 One method of biometric identification involves scanning the iris. Francesco Carta fotografo / Getty Images
One method of biometric identification involves scanning the iris. Francesco Carta fotografo / Getty ImagesPicture yourself as James Bond, tasked with infiltrating a secret lab to neutralize a lethal biological threat and rescue humanity. However, before you can proceed, you must bypass an advanced security system. This system demands more than a simple key or password—it requires the villain's irises, voice, and hand geometry to grant access.
This situation, minus the life-threatening weapon, could easily occur during a typical workday. Airports, hospitals, hotels, supermarkets, and even Disney theme parks are increasingly adopting biometrics—technology that verifies identity through physical or behavioral characteristics—to enhance security measures.
This article explores biometric authentication systems that utilize handwriting, hand geometry, voiceprints, iris patterns, and vein structures. It also delves into why an increasing number of businesses and governments are adopting biometric technologies like facial and voice recognition systems. Perhaps we'll even uncover whether Q's counterfeit contact lenses, voice recordings, and silicone hand could truly enable James Bond to infiltrate the lab and save the world.
The Cutting-Edge Security of Biometric Data
Every day, you rely on basic security measures—using a key to enter your home or logging into your computer with a username and password. You’ve likely also faced the frustration of losing your keys or forgetting a password. Beyond the inconvenience, there’s the risk that someone else could find and misuse them, pretending to be you.
Biometrics shifts the focus from what you possess (like a key) or what you know (like a password) to who you are for identification. This technology encompasses physical traits (such as fingerprints and facial features) and behavioral patterns (like voice recognition). Unlike traditional methods, your biological and behavioral traits are nearly impossible to lose, forget, or replicate, making them a more secure and reliable option.
 Biometrics relies on distinct characteristics, such as iris patterns, to verify identity.
Photo courtesy Iridian Technologies
Biometrics relies on distinct characteristics, such as iris patterns, to verify identity.
Photo courtesy Iridian TechnologiesHow Biometric Data is Processed and Stored
While biometric systems may appear complex, they all operate using three fundamental steps:
- Enrollment: During your initial interaction with a biometric system, it collects basic details such as your name or ID number. It then captures a digital representation of your unique trait, whether it’s a fingerprint, voice sample, or iris scan.
- Storage: Unlike the dramatic portrayals in films, most systems don’t retain the full image or recording. Instead, they convert your trait into a coded format or graphical representation. In some cases, this data is stored on a smart card that you keep with you.
- Comparison: When you use the system again, it matches the trait you provide with the stored data. Based on this comparison, it either verifies or denies your identity.
 This laptop includes a built-in fingerprint scanner, making biometric security accessible for personal use.
This laptop includes a built-in fingerprint scanner, making biometric security accessible for personal use.All biometric systems rely on the same three core components:
- A sensor designed to capture the specific trait used for identification
- A computer responsible for processing and storing the collected data
- Software that evaluates the trait, converts it into a graphical or coded format, and handles the comparison process
Biometric security systems, such as the fingerprint scanner featured on the IBM ThinkPad T43 (right), are increasingly popular for personal use. Explore other Mytour articles to discover more about facial recognition and fingerprint scanning.
Handwriting Analysis
 This Tablet PC includes a system for verifying signatures.
Photo courtesy Softpro
This Tablet PC includes a system for verifying signatures.
Photo courtesy SoftproAt first glance, relying on handwriting for identification might appear unreliable. After all, with some effort, many individuals can mimic another person's handwriting. It might seem simple to obtain a copy of someone's signature or password and then practice forging it.
However, biometric systems go beyond merely analyzing the shape of your letters; they focus on the process of writing itself. They measure factors like the pressure applied, the speed of writing, and the rhythm of your strokes. Additionally, they track the order in which you form letters, such as whether you dot your 'i's and cross your 't's as you write or after completing the word.
These characteristics, unlike the basic shapes of letters, are incredibly challenging to replicate. Even if someone obtained a copy of your signature and attempted to trace it, the system would likely reject the forgery.
Sensors in a handwriting recognition system may include a touch-sensitive writing pad or a specialized pen equipped with sensors that capture details like angle, pressure, and direction. The software then converts the handwriting into a graphical format, accounting for natural variations in a person's writing style over time.
Hand and Finger Geometry Analysis
 A scanner designed for hand geometry recognition
Photo courtesy Ingersoll-Rand
A scanner designed for hand geometry recognition
Photo courtesy Ingersoll-RandWhile hands and fingers are unique, they are not as distinctive as other biometric traits like fingerprints or irises. As a result, hand and finger geometry readers are commonly used in businesses and schools for authentication rather than identification. For instance, Disney theme parks employ finger geometry scanners to allow ticket holders access to various park areas. Similarly, some companies use hand geometry systems as a replacement for traditional timecards.
Hand and finger geometry systems rely on a combination of a digital camera and light. To use the system, you place your hand on a flat surface, positioning your fingers against guide pegs to ensure precision. A camera then captures one or more images of your hand and its shadow, analyzing the length, width, thickness, and curvature of your hand or fingers. This data is converted into a numerical template for identification.
Hand and finger geometry systems have their advantages and drawbacks. Because hands and fingers are less unique than fingerprints or irises, some users feel these systems are less intrusive. However, changes in hand shape due to injury, weight fluctuations, or arthritis can affect accuracy. Some systems adapt by updating user data to account for minor daily variations.
For applications requiring higher security, biometric systems utilize more unique traits, such as voice patterns.
Voice Recognition
 Speaker recognition systems utilize spectrograms to visually represent human voices.
Photo courtesy Richard Horne
Speaker recognition systems utilize spectrograms to visually represent human voices.
Photo courtesy Richard HorneYour voice is distinct due to the structure of your vocal tract and the way your mouth moves when you speak. To register with a voiceprint system, you either repeat specific words or phrases it requires, or provide a lengthy speech sample, allowing the system to recognize you regardless of the words you use.
When people imagine voiceprints, they often picture wave patterns displayed on an oscilloscope. However, voiceprint systems rely on sound spectrograms, not waveforms. A spectrogram is a graph that plots sound frequency on the vertical axis and time on the horizontal axis. Different speech sounds produce distinct patterns within the graph, and colors or shades of grey represent the acoustic properties of the sound. This tutorial provides detailed insights into spectrograms and how to interpret them.
Some organizations employ voice recognition technology to allow individuals to access information or grant authorization remotely. Instead of requiring physical presence at an iris scanner or hand geometry reader, users can authorize actions simply by making a phone call.
However, some systems, especially those operating over the phone, can be bypassed using a recording of an authorized person's password. To counter this, certain systems use multiple randomly selected voice passwords or rely on general voiceprints rather than specific word-based prints. Others incorporate technology that identifies the distortions introduced during recording and playback.
For certain high-security systems, relying on a single identification method isn't sufficient. Layered systems integrate a biometric approach with additional measures like keycards or PINs. Multimodal systems, on the other hand, combine multiple biometric techniques, such as pairing an iris scanner with a voiceprint system for enhanced security.
Iris Scanning Technology
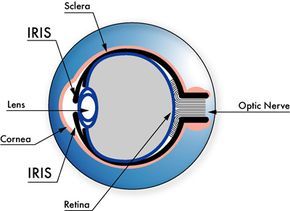 Anatomy of the eye
Photo courtesy Iridian Technologies
Anatomy of the eye
Photo courtesy Iridian TechnologiesWhile iris scanning may appear futuristic, the technology relies on a straightforward CCD digital camera. It captures a detailed, high-contrast image of the iris using both visible and near-infrared light. Near-infrared light renders the pupil extremely dark, simplifying the process for the computer to distinguish between the pupil and the iris.
When using an iris scanner, the camera either auto-focuses or guides you via a mirror or audible cues to ensure proper positioning. Typically, your eye should be 3 to 10 inches from the camera. Once the image is captured, the computer identifies and analyzes key features of the iris.
- The center point of the pupil
- The boundary of the pupil
- The outer edge of the iris
- The eyelids and eyelashes
The system then examines the unique patterns within the iris and converts them into a digital code.
 An advanced iris scanning device
Photo courtesy Iridian Technologies
An advanced iris scanning device
Photo courtesy Iridian TechnologiesIris scanners are increasingly used in high-security environments due to the extraordinary uniqueness of each person's eyes (the probability of two iris codes matching is 1 in 10^78 [ref]). They also provide over 200 biometric data points for comparison, far exceeding the 60 to 70 points typically used in fingerprint analysis.
The iris is both visible and well-protected, and it remains stable over time, making it an excellent choice for biometric identification. Even after eye surgery, most individuals' irises remain unchanged, and blind individuals can use iris scanners as long as their irises are intact. Eyeglasses and contact lenses generally do not affect the accuracy of the scans.
Vein Pattern Recognition
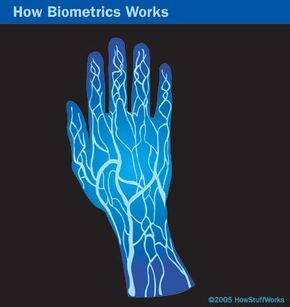 Vein scanners utilize near-infrared light to capture the unique patterns of a person's veins.
Vein scanners utilize near-infrared light to capture the unique patterns of a person's veins.Veins are ideal for identity verification. Similar to irises and fingerprints, each person's vein patterns are entirely unique. Even twins have different vein structures, and the veins on the left and right sides of a person's body differ as well. Since many veins are not visible through the skin, they are nearly impossible to forge or alter. Additionally, vein patterns remain relatively stable over time, even as a person ages.
To use a vein recognition system, you place your finger, wrist, palm, or the back of your hand on or near the scanner. A camera captures a digital image using near-infrared light. The hemoglobin in your blood absorbs this light, making veins appear dark in the image. The software then generates a reference template based on the shape and position of the vein structure, similar to other biometric authentication methods.
Vein geometry scanners are entirely different from medical vein scans used in hospitals. Medical vein scans often involve radioactive particles, while biometric security scans use harmless light similar to that emitted by a remote control. For more details on infrared imaging, NASA provides extensive information.
Privacy Issues and Concerns
Some individuals oppose biometric authentication due to cultural or religious beliefs. Others envision a scenario where surveillance cameras identify and monitor them in public spaces, tracking their activities and purchasing habits without permission. They question whether companies are exchanging biometric data as they do with email addresses and phone numbers. Concerns also arise about the existence of a massive global database containing sensitive information about everyone and whether such data is adequately protected.
Currently, modern biometric systems lack the capacity to store and organize data on every individual worldwide. Most systems retain only a small amount of information about a limited number of users. They typically do not store actual recordings or representations of a person's traits—instead, they convert the data into a coded format.
Most biometric systems are designed to operate in specific locations, such as office buildings or hospitals. The data stored in one system is not necessarily interchangeable with others, although efforts are underway to standardize biometric information across platforms.
Beyond privacy concerns, critics highlight several issues with biometrics, including:
- Over-reliance: The belief that biometric systems are infallible might cause individuals to neglect basic security measures and fail to safeguard the system's data.
- Accessibility: Certain systems may not be suitable for specific groups, such as the elderly or individuals with disabilities.
- Interoperability: During emergencies, agencies using different systems may face delays if they are unable to share data due to incompatibility.
