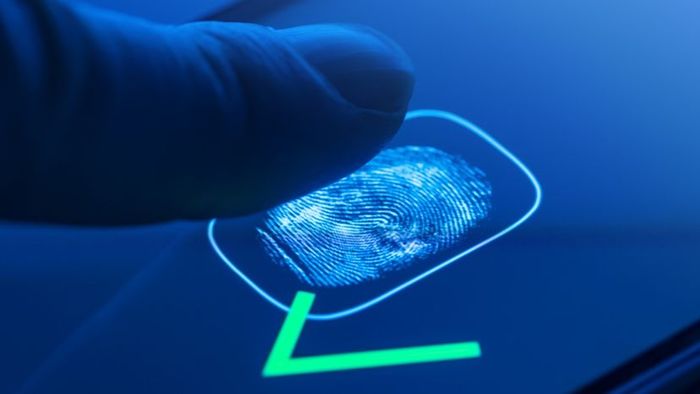
 Fingerprint recognition scanners? You've definitely encountered them. Jorg Greuel / Getty Images
Fingerprint recognition scanners? You've definitely encountered them. Jorg Greuel / Getty ImagesFor decades, digital fingerprint scanners have been a key feature in spy thrillers, but until recently, they were considered cutting-edge technology in the real world. In recent years, however, these devices have become commonplace — seen in police stations, secure buildings, and even built into PC keyboards. You can purchase a personal USB fingerprint scanner for under $100, immediately adding top-notch biometric protection to your computer. Rather than, or in addition to, a password, your unique fingerprint grants access.
In this article, we will dive into the exciting world of fingerprint scanners in law enforcement and identity protection. We will also compare how these systems perform relative to traditional password and ID card security methods, and explore where they might fall short.
Understanding Fingerprints

Fingerprints are one of those strange quirks of nature. Humans are born with built-in, easily accessible ID cards. You have a unique design that belongs to you alone, right at your fingertips. But how did this come to be?
Humans have small ridges of skin on their fingers because this particular trait was highly beneficial to the ancestors of our species. These ridge patterns and the valleys between them enhance the grip of the hands, much like the tread on a rubber tire helps it grip the road.
The second role of fingerprints is purely incidental. Like all aspects of the human body, these ridges are formed through a mix of genetic and environmental factors. The DNA code provides the general instructions for skin formation in a developing fetus, but the exact shape and pattern of each ridge is shaped by random events. Factors like the fetus's position in the womb and the composition of the surrounding amniotic fluid determine the formation of each ridge.
Beyond genetics, countless environmental factors also influence the formation of fingerprints. Much like how weather shapes clouds or the coastline of a beach, the development process is so unpredictable that it is virtually impossible for the same exact fingerprint pattern to emerge twice throughout human history.
As a result, fingerprints serve as a distinct identifier for each individual, even for identical twins. While two prints may appear nearly identical at first glance, a skilled investigator or advanced software can detect clear, unique differences.
This forms the foundation of fingerprint analysis, whether in criminal investigations or security systems. A fingerprint scanner's role is to replace a human analyst by capturing a print sample and matching it with stored records. In the following sections, we will explore how scanners accomplish this task.
Optical Scanner
A fingerprint scanner system has two primary functions: it must capture an image of your finger, and it must compare the pattern of ridges and valleys in that image with patterns from pre-existing records.
There are several methods for capturing an image of a person's finger. The most widely used techniques today are optical scanning and capacitance scanning. Both produce similar images, but they use entirely different approaches to achieve this.
At the core of an optical scanner is a charge coupled device (CCD), the same light sensor system found in digital cameras and camcorders. A CCD is essentially a grid of light-sensitive diodes known as photosites, which generate an electrical signal when exposed to light photons. Each photosite captures a pixel, a tiny dot representing the amount of light that struck it. Together, these light and dark pixels form an image of the scanned object (such as a finger). Usually, an analog-to-digital converter in the scanner processes the analog signal to produce a digital image. For more on CCDs and digital conversion, see How Digital Cameras Work.
The scanning process begins when you place your finger on a glass surface, and a CCD camera captures the image. The scanner is equipped with its own light source, often an array of light-emitting diodes, to illuminate the finger's ridges. The CCD system generates an inverted image of the finger, where the darker areas represent more light reflection (the ridges) and the lighter areas represent less reflection (the valleys).
Before comparing the captured print with stored data, the scanner processor ensures the CCD has recorded a clear image. It checks the overall pixel darkness, or the average values from a small sample, and rejects the scan if the image is too light or too dark. If rejected, the scanner adjusts the exposure time to allow more or less light, then attempts the scan again.
If the darkness level is appropriate, the scanner system then checks the image definition (sharpness of the fingerprint scan). The processor examines several straight lines moving both horizontally and vertically across the image. A high-definition fingerprint scan will show lines running perpendicular to the ridges, alternating between very dark and very light pixels.
If the processor confirms that the image is sharp and well-exposed, it proceeds to compare the captured fingerprint with those stored in the database. We’ll explore this process in detail shortly, but first, let’s take a look at the other major scanning technology, the capacitive scanner.
Capacitance Scanner
Just like optical scanners, capacitive fingerprint scanners create an image of the ridges and valleys forming a fingerprint. However, rather than using light to capture the print, capacitive scanners rely on electrical currents.
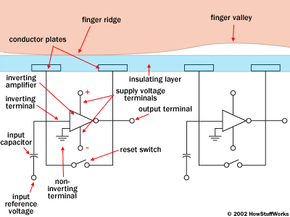
The illustration below depicts a basic capacitive sensor. It consists of one or more semiconductor chips that contain a grid of tiny cells. Each of these cells is made up of two conductor plates that are covered by an insulating layer. The cells are extremely small—smaller than the width of a single ridge on a finger.
This sensor connects to an integrator, an electrical circuit built around an inverting operational amplifier. The inverting amplifier is a complex semiconductor component made up of various transistors, resistors, and capacitors. The details of its operation would require an entire article to explain, but here, we can get a general idea of how it works in a capacitance scanner. (For a more detailed explanation, visit this page on operational amplifiers.)
Similar to any amplifier, the inverting amplifier adjusts one current based on variations in another (for further details, refer to How Amplifiers Work). Specifically, it modifies the supply voltage, based on the relative voltages of two inputs, called the inverting terminal and the non-inverting terminal. In this case, the non-inverting terminal connects to ground, while the inverting terminal is connected to both a reference voltage supply and a feedback loop. This feedback loop, which also connects to the amplifier's output, includes the two conductor plates.
As you might have guessed, the two conductor plates essentially form a basic capacitor, an electrical component that can store charge (see How Capacitors Work for further details). The surface of the finger acts as the third capacitor plate, separated by the insulating layers in the cell structure and, in the case of fingerprint valleys, a pocket of air. The capacitance (the ability to store charge) of the capacitor changes when the distance between the plates is varied by moving the finger closer or farther. Therefore, the capacitor beneath a ridge has a greater capacitance compared to the one under a valley.
To begin scanning, the processor first closes the reset switch for each cell, shorting the input and output of each amplifier to balance the integrator circuit. After reopening the switch, the processor applies a fixed charge to the integrator, causing the capacitors to charge. The capacitance of the feedback loop's capacitor influences the voltage at the amplifier’s input, which then alters the output. Since the distance between the capacitor and the finger affects the capacitance, ridges create a different voltage output than valleys.
The scanner’s processor reads the voltage output and identifies whether it corresponds to a ridge or a valley. By reading all cells in the sensor array, the processor can reconstruct an overall image of the fingerprint, similar to the one generated by an optical scanner.
The primary benefit of a capacitive scanner is that it captures an actual fingerprint shape, as opposed to the light and dark patterns representing a fingerprint’s visual impression. This feature makes the system more secure and harder to deceive. Furthermore, because capacitive scanners use a semiconductor chip instead of a CCD unit, they are generally more compact than optical scanners.
Analysis
In films and TV shows, automated fingerprint analyzers are often depicted overlaying different fingerprint images to find a match. However, this approach isn't particularly effective in real life. Smudges can distort the appearance of prints, making overlays inaccurate. Additionally, using the entire fingerprint image for comparison demands significant processing power and poses security risks, making it easier for someone to steal the fingerprint data.
Instead, most fingerprint scanners focus on comparing specific characteristics of a fingerprint, known as minutiae. Human and computer investigators typically focus on areas where ridge lines end or where one ridge splits into two (bifurcations). These and other distinctive features are collectively referred to as typica.
The software of the scanner system employs sophisticated algorithms to identify and analyze these minutiae. The fundamental concept is to assess the relative positions of these minutiae, much like identifying a constellation by the positions of its stars. You can think of it as visualizing the shapes formed by connecting the minutiae with straight lines. If two prints share the same shapes and dimensions formed by three ridge endings and two bifurcations, there's a high probability they come from the same print.
To establish a match, the scanner system doesn't need to find the exact minutiae pattern in both the sample and the stored print. It only needs to identify a sufficient number of shared minutiae patterns between the two prints. The specific number required varies depending on the scanner's programming.
Pros and Cons
Security systems use several methods to verify that an individual is an authorized user. Most systems typically rely on one or more of the following factors:
- What you have
- What you know
- Who you are
A "what you have" system requires a physical token, such as an identity card with a magnetic strip. A "what you know" system depends on you entering a password or PIN. A "who you are" system, however, seeks physical evidence to confirm your identity — like a specific fingerprint, voice pattern, or iris scan.
"Who you are" systems, such as fingerprint scanners, offer several benefits over other methods. Some of the key advantages include:
- Physical traits are much harder to replicate than identity cards.
- You can't guess a fingerprint pattern the way you can guess a password.
- You can’t lose your fingerprints, irises, or voice like you can lose an access card.
- You can’t forget your fingerprints as you might forget a password.
Although biometric scanners are highly effective, they are not foolproof and come with notable drawbacks. Optical scanners may sometimes struggle to differentiate between an actual finger and a photograph of one, while capacitive scanners could be deceived by a mold of someone's finger. If a malicious actor were to gain access to a legitimate user's fingerprints, they could bypass the scanner. In the worst-case scenario, someone could even sever a finger to gain unauthorized access. Some scanners include additional sensors to detect pulses and heat to ensure the finger is alive and not a fake, but even these features can be tricked by a gelatin mold placed over a real finger. (This site discusses various methods of bypassing a scanner.)
To enhance the reliability of these security systems, it’s beneficial to pair biometric analysis with another form of identification, such as a password. This is similar to how an ATM requires both a bank card and a PIN code for access.
The real challenge with biometric security is the level of damage caused if someone successfully steals identity information. If you lose your credit card or inadvertently reveal your PIN, you can always obtain a replacement card or change your code. However, if someone gets hold of your fingerprints, you're effectively stuck for life. You can't just replace your prints. Until you're certain that all copies have been destroyed, you can't use your fingerprints as a form of ID again.
Despite this significant drawback, fingerprint scanners and other biometric systems remain a strong means of identification. In the future, they will likely become an integral part of daily life, just like keys, ATM cards, and passwords are today.
