 The United States depends on key figures like Gregory Garcia from the Department of Homeland Security to protect the nation from cyber threats. Explore more images of computer hardware.
Scott J. Ferrell/Congressional Quarterly/Getty Images
The United States depends on key figures like Gregory Garcia from the Department of Homeland Security to protect the nation from cyber threats. Explore more images of computer hardware.
Scott J. Ferrell/Congressional Quarterly/Getty ImagesAttention, soldier! Not every battle unfolds on rough terrain, the open sea, or in the skies. Today, some of the most intense combat occurs within digital networks. Instead of bullets and bombs, the warriors in these battles wield bits and bytes. But don’t be fooled into thinking that digital weapons don’t have real-world impacts. The truth couldn’t be more opposite.
Think about all the critical systems in the United States linked to the Internet:
- Emergency response services
- Financial markets and banking infrastructure
- Power distribution networks
- Water and fuel pipelines
- Military defense systems
- Telecommunication networks
This is just the start. Consider all the essential services and systems we rely on to keep society functioning smoothly. The majority of them operate on computer networks. Even if network administrators isolate their systems from the wider Internet, they could still fall victim to a cyber attack.
Cyber warfare is a growing threat. Unlike conventional warfare that demands extensive resources like troops, weapons, and equipment, cyber warfare requires only a person with the right expertise and computer tools to cause chaos. The enemy could be anywhere, even within the country being targeted. A significant attack could be carried out by just a handful of hackers using standard laptop computers.
Another alarming feature of cyber warfare is that a cyber attack can either be part of a coordinated national assault or simply the work of a rogue hacker looking to cause mischief. By the time the target identifies the nature of the attack, it might already be too late. Regardless of intent, cyber attacks can inflict billions in damages. Many nations are not adequately prepared for such threats. The real question is not if there will be a cyberwar, but when it will occur.
Some may argue that cyberwar is already underway. In fact, considering the daily attacks on the United States and other nations, the first major cyberwar may have started as early as the late 1990s. In the next section, we'll explore some of the most notable "battles" in cyber warfare over the past decade.
Cyberwars Across the Globe
 The 2005 Infocomm security conference held in Singapore
Roslan Rahman/AFP/Getty Images
The 2005 Infocomm security conference held in Singapore
Roslan Rahman/AFP/Getty ImagesThough the Internet has been around for several decades, it remains a relatively young technology. It has, however, proven to be incredibly valuable. Governments, corporations, and individuals quickly embraced Internet technology. Soon, entire industries and government services became reliant on the Internet for their operations. The issue, however, is that overall, the Internet and its connected systems are not very secure. There are numerous ways to exploit weaknesses and breach systems. Internet security has struggled to keep pace with its rapid adoption and usage.
Some people recognized the inherent risks of the Internet quite early. In 1997, the Department of Defense initiated an experiment known as Eligible Receiver. Although many details about the experiment remain classified, the core objective was to determine whether a group of hackers using standard computers and software could breach the Pentagon's computer systems. The findings were unsettling — as John Hamre, the deputy secretary of defense at the time, reported, it took three days before anyone at the Pentagon realized their systems were under attack [source: Frontline].
The group of hackers successfully took control of the Pentagon and national military command systems. In a real-world scenario, this could have led to a shutdown of critical systems. Even more concerning was the possibility that the attackers could have accessed and stolen sensitive information.
In fact, it appears that a real threat successfully did just that a year later. In an incident dubbed Moonlight Maze, someone managed to infiltrate multiple computer systems at the Pentagon, NASA, and other facilities, accessing classified data. U.S. officials uncovered the breach in 2000, two years after it had gone undetected [source: Frontline]. The stolen information included strategic maps, troop movements, and other sensitive materials. Authorities traced the attacks to Russia, but it is still uncertain whether that was the true origin of the breach.
The United States isn't always on the defensive in cyber warfare. The U.S. has actively employed cyber tactics against Iraq and Afghanistan. During the Kosovo war, the U.S. used cyber attacks to undermine Serbia's air defense systems. These attacks manipulated the data the systems generated, causing Serbian forces to receive false information during the air campaign. Security agents are also working to infiltrate terrorist cells and monitor them from a distance.
Recently, cyber warfare played a significant role in the conflict between Russia and Georgia. Hackers targeted Georgian Web servers with a series of distributed denial of service attacks (DDoS). A DDoS involves bombarding a Web server with millions of pings, overwhelming the server until it slows down or crashes. The identity of the attackers remains unknown — it could have been Russian agents, mafia hackers, or even individuals with no connection to the conflict.
And the list doesn't end there. Some believe that North Korea has launched cyber attacks against South Korea. There are also claims that China uses cyber attacks to target Taiwan. The terrorist group Al Qaeda has even declared a cyber jihad against the U.S. In many instances, proving that one nation is actively launching cyber attacks against another is virtually impossible.
What exactly does a cyberwar look like? In the next section, we'll dive deeper into the strategies employed by cyber warriors.
The Eligible Receiver experiment used a technique known as a red team attack, a strategy employed in the security field. A red team is a group that acts as an adversary to test the effectiveness of your defenses. They adopt the tactics that a real enemy might use in an actual attack.
Cyberwar Battle Strategies
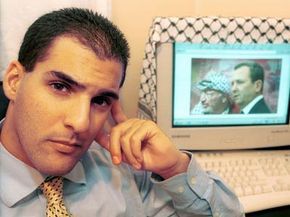 Israel's government enlisted hacker Avi Buzaglo to assist in defending the nation against potential cyber attacks.
Brian Hendler/Liaison/Getty Images
Israel's government enlisted hacker Avi Buzaglo to assist in defending the nation against potential cyber attacks.
Brian Hendler/Liaison/Getty ImagesAlthough there are various cyberwarfare scenarios, in general, strategies can be categorized into two primary groups. Let's delve into each one in detail.
The first main strategy is the Pearl Harbor attack, named after the surprise assault on the naval base at Pearl Harbor, Hawaii, in 1941. This approach involves a large-scale cyber attack targeting critical computer systems. Hackers would infiltrate the systems first, then carry out acts of sabotage, potentially shutting down entire networks or disrupting key utilities like water and fuel pipelines.
Another tactic involves using computer viruses to carry out the attack. Viruses like Code Red, Slammer, and Nimda spread quickly across the Internet. Code Red, for example, directed infected machines to target the White House website. These viruses caused billions of dollars in damage as businesses and governments scrambled to fix systems compromised by the infections. Viruses are an appealing option for hackers due to their low risk and high reward, as it is often difficult to trace the creators behind them.
While Pearl Harbor-style attacks are terrifying enough on their own, some cybersecurity experts are concerned that such cyber attacks could be combined with a physical strike. Imagine the power going out across a city in an instant, followed by explosions in the distance. A coordinated assault like this could not only cause significant damage but would also be an effective psychological weapon. Experts worry that groups like Al Qaeda might be planning strategies involving this combination of cyber and physical attacks.
Another form of cyber assault is more subtle but equally dangerous. Instead of launching an overt attack, the aggressor would infiltrate computer systems and quietly observe. This strategy is about espionage and reconnaissance—gathering intelligence without detection. The gathered information could then be used to target vulnerabilities in the victim's infrastructure.
A hacker who gains access to a system might also sabotage it gradually, avoiding detection. By making small, subtle changes to the system's code, they can degrade its accuracy and reliability over time. This long-term approach may eventually render the system unstable or unresponsive. Although slower to take effect than a Pearl Harbor-style attack, this method is harder to detect and fix, making it more challenging to prevent.
A hacker infiltrating a system might even implant computer viruses. Not all viruses cause immediate damage; some are designed with triggers that can be manually activated later. Others have time-based triggers, set to release the virus on a specific date.
How can countries protect themselves from cyber warfare? Discover more in the following section.
Water and fuel management often relies on System Control and Data Acquisition (SCADA) systems. These systems enable automation by converting cyber commands into physical actions, like opening a valve or turning off a power grid. However, most SCADA systems operate on common software—primarily Microsoft products—that are known to have several vulnerabilities.
Cyberwar Defenses
 In 1999, U.S. President Bill Clinton addressed a conference on the rising threat of cyber terrorism. See more images of the president.
Stephen Jaffe/AFP/Getty Images
In 1999, U.S. President Bill Clinton addressed a conference on the rising threat of cyber terrorism. See more images of the president.
Stephen Jaffe/AFP/Getty ImagesBecause cyber warfare is so different from conventional warfare, the same rules don't apply. A skilled hacker can make an attack nearly impossible to trace. It's easy for a hacker to control a vast network of zombie computers, which are machines infected with malicious software that gives the hacker remote control. The owners of these infected computers may never realize they've been compromised. If a system is attacked by an army of zombie computers, it may be nearly impossible to pinpoint the hacker responsible for the attack.
A key part of preparing for a cyber attack is raising global awareness. The importance of computer security cannot be emphasized enough. A solid mix of the right antivirus software and a cautious approach to online activities can help prevent hackers from obtaining the necessary resources to launch an attack.
Experts like Richard Clark, who served as the former cybersecurity advisor to the U.S., argue that software companies share some of the blame. He has pointed out that these companies often rush products to market without ensuring they've passed rigorous quality control tests. Specifically, he criticized Microsoft for its practices. Microsoft now claims to invest more time and resources to enhance the security features of its products [source: Frontline].
Why release insecure products? The answer is more complex than it seems. Companies face an economic dilemma when deciding whether to spend more time addressing security issues before releasing a product. Lengthening the production cycle means higher costs, which poses a challenge for businesses. Should they raise the price to cover these expenses, potentially hurting consumers? Should they keep prices the same, but absorb the additional costs, risking the interests of investors? Or should they cut salaries to save costs, potentially affecting the workforce? The reality is that focusing more on security will affect a company’s profitability. If the perceived risk of a security breach is low, companies might ignore the threat altogether.
Another factor to consider is that private companies own most of the Internet's infrastructure. Without government regulations, it’s up to these companies to protect their networks. Even Richard Clark has stated that regulation isn't the solution—he argues that it stifles innovation and lowers security standards across industries.
Most sectors and governments employ security professionals who continuously monitor their computer systems. Their job is to detect and respond to probes and attacks. Experts like John Arquilla, associate professor at the Naval Postgraduate School, and John Hamre, CEO of the Center for Strategic and International Studies, have stated that a Pearl Harbor-style cyberattack would likely not cause widespread devastation, partly because we’ve learned how to quickly detect and address attacks [source: Frontline]. Although an attack could still succeed, they suggest that recovery would be relatively fast. Governments and corporations should work to close any security gaps, but a massive attack is unlikely to incapacitate major systems for long. Other experts remain concerned, warning that a well-organized attack could catch us off guard and cause significant economic disruption.
Although it may not be immediately apparent in our daily lives, there is no doubt that cyber warfare is currently happening between various nations and factions across the globe. So, is the age of cyberwar upon us? It might already be in progress.
