 The Fujitsu GeoStream R980, a powerful industrial router. Check out the Internet connection images to discover different ways to access the web. Photo courtesy of Newstream.com.
The Fujitsu GeoStream R980, a powerful industrial router. Check out the Internet connection images to discover different ways to access the web. Photo courtesy of Newstream.com.The Internet stands as one of the most significant communication advancements of the 20th century. It enables instantaneous e-mail exchanges between people worldwide and allows access to various resources, such as articles on Mytour.com. Naturally, none of this would be possible without the router, raising the fundamental question: What is the role of a router?
We’re all familiar with the many elements of the Internet that reach our homes and offices—the web pages, e-mails, text messages, downloaded files, and streaming content that make the Internet such a dynamic and invaluable resource. However, none of these components would ever reach your device without the router. In this article, we aim to clarify exactly what a router does and emphasize its critical role in making the Internet possible.
The Function of Wired and Wireless Routers
When you send an e-mail to a friend across the country, how does the message reach your friend's computer instead of one of the millions of others worldwide? Much of the process that ensures the message arrives at the right destination is handled by routers. These critical devices manage the flow of messages between networks, rather than within them.
Let's examine what a basic router might do. Picture a small company that creates animated 3-D graphics for local television stations. The company has 10 employees, with four working as animators and the rest in sales, accounting, and management. The animators frequently need to exchange large files as part of their projects, which they do over a network.
When one animator sends a file to another, the file is so large that it takes up most of the network’s bandwidth, slowing down the network for other users. This issue arises from how Ethernet functions. Every packet of data sent from one computer is visible to all other computers on the local network. Each machine then checks the packet and determines if it’s addressed to it. While this keeps the network simple, it can lead to performance problems as the network expands or becomes busier.
To prevent the animators' work from disrupting the office staff, the company sets up two distinct networks—one for the animators and another for the rest of the staff. A wired router connects these networks and also links both to the Internet.
Directing Traffic
The router is the only device that sees every message sent by any computer on either of the company's networks. When the animator in our example sends a huge file to another animator, the router looks at the recipient's address and keeps the traffic on the animator's network. However, when an animator sends a message to the bookkeeper asking about an expense-account check, then the router sees the recipient's address and forwards the message between the two networks.
One of the tools a router uses to decide where data packets should go is a configuration table. A configuration table is a collection of information, including:
- Information on which connections lead to particular groups of addresses
- Priorities for connections to be used
- Rules for handling both routine and special cases of traffic
A configuration table can be as simple as a half-dozen lines in the smallest routers, but can grow to massive size and complexity in the very large wired routers that handle the bulk of Internet messages.
Delivering Information to Connected Devices
A router performs two distinct yet interconnected tasks:
- The router ensures that data is only sent to where it's necessary, preventing valuable resources from being wasted on irrelevant connections.
- The router guarantees that the information successfully reaches its correct destination.
In carrying out these essential roles, the router is indispensable for network management. It connects two separate networks, enabling data to flow between them and, in some instances, converting protocols to ensure smooth communication. Additionally, it acts as a shield, safeguarding each network from the other, ensuring that one network's traffic doesn't spill over into the other unnecessarily.
As the number of interconnected networks increases, the router’s traffic handling configuration grows, requiring greater processing power. Despite this expansion, the router's fundamental operation and purpose remain unchanged.
Sending Data Packets
Data transmitted over the Internet, whether it's a Web page, a downloaded file, or an e-mail message, follows a packet-switching network system. This system breaks down the data into packets, each roughly 1,500 bytes in size. Each packet is wrapped with details such as the sender’s and receiver’s addresses, its place in the larger message, and instructions for ensuring that the packet is delivered without errors.
Each packet of data is routed to its destination through the most efficient path available. This route could be shared by some, all, or none of the other packets in the message. The packet-switching model for data networks has two key benefits:
- The network is capable of distributing the processing load evenly across various devices, dynamically adjusting every millisecond.
- If one device encounters a problem during message transmission, packets can be rerouted to avoid the issue, ensuring the full message is still delivered intact.
The Journey of Data Packets
The routers that form the backbone of the Internet are capable of adjusting the routes that data packets take, as they examine the metadata surrounding the packets. These routers communicate with each other about network conditions like delays and congestion. However, not all routers perform the same tasks. Routers vary in size and capability. For example:
- If you've set up Internet connection sharing between two Windows 98 computers, one of the computers (the one with the Internet connection) functions as a basic router. In this case, the router's role is minimal — it only checks if the data is meant for one computer or the other, and it operates quietly in the background, without impacting other programs you may be running.
- Medium-sized routers, like those used to connect small office networks to the Internet, perform additional tasks. These routers often enforce security rules to protect the office network from potential attacks. They handle enough traffic to be stand-alone devices, as opposed to software running on a server.
- The largest routers, used to manage data at major Internet traffic hubs, handle millions of packets every second. These routers work to optimize the network configuration. They are large, independent systems more akin to supercomputers than typical office servers.
Identifying a Local Area Network
A key responsibility of any router is determining when a packet stays within its local network. This is done using a mechanism called a subnet mask. The subnet mask resembles an IP address and is often displayed as "255.255.255.0." It tells the router that any messages where both the sender and receiver share the first three segments of their IP addresses are on the same network and should not be sent to another network.
For instance: If a computer at address 15.57.31.40 sends a request to a computer at 15.57.31.52, the router, upon inspecting the packets, notices that the first three groups of numbers (15.57.31) match for both the sender and the receiver. Therefore, it keeps the packet within the local network. (You’ll explore how these addresses function in more detail in the next section.)
Knowing Where to Send Data
Routers are one of several types of devices that make up the "plumbing" of a computer network. Hubs, switches and routers all take signals from computers or networks and pass them along to other computers and networks, but a router is the only one of these devices that examines each bundle of data as it passes and makes a decision about exactly where it should go. To make these decisions, routers must first know about two kinds of information: addresses and network structure.
When a friend mails a birthday card to be delivered to you at your house, he probably uses an address that looks something like this:
The address has several pieces, each of which helps the people in the postal service move the letter along to your house. The ZIP code can speed the process up; but even without the ZIP code, the card will get to your house as long as your friend includes your state, city and street address. You can think of this address as a logical address because it describes a way someone can get a message to you.
Virtual Addresses
Every device connected to a network, whether it's a local office network or the vast Internet, carries a unique physical address. This address is tied to the device itself, and it identifies it as a part of the network. For example, a network interface card (NIC) in your desktop computer carries a physical address, which is stored in a dedicated memory location.
This physical address, often referred to as the MAC address (Media Access Control), is composed of two segments, each consisting of 3 bytes. The first half of the address identifies the manufacturer of the NIC, while the second half represents the NIC’s unique serial number.
What's interesting is that a single device can possess multiple logical addresses simultaneously. Much like your own home address, telephone number (or multiple numbers), and email address are all used to receive different types of communication, each serving a distinct purpose. These are simply channels for different kinds of messages, functioning within different 'networks'.
In the same way, computer networks employ logical addresses. It's entirely possible to use multiple addressing schemes or protocols across various networks at the same time. For example, if you're browsing the Internet (and if you're reading this, you are), you're using an address that belongs to the TCP/IP network protocol. Additionally, if you have a local network set up for sharing files between family computers, you may also be using the Microsoft NetBEUI protocol.
Physical Network Addresses
In most cases, you won't directly encounter the MAC address of your devices, as it's managed automatically by the software that facilitates network communication. This software ensures that the MAC address gets matched to a logical address, which is what the network uses to direct data to your device.
If you're curious to check the MAC address and logical address being used by the Internet Protocol (IP) on your Windows computer, Microsoft provides a handy tool for this. Open the "Start" menu, select "Run," and type WINIPCFG (or IPCONFIG/ALL for Windows 2000/XP). After the gray window pops up, click on "More Info."
You'll find a lot of details in this window, some of which will change depending on how your Internet connection is set up. The MAC address displayed is that of the network adapter being queried by the program. The IP address is the logical address assigned to your connection by your ISP or network administrator. It also shows the addresses of other servers, including the DNS servers that handle the names of Internet sites.
Once you're done reviewing the information, click OK. Be cautious about sharing your computer's information with others. With your address and the right tools, a malicious individual could, in some cases, gain unauthorized access to your personal data or even take control of your system through a "Trojan Horse" program. And let's not even get started on the dangers of malware and ransomware!
Understanding Networking Protocols
The primary function of a router is to determine the appropriate destination for information intended for your computer. Just like a postal worker can route a birthday card to your address without knowing the exact location, routers forwarding emails don’t need your computer’s MAC address. They simply ensure the message reaches its destination.
Routers are designed to recognize the most commonly used network protocols. This means they understand the address format, the number of bytes in each data packet sent through the network, and how to ensure all packets reach their destination and are properly reassembled. Routers on the Internet’s main "backbone" process millions of packets every second, ensuring smooth data flow.
In a modern network, an email is split into smaller packets. These packets are sent separately and reassembled once they arrive at their destination. Since each packet can take a different route, similar to a train passing through various switches, this type of network is called a packet-switched network.
Tracking a Message
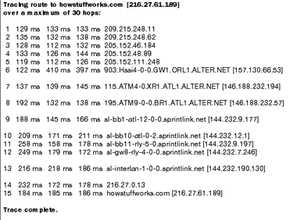 A report on the route trace.
A report on the route trace.If you’re using a Windows-based system, you can easily find out how many routers are involved in your Internet traffic with a tool that's already installed on your computer. This tool is called Traceroute, which precisely describes its function — it tracks the path a packet of information takes from your computer to another one connected through an Internet service provider.
You can use Traceroute to check how many routers are between your computer and any other system you know by name or IP address. It can be fascinating to see how many hops it takes to reach systems beyond your own country. For example, I tried to determine how many routers were between my machine and the BBC’s web server. The result was this:
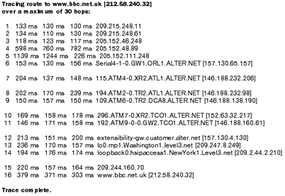 How many routers are needed to connect the U.S. to the BBC?
How many routers are needed to connect the U.S. to the BBC?It’s surprising that it took just one additional step to access a Web server across the Atlantic, compared to reaching one two states away!
The Wireless Router and Beyond
The era of relying on ethernet cables has ended! Routers have evolved significantly in recent years, fueled by the ever-growing demand for faster internet speeds, wider coverage, and more stable connections. Today’s wireless routers offer much more than simply connecting devices to the internet.
Now equipped with cutting-edge features like dual-band or even tri-band capabilities, modern routers can operate on multiple frequencies at the same time. This innovation reduces interference and enhances the ability to support more devices, all without sacrificing connection quality.
Speedier Internet Connections
Packet-switched networks for multiple devices are becoming more flexible than ever. The adoption of the latest Wi-Fi standards, like Wi-Fi 6 (802.11ax), represents a major turning point in wireless technology. Wi-Fi 6 routers deliver higher data rates, greater capacity, and improved performance in environments with many devices, along with better power efficiency for connected devices.
Moreover, the incorporation of Mesh networking technology has transformed the home Wi-Fi experience. By linking multiple router nodes to provide full Wi-Fi coverage across a home, Mesh systems eliminate dead zones, ensuring a consistent and powerful Wi-Fi signal throughout larger living spaces.
Stronger Network Security
The development of wireless routers is also evident in their enhanced security features. In response to rising cybersecurity threats, modern routers are now equipped with advanced security protocols like WPA3, offering cutting-edge encryption for safer connections.
Additionally, many routers now come with integrated VPN support, parental control features, and the ability to manage network access through mobile apps, making it easier and more convenient for everyday users to handle network management. This shift not only showcases technological progress but also emphasizes a move toward more user-friendly designs, catering to the growing dependence on connected devices in modern life.
