 Phishing is a prevalent tactic used for online identity theft and the spread of malicious software. This deceptive practice often exploits trusted names like banks and e-commerce sites to gain unauthorized access to personal information.
2005 Mytour
Phishing is a prevalent tactic used for online identity theft and the spread of malicious software. This deceptive practice often exploits trusted names like banks and e-commerce sites to gain unauthorized access to personal information.
2005 MytourMain Points to Remember
- Phishing involves fraudulent attempts to steal sensitive information through fake communications that resemble legitimate institutions such as financial institutions or online stores.
- Phishers carefully plan and execute attacks to gather private and financial details, frequently relying on tactics like forged email addresses and hidden URLs.
- To stay safe, be wary of messages with vague greetings, urgent demands, or immediate action requests, and report any suspicious phishing activity to the relevant authorities.
Imagine checking your e-mail one day and receiving a message from your bank. While you've received emails from them before, this one feels off, especially since it threatens to shut down your account unless you respond right away. How do you react?
This and similar messages are examples of phishing, a form of online identity theft. In addition to stealing sensitive personal and financial information, phishers can also infect computers with malicious software and manipulate individuals into unknowingly participating in illegal activities like money laundering.
Phishing is often associated with e-mail messages that spoof trusted entities like banks, credit card companies, or online retailers such as Amazon and eBay. These messages appear legitimate, aiming to trick victims into divulging their private information. However, email is just one component of a larger phishing scheme.
The process from start to finish includes the following steps:
- Planning. Phishers select their target businesses and figure out how to gather e-mail addresses for their customers. They typically use techniques similar to those employed by spammers, such as mass mailings and address harvesting.
- Setup. After identifying the target business and its customers, phishers develop strategies for sending their fraudulent messages and collecting the stolen data. Most often, this involves crafting fake e-mails and fake websites.
- Attack. This is the stage that most people recognize — the phisher sends a forged message that appears to come from a trustworthy source.
- Collection. Phishers then gather the personal information victims provide through websites or pop-up forms.
- Identity Theft and Fraud. Using the stolen data, phishers make illegal transactions or engage in fraudulent activity. Around a quarter of victims never fully recover from the consequences of the attack [Source: Information Week].
If the phisher plans another attack, he reviews the outcomes of the previous scam, analyzing what worked and what didn’t, and then begins the process anew.
Phishing attacks exploit vulnerabilities in both client-side and server-side security. Despite their high-tech nature, many phishing schemes resemble traditional cons, where the scammer tricks their target into believing they are legitimate and trustworthy.
The term "phishing" was first recorded in 1996. It is widely believed to be a variant of the word "fishing," referring to the act of "fishing for information" [source: Next Generation Security Software].
Phishing Scams
 Mytour
MytourSince most individuals are cautious about sharing sensitive details like their bank account, credit card information, or passwords, phishers must employ advanced tactics to manipulate their victims into surrendering this data. This form of manipulation is known as social engineering.
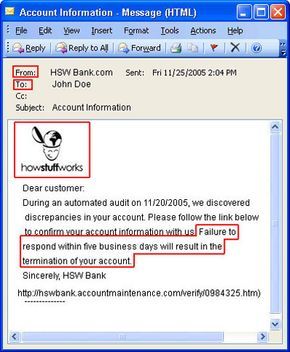
Phishers frequently use authentic company logos and replicate legitimate e-mail messages, replacing the original links with fraudulent ones that lead to fake websites. They also employ spoofed e-mail addresses in the "From:" and "Reply-to" fields and disguise links to appear genuine. Recreating the look of an official communication is just one step in the scam.
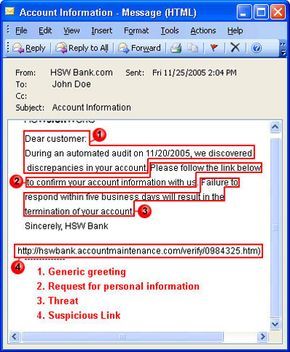
Many phishing messages create a sense of urgency, pushing the victim to act quickly without thinking. These messages often threaten to cancel the victim's account if they don't respond right away. Others falsely claim that a purchase was made in their name, prompting the victim to act swiftly to prevent a loss they never actually incurred, ultimately handing over the sensitive information the phishers seek.
Additionally, many people place their trust in automated processes, assuming they are infallible. This is why many phishing messages claim that an automated audit or system check has detected an issue with the victim's account. Victims are more inclined to believe that a security breach has occurred rather than question the possibility of an error in the automated system itself.
While e-mail is the primary channel used for phishing attacks, scammers also target victims through:
- Instant messages
- Cell phone text (SMS) messages
- Chat rooms
- Fake banner ads
- Message boards and mailing lists
- Fake job search sites and job offers
- Fake browser toolbars
Address Spoofing
 Address spoofing is one of the most prevalent methods phishers employ to gather sensitive information.
Mytour.com
Address spoofing is one of the most prevalent methods phishers employ to gather sensitive information.
Mytour.comAs web browsers and e-mail clients grow more advanced, they also introduce more vulnerabilities that phishers can exploit. As technology improves, so do the tactics used by phishers. For instance, as spam and phishing filters evolve to become more robust, phishers develop increasingly sophisticated methods to bypass them.
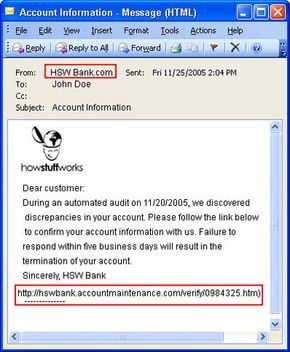
One of the most widely used techniques is address spoofing. Many e-mail applications allow users to manually input their preferred details into the "From" and "Reply-to" fields. While this feature is helpful for managing multiple email accounts, it also makes it easier for phishers to craft messages that appear to originate from trustworthy sources. Additionally, some e-mail servers allow direct connections to the Simple Mail Transfer Protocol (SMTP) port without requiring authentication, enabling phishers to send malicious messages by directly controlling the e-mail server.
Other methods employed by phishers include:
Obfuscated links. These deceptive URLs may appear genuine, but they actually redirect the victim to a fraudulent website. Some common obfuscation methods include:
- Utilizing misspelled versions of the targeted company's URL or registering international domain names (IDNs) to create an imitation of the legitimate website address. Incorporating the company name within an altered domain name.
- Representing the URL in alternative formats, such as hexadecimal code.
- Embedding redirection instructions into what seems like a valid URL.
- Employing HTML to disguise links. For instance, the following link appears to lead to a section about "How Spam Works" discussing zombie machines, but it actually redirects to an entirely different page on zombies: https://computer.Mytour.com/spam4.htm
Graphics. By detecting the victim's e-mail client and browser, phishers can overlay images of address bars and security padlocks, misleading the victim into thinking they are on a secure website when, in fact, they are not.
Popup windows and frames. Malicious popups can appear on the screen, or invisible frames around the webpage can contain harmful code, further compromising the victim's security.
HTML. Some phishing e-mails may appear as plain text but actually contain HTML code with hidden words and commands, allowing the message to bypass anti-spam filters and deceive the recipient.
DNS cache poisoning. Also known as pharming, this occurs when a phisher alters DNS server information, often through interactions with customer service representatives. As a result, individuals attempting to access the spoofed company's website are redirected to a fraudulent site. Pharming is particularly challenging to detect and can impact numerous victims simultaneously.
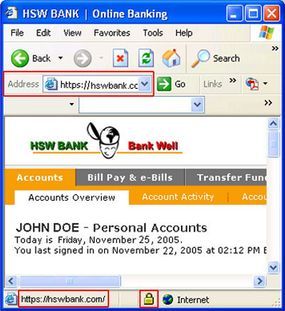
Phishers can deploy proxy computers positioned between the victim and the target website to monitor and record the victim's activities. Additionally, they can exploit weaknesses in a company's website security, injecting malicious code into specific pages. In these cases, there is no need to disguise the links, as the victim remains on a legitimate-looking site when their information is stolen.
Phishers also rely on harmful software in their attacks, such as:
- Key loggers and screen capture Trojans that track and transmit information back to the phisher.
- Remote access Trojans that turn victims' devices into zombie computers, which can then be used to send phishing emails or host phishing websites.
- Bots that maintain fake conversations with victims in chat rooms or coordinate networks of zombie computers.
- Spyware that monitors and records users' online activities, enabling phishers to tailor future attacks.
Anti-Phishing
 Anti-phishing strategies often involve utilizing firewalls and antivirus software to enhance security.
Anti-phishing strategies often involve utilizing firewalls and antivirus software to enhance security.The typical security measures you take, such as deploying a firewall and using antivirus programs, can be effective in defending against phishing. To further protect yourself, consider reviewing SSL certificates on websites and monitoring your own banking and credit card statements for any suspicious activity.
Furthermore, phishers often leave behind certain clues in their emails and websites. When reviewing your email, look out for the following warning signs:
- Generalized salutations like "Dear Customer." Legitimate communications from your bank should include your full name. (Some phishers have advanced to spear phishing, which may involve personalized details.)
- Urgent threats to your account, demanding immediate action, such as "Reply within five business days, or your account will be canceled." Reputable companies generally strive to retain customers and are unlikely to act so hastily.
- Requests for private information. Before phishing became widespread, most companies didn't ask for sensitive details via email or phone.
- Suspicious URLs. Links that appear unusually long, contain an @ symbol, or have spelling errors may indicate phishing. It's safer to manually type the website's URL into your browser than clicking any link in an email.
- Spelling mistakes and grammatical errors.
Fortunately, both businesses and government bodies are actively combating phishing. The U.S. government has mandated that by the end of 2006, banks must implement dual security methods, requiring both passwords and physical devices like tokens or biometric scanners for online transactions [Source: Wired]. Many Internet service providers (ISPs) and software developers now offer phishing toolbars that verify security certificates, identify the registration location of websites, and analyze links. Additionally, these tools allow users to report phishing attempts. Other programs employ visual indicators to confirm the legitimacy of the websites you visit.
Responding to Phishing
If you receive an email that you suspect to be a phishing attempt, do not reply, click any links, or provide personal details. Instead, report the incident directly to the company being impersonated. Use their official website or contact number rather than any links provided in the suspicious email. You should also notify the National Fraud Information Center and the Anti-Phishing Working Group.
If you think you may have unintentionally shared your personal information with a phisher, it is crucial to report the incident to the following:
- The company that was impersonated.
- Any financial institutions such as banks or credit agencies where you may have disclosed sensitive details.
- At least one of the three major credit reporting agencies (Equifax, Experian, and TransUnion).
- Your local police department.
- The Federal Trade Commission.
- The Federal Trade Commission and The Federal Bureau of Investigation (FBI) through the Internet Crime Complaint Center.
If you suspect a website has been spoofed, it's essential to change your passwords for that site. Additionally, if you use the same password elsewhere, be sure to update those accounts as well.
- In August 2005, there were 13,776 phishing attacks linked to 5,259 websites.
- These attacks targeted 84 businesses, with three companies receiving 80 percent of the attacks.
- 85 percent of the attacks were aimed at banks and other financial institutions.
- Phishers were able to obtain personal information from up to 5 percent of their targets.
- 57 million U.S. Internet users have received at least one phishing email, and up to 1.7 million have shared their personal details with the attackers. Source: NGS Software and AntiPhishing.org
