 Carnivore was a surveillance tool created by the FBI. Image Credit: Nes / Getty Images
Carnivore was a surveillance tool created by the FBI. Image Credit: Nes / Getty ImagesYou might have heard of Carnivore, a contentious tool created by the U.S. Federal Bureau of Investigation (FBI) designed to allow the agency access to the online and email activities of suspected criminals. To many, its existence is reminiscent of George Orwell's novel "1984." Despite Carnivore being phased out by the FBI in favor of commercially available eavesdropping software by January 2005, the system that once promised to enhance the FBI's reach in the realm of digital communication monitoring remains fascinating in both its design and its potential use.
Evolution of Carnivorous Practices
Carnivore represented the third iteration of the FBI's online-detection software. While details about the first version remain undisclosed, it is widely believed to have been a commercial tool called Etherpeek.
In 1997, the FBI introduced the second version, Omnivore. According to information from the FBI, Omnivore was designed to monitor e-mail traffic from a particular Internet service provider (ISP), capturing targeted e-mails and saving them to a tape-backup drive or printing them in real time. By late 1999, Omnivore was replaced with the more advanced DragonWare Suite, which enabled the FBI to reconstruct e-mail messages, downloaded files, and even Web pages.
DragonWare was composed of three main components:
- Carnivore - A system based on Windows NT/2000 designed to capture information
- Packeteer - While no official details were provided, it was likely a tool for reassembling packets into readable messages or Web pages
- Coolminer - Similarly, little official information was disclosed, but it was probably used for extracting and analyzing data from the captured messages
As shown, authorities were tight-lipped about the DragonWare Suite, offering no official details on Packeteer and Coolminer, and minimal information about Carnivore. However, it is known that Carnivore was fundamentally a packet sniffer, a common technology that has existed for some time.
Packet Sniffing
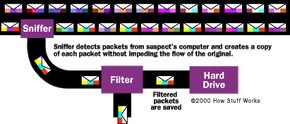
For years, network administrators have relied on packet sniffers to monitor their networks, conduct diagnostic tests, and resolve issues. A packet sniffer is essentially a program that can access all of the information flowing through the network it is connected to. As data is transmitted across the network, the sniffer examines, or "sniffs," each individual packet.
Typically, a computer only processes packets that are specifically directed to it, ignoring the rest of the network's traffic. However, when a packet sniffer is activated, the network interface is switched to promiscuous mode, allowing it to view all packets passing through. The volume of traffic depends heavily on the computer's position in the network. A computer located at a remote branch will only detect a small portion of the network traffic, while a main domain server will capture nearly all of it.
There are generally two ways to configure a packet sniffer:
- Unfiltered - Captures all packets passing through
- Filtered - Captures only those packets that contain specific data elements
Packets containing the targeted data are duplicated as they pass through. Depending on the configuration, these duplicates are stored in memory or on a hard drive. These stored copies can then be examined in detail for particular information or patterns.
When you access the Internet, you're connecting to a network operated by your ISP. This ISP network links to others operated by different ISPs, forming the backbone of the Internet. If a packet sniffer is placed on one of your ISP's servers, it could potentially observe all your online activities, including:
- The websites you visit
- The content you view on those websites
- Your email correspondences
- The contents of the emails you send
- Files you download from websites
- Media streaming activities, such as audio, video, and Internet telephony
- Visitors to your website (if you have one)
In fact, many ISPs use packet sniffers as troubleshooting tools. Furthermore, numerous ISPs retain copies of data, such as e-mails, as part of their backup systems. While Carnivore and its associated programs represented a controversial leap for the FBI, they were not groundbreaking technology.
The Carnivore Process
Now that you have a basic understanding of what Carnivore was, let's explore how it functioned:
The FBI suspects someone of being involved in illegal activities and seeks a court order to monitor the individual's online actions. The court approves the request, granting authorization for a full content-wiretap of e-mail traffic only, and issues the order.
In telephone surveillance, a "content-wiretap" refers to the ability to capture and use all the data in a packet. In contrast, a trap-and-trace allows the FBI to collect only the destination details, such as the sender's e-mail address or the website being visited by the suspect. A variant of this, called pen-register, monitors where e-mails to the suspect originate from or where visits to the suspect's website are coming from.
The FBI contacts the suspect's ISP and requests copies of the backup files documenting the suspect's online actions. The FBI then installs a Carnivore system at the ISP to observe the suspect's activities. The setup includes:
- A Pentium III Windows NT/2000 system equipped with 128 megabytes (MB) of RAM
- A commercial communications software tool
- A custom-built C++ application that works alongside the commercial software to enable packet sniffing and filtering
- A physical lockout system that requires a special passcode to access the computer (This ensures that only the FBI can access the Carnivore system physically.)
- A network isolation device that ensures the Carnivore system remains undetectable by other devices on the network (This safeguards against remote hacking attempts.)
- A 2-gigabyte (GB) Iomega Jaz drive for storing captured data (The Jaz drive uses 2-GB removable cartridges that can be swapped like a floppy disk.)
The FBI sets up the Carnivore software with the IP address of the target, ensuring that Carnivore only collects packets from that specific source. All other packets are disregarded. Carnivore silently copies the packets from the suspect's system without interfering with the network's data flow. After being captured, the packets pass through a filter that retains only the e-mail packets. The software determines the packet's content based on the protocol, such as how e-mail packets use the Simple Mail Transfer Protocol (SMTP). These e-mail packets are then saved to the Jaz cartridge. Every day or two, an FBI agent visits the ISP to swap out the Jaz cartridge. The removed cartridge is placed in a sealed, dated container. If the seal is broken, the person responsible must sign, date, and reseal it — otherwise, it is considered "compromised." The surveillance can continue for no longer than a month without further court approval. Once the monitoring is complete, the FBI retrieves the system from the ISP. The collected data is analyzed using Packeteer and Coolminer, and if sufficient evidence is found, it may be used in legal proceedings against the suspect.
The ISP does not retain customer activity data as part of its backup processes.
The example above demonstrates how the system identifies which packets should be retained.
Prey of the Carnivore
The FBI intended to use Carnivore for specific purposes. In particular, the agency would seek a court order to deploy Carnivore when a person was suspected of:
- Terrorism
- Child pornography/exploitation
- Espionage
- Information warfare
- Fraud
Several critical issues raised significant concern from various parties:
- Privacy - Many considered Carnivore a severe infringement on privacy rights. While there is certainly potential for misuse, the Electronic Communications Privacy Act (ECPA) ensures legal privacy protection for all forms of electronic communication. Any electronic surveillance demands a court order and requires demonstrating probable cause that the individual is involved in criminal activities. Consequently, any use of Carnivore that disregarded ECPA would be unlawful and could even be deemed unconstitutional.
- Regulation - There was widespread concern that Carnivore represented a massive system capable of granting the U.S. government control over the Internet. Achieving this would have required an enormous infrastructure, with Carnivore systems placed at every ISP, including private, commercial, and educational entities. While technically possible for U.S.-based ISPs, this effort could not extend to those operating outside U.S. borders, and any such attempt would have been met with significant opposition.
- Free speech - Some believed that Carnivore was capable of monitoring all content traversing an ISP, scanning for specific keywords like "bomb" or "assassination." Though packet sniffers can indeed be set to search for particular data patterns, the FBI would need probable cause to justify such monitoring. Without it, such surveillance would violate both ECPA and the individual's constitutional right to free speech.
- Echelon - Echelon is a rumored secret network allegedly under development by the National Security Agency (NSA) to intercept and capture international packets containing targeted keywords, such as "bomb" or "assassination." While no concrete evidence confirms Echelon's existence, many confused this rumored system with Carnivore.
All of these concerns made the implementation of Carnivore a challenging endeavor for the FBI. The agency's refusal to disclose the source code and other technical details further fueled public unease. Nevertheless, if used in strict adherence to the ECPA guidelines, Carnivore had the potential to serve as a powerful tool in the fight against crime.
