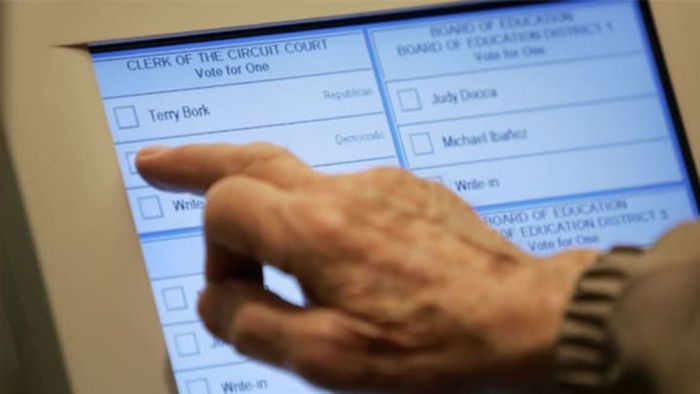
The problem isn’t merely small security flaws in these machines; it’s that they’re ridiculously vulnerable to hacking. Consider the touchscreen Diebold Accuvote system, which was anticipated to be used by nearly one-quarter of Americans to cast their votes in 2012. Yet, these machines have faced repeated criticism for security lapses over nearly a decade.
So, how insecure are these systems? In 2006, a professor of computer science at Princeton, along with his students, were examining the security of the system when they stumbled upon a surprisingly simple method to breach the Accuvote’s security. The machine logs votes on a memory card located behind a locked panel, but the lock is the same kind used on hotel minibars and jukeboxes. A widely accessible universal key can easily open it. Oops!
In September 2011, even more alarming news came from the Argonne National Laboratory’s Department of Energy. A team of computer scientists from the lab’s Vulnerability Assessment team created a device that could attach to the Accuvote’s circuitry and instantly alter voter ballots. The most frightening part? The components needed to create the “alien electronics” for hacking the system only cost $10.50. For another $15, hackers could add a remote control that allows them to alter ballots from up to half a mile away. This means that while candidates spend millions on campaigns, all it takes is $26 and a basic science knowledge to undermine democracy.
This article was first published in the January-February 2012 issue of mental_floss magazine under the title 'The Most Important Questions of 2012.'
