We increasingly depend on computers in nearly every part of our daily routines. Because of this, it can be difficult to comprehend how something so familiar and well-established could lead to errors that cost hundreds of millions, or even billions, of dollars.
Still, significant security vulnerabilities affect nearly every device on Earth (yes, even the one you're reading this on), and hastily designed systems have led to fatal outcomes. Let's explore ten instances when computers malfunctioned—or were intentionally sabotaged—in costly, sometimes deadly, manners.
10. Mars Climate Orbiter
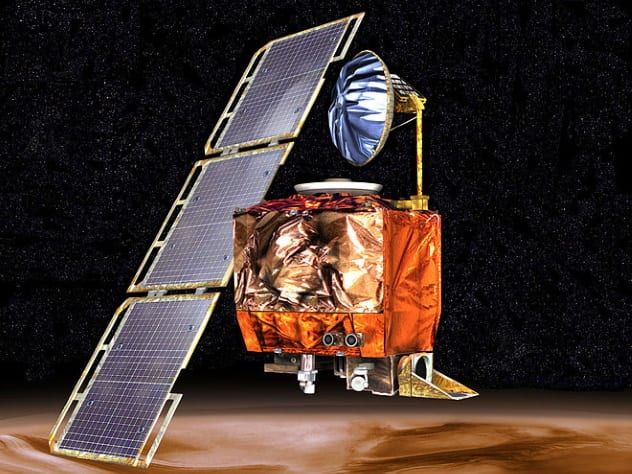
The Mars Climate Orbiter was a small space probe launched on December 11, 1998, by NASA with the goal of entering Martian orbit to study the planet’s atmosphere and provide valuable insights into its climate and surface changes. The launch proceeded as expected, and the probe traveled toward Mars without apparent problems. However, unbeknownst to the mission control team on Earth, the spacecraft was being directed along a path that would ultimately result in the mission's failure.
The orbiter was being guided by various teams, some of whom used metric units while others employed imperial units. This simple unit conversion mistake—combined with a misconfiguration of Lockheed’s computer systems—caused a course correction to send the Mars Climate Orbiter too close to the planet, likely leading it to be burned up and destroyed upon entering the Martian atmosphere.
9. Ariane 5
Ariane 5 is a type of heavy-lift rocket used in Europe. Developed collaboratively by 20 European countries—including Belgium, France, Germany, and the United Kingdom—it has been consistently improved to increase efficiency, reliability, and power, and continues to be in use today.
After its development, the first completed Ariane 5 rocket was placed on the launchpad in preparation for its inaugural flight on June 4, 1996. As the engines ignited on both the core stage and large boosters, the rocket ascended into the sky, quickly gaining speed and rotating faster than its predecessor, the Ariane 4. Unfortunately, this faster-than-expected maneuvering was the very reason for the rocket's failure.
The internal computers and software that monitored speed and orientation aboard the Ariane 5 were carried over from the Ariane 4, but the increased speed of the new rocket caused the computers to experience a “hardware exception” while converting a 64-bit floating point number to a 16-bit integer. In simple terms, the rocket’s enhanced power quickly surpassed the limits of the older systems in just 37 seconds, leading to the numbers flipping from 32,768 to -32,768, which confused the rocket's guidance system. This triggered a sudden downward turn, resulting in a catastrophic breakup and aerial explosion, destroying both the rocket and its payload.
8. Knight Capital Group

Knight Capital was an American-based financial services company, known for buying and trading vast quantities of stocks on the global market. It dominated trading in the United States, controlling approximately 17 percent of NASDAQ transactions.
The company's downfall occurred suddenly on August 1, 2012. That morning, as the stock market opened, Knight Capital's automated trading systems began rapidly buying and selling millions of shares across hundreds of stocks for a span of 45 minutes, until the malfunctioning systems were shut down. Knight Capital was forced to sell the shares back at a loss, resulting in a staggering $440 million deficit—roughly $10 million lost per minute.
A technician had improperly installed new trading software on one of the computers, which caused the malfunction and briefly destabilized the stock market. In the aftermath of the disaster, Knight Capital had to be acquired by another financial firm, Getco, as the company simply didn't have enough funds to continue and needed to be “rescued” by others.
7. Stuxnet

Stuxnet is the name of a malicious software discovered in 2010, believed to have been co-developed by the United States and Israel as a cyberweapon since 2005. Specifically targeting real-world mechanical systems, Stuxnet is widely considered the first known malware designed to cause direct, physical damage.
Stuxnet seems to have primarily been used against Iran’s nuclear program—specifically infiltrating the Natanz nuclear facility, where it infected the computer systems and manipulated machinery in a destructive manner. Remarkably, it appears to have entered through a simple, easily detectable USB drive. Between November 2009 and late January 2010, this malware caused approximately 1,000 nuclear centrifuges—about ten percent of the facility’s total—to violently disintegrate by altering rotor speeds. Stuxnet first increased and then decreased the rotation speed, effectively destabilizing the machines. The resulting damage is thought to have led to a 30-percent reduction in Iran’s nuclear enrichment efficiency—a significant setback to the country’s nuclear ambitions.
6. WannaCry

In May 2017, a global cyberattack was launched that infected Windows-based computers with ransomware. Ransomware is a type of malicious software that encrypts a user's data, rendering it unusable, and demands payment for decryption. WannaCry primarily targeted older Windows systems, like Windows XP, and spread to over 200,000 computers across 150 countries.
The ransom demanded ranged from $300 to $600 per computer. Those who paid the ransom received their data back safely. The United Kingdom’s National Health Service was especially hard-hit, with tens of thousands of computers controlling MRI scanners, surgical equipment, and more being attacked. This led to the postponement of some non-emergency cases while the situation was contained. The total global cost is estimated to reach up to $4 billion, with blame squarely placed on North Korea by the West.
5. Dhahran Patriot Missile Interception

The Patriot missile system, developed by the United States, is a surface-to-air missile system designed to intercept both aircraft and ballistic missiles, provided they are detected and confirmed as threats. It is widely used today by the United States and several of its allies, including Germany. The system was also heavily deployed during the Gulf War of 1991 to protect American troops and aircraft, where it failed due to a known software error.
A Patriot missile system deployed in Dhahran, Saudi Arabia, had been in operation for 100 hours, during which its internal clock drifted by 0.34 seconds. Two weeks prior, Israeli technicians had detected the issue and recommended that the US periodically reboot the system’s computers. However, this suggestion was not followed. On February 25, 1991, an Iraqi-launched “Scud” missile struck a US Army barracks in Dhahran, killing 28 American soldiers. The Patriot system had detected the missile and predicted its next location, but due to the drifting internal clock, the system searched in the wrong place, found nothing, and shut down. As a result, the system failed to intercept the missile, missing an opportunity to save many lives.
4. Meltdown

Meltdown is a vulnerability that affects all Intel CPUs released between 1995 and October 2018, as well as certain ARM processors. Given that Intel CPUs power most of the world’s computers, security experts have labeled this vulnerability as “catastrophic,” with many initially doubting the reports of its existence due to the severity of the issue.
Meltdown exploits the way modern CPUs operate, allowing processes running on a computer to access all data currently being handled by the CPU, bypassing security measures meant to prevent this. The implications are disastrous—an attacker using Meltdown could steal passwords, sensitive financial data, images, and essentially anything else without the user’s knowledge, all while evading antivirus software. Intel and Microsoft have both issued emergency security patches to address the exploit, but these patches reportedly come with a performance hit, ranging from 5 percent to as much as 30 percent. With such widespread impact, the exploit is undeniably destructive.
3. Boeing 737 MAX

The Boeing 737 MAX is a newer iteration of the iconic Boeing 737 series, a narrow-body, twin-engine airliner that has been in service since the late 1960s. Over the years, the 737 has undergone several upgrades to meet the evolving demands of modern aviation. However, it could be argued that the 737 MAX pushed these changes too far.
In an effort to improve fuel efficiency, the 737 MAX was rushed into production, requiring larger engines that couldn’t be mounted in the traditional manner. To solve this, Boeing positioned the larger engines further forward on the wings, creating several changes in the aircraft's flying characteristics. Rather than incur the additional expense of retraining pilots to handle these differences, Boeing introduced a system called MCAS, designed to automatically lower the aircraft’s nose if an excessive angle of attack was detected. However, this software malfunctioned, leading to the crashes of two 737 MAX flights: Lion Air Flight 610 in October 2018 and Ethiopian Airlines Flight 302 in March 2019, both of which resulted in the tragic loss of 346 lives as the MCAS system forced the planes into the ground. Following these accidents, the 737 MAX has been grounded worldwide and is banned from carrying passengers due to ongoing safety concerns.
2. ILOVEYOU
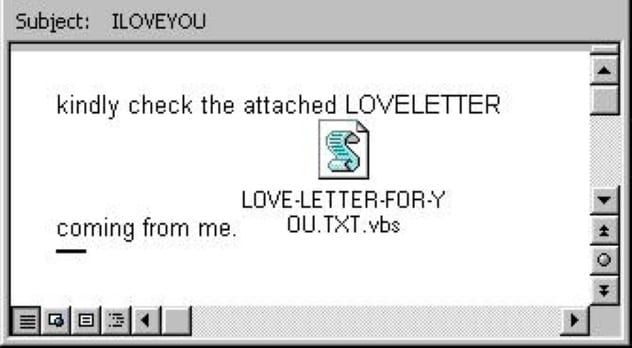
On May 5, 2000, an email titled “ILOVEYOU” was sent to millions across the globe. The message typically contained a line like “Please read the attached LOVELETTER from me” and included an attachment named “LOVE-LETTER-FOR-YOU.TXT.vbs.” Intrigued by the subject, many recipients opened the attachment, unknowingly triggering a destructive script.
The script then began overwriting random files on the user’s computer and automatically forwarded itself to everyone in the recipient’s Microsoft Outlook address book. This viral spread of the malware quickly escalated from the Philippines to Hong Kong, Europe, and the US. The total damage caused by ILOVEYOU is estimated at around $8 billion worldwide, with $15 billion spent on removing it from systems. Approximately 10% of internet-connected computers were affected, with a staggering 50 million infections reported within just ten days.
1. Spectre

Spectre, like Meltdown, is a major security flaw that came to light in 2018, but it’s even more widespread. While Meltdown primarily targeted Intel processors, Spectre affects nearly every computer system by 2019. Some variants of Spectre cannot be adequately fixed through software alone and will require hardware changes, which are currently being rolled out.
Spectre exploits a vulnerability by manipulating a program into accessing seemingly harmless memory, thereby enabling an attacker to read and potentially steal sensitive data without the user’s consent. At present, only a small number of CPUs are immune to this attack, most notably the AMD Zen 2 and Intel Ice Lake processors. Similar to Meltdown, software patches are available but come with performance penalties and may cause unexpected reboots when applied. Unfortunately, it seems unlikely that Spectre will be fully eradicated in the near future, as it requires hardware fixes across all computer systems—and it's probably already affecting you.
